What is Tailgating? Definition, Examples & Prevention
IT Governance
JULY 27, 2023
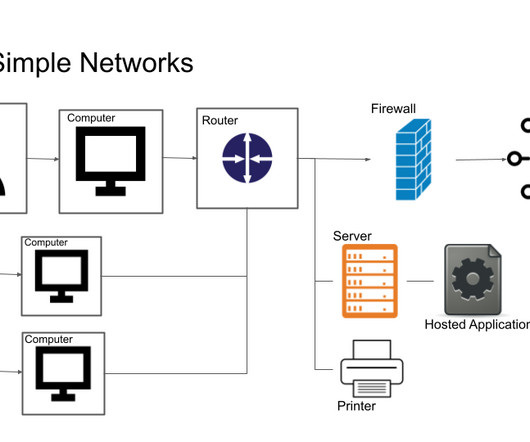
In those cases, video surveillance is a helpful tool. Definition, Examples & Prevention appeared first on IT Governance UK Blog. There are some industries where employees are required to move regularly between public and employee-only spaces, and it would hinder business if they were forced to constantly lock or unlock doors.








































Let's personalize your content