Australian Police Arrest Alleged Head of Ghost Encrypted App
Data Breach Today
SEPTEMBER 18, 2024
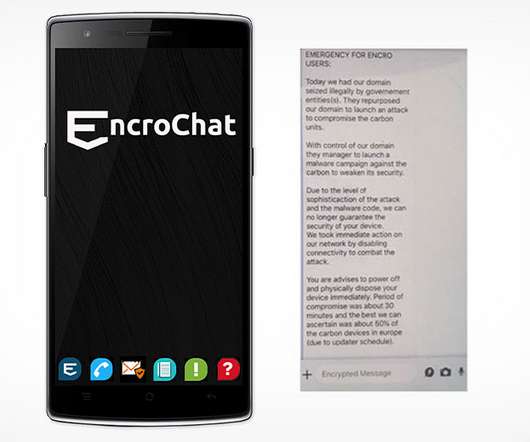
International Law Enforcement Dismantles End-to-End Encrypted Messaging Service An international law enforcement operation dismantled the Ghost encrypted messaging service in a takedown that resulted in the arrest of 51 suspects across three continents including alleged members of the Italian Mafia and motorcycle gangs.















































Let's personalize your content