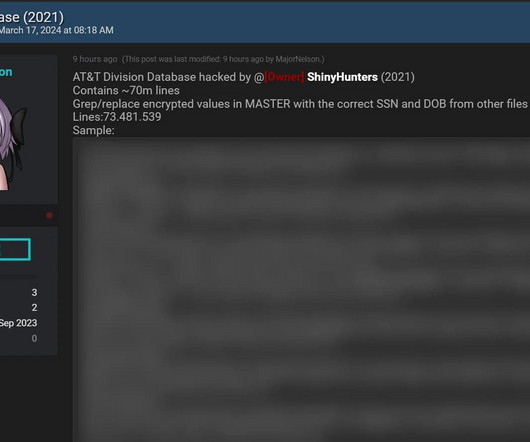
After 70M Individuals' Data Leaks, AT&T Denies Being Source
Data Breach Today
MARCH 19, 2024
Dataset Leaked for Free; ShinyHunters Cybercrime Gang First Advertised It in 2021 Data breach blast from the past: Data pertaining to 70 million individuals that the ShinyHunters gang claimed were AT&T customers has been leaked via a hacking forum, three years after criminals first offered it for sale. AT&T said the information didn't appear to have been stolen from its systems.


































Let's personalize your content