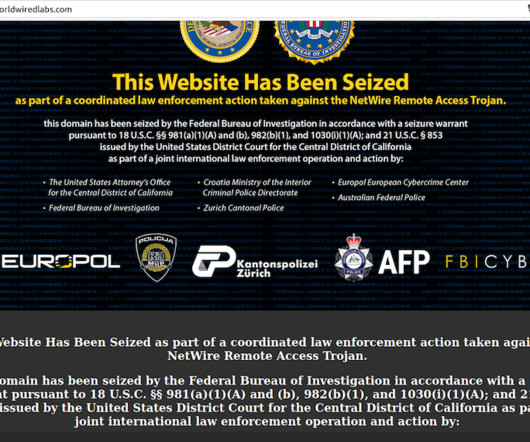
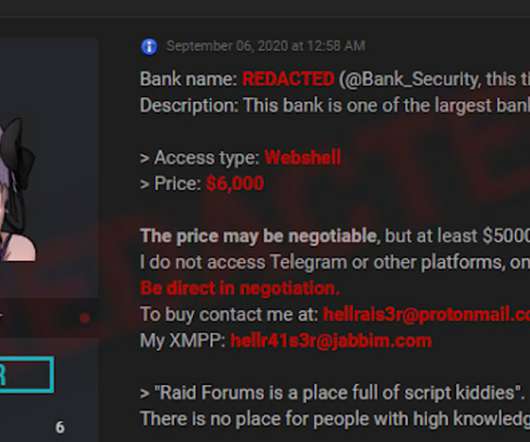
Microsoft: Russian Hackers Had Access to Executives' Emails
Data Breach Today
JANUARY 20, 2024
Computing Giant Says Hackers Did Not Access Customer Data or Production Systems Russian state hackers obtained access to the inboxes of senior Microsoft executives for at least six weeks, the computing giant disclosed late Friday afternoon.












































Let's personalize your content