Multifactor Authentication Shouldn't Be Optional
Data Breach Today
JULY 11, 2024
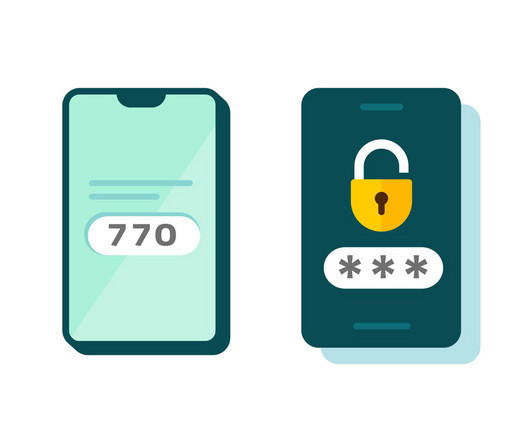
Cloud Customers Should Demand More Security From Providers The theft of terabytes of Snowflake customers' data through credential stuffing hacks highlights how multifactor authentication shouldn't be optional for safeguarding accounts.
















































Let's personalize your content