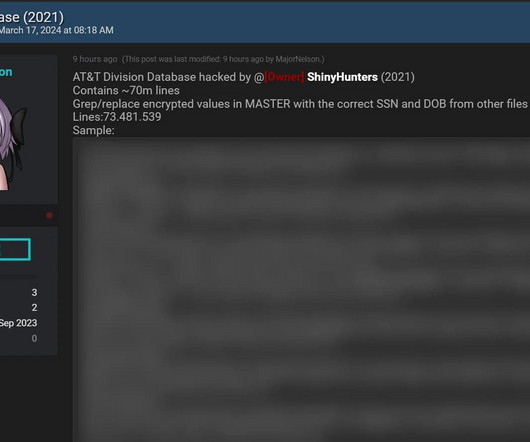
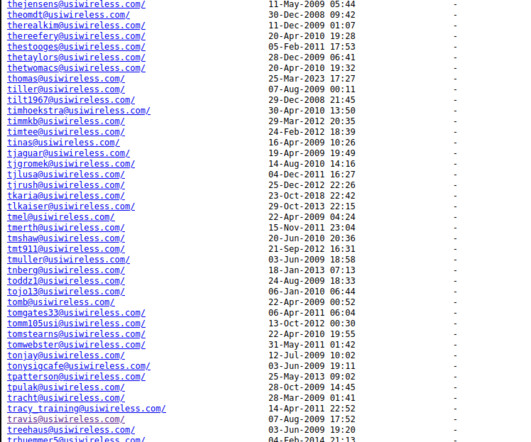
Change Healthcare's Breach Costs Could Reach $2.5 Billion
Data Breach Today
JULY 17, 2024
Costs Have Already Hit $2 Billion, Parent Company UnitedHealth Group Reports Fallout from the February ransomware hit on Change Healthcare, including the theft of data pertaining to up to one-third of Americans, has so far led to $2 billion in costs and may yet reach $2.5 billion, says parent company UnitedHealth Group.







































Let's personalize your content