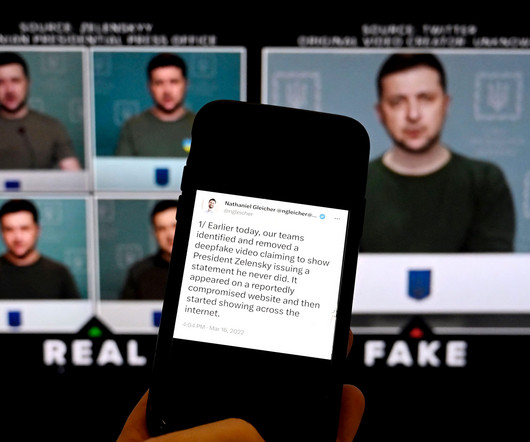
Ransomware Actors Steal Australian Courts' Video Recordings
Data Breach Today
JANUARY 3, 2024
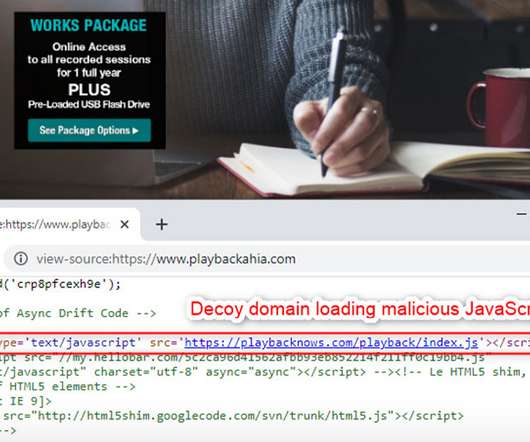
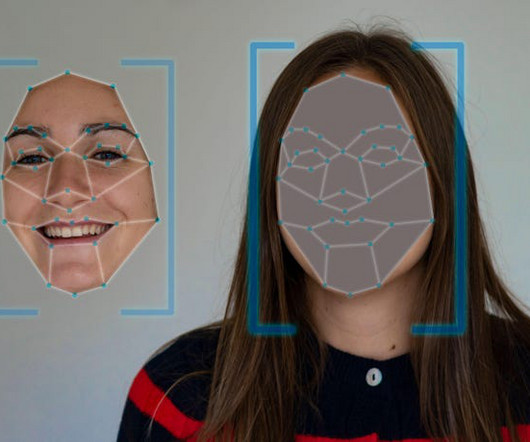
Hackers Lock Up Recordings of Court Hearings to Extort Victoria's Court System The court system of Victoria said it had experienced a serious cybersecurity incident in late 2023 that gave hackers access to video recordings of proceedings at multiple courts, including the Supreme Court and the County Court. The hack took place on Dec.










































Let's personalize your content