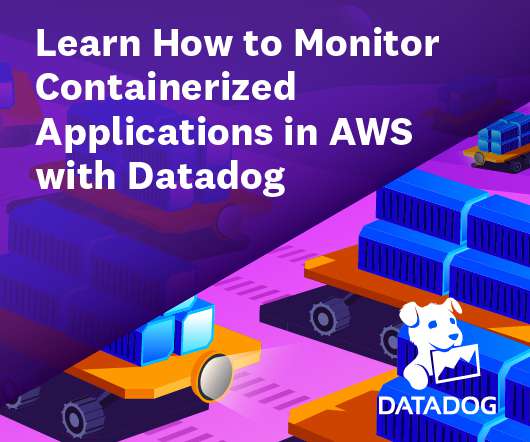
How to secure data and integrate applications in a hybrid cloud environment
Data Breach Today
JULY 25, 2024
Simplifying your transition to a hybrid cloud environment while ensuring data security and app integration When you move to a hybrid cloud environment consideration must be given to how data is secured and synchronized during and after the transfer.













































Let's personalize your content