AI and AI policy top the agenda at CILIP Supplier Forum
CILIP
MARCH 4, 2024
In addition to the 'Developing your AI policy' workshop, case studies were presented from both sides of the sector, an employer and an educator.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

IT Governance
FEBRUARY 25, 2019
There are tons of events across the UK each year , where you can listen to keynote presentations, take part in roundtables and workshops, and network. Find out more about the ISO27001 Certified ISMS Foundation Training Course >> The post How to start your career in cyber security appeared first on IT Governance Blog.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CGI
DECEMBER 10, 2014
A case study on the use of iBeacon technology at a major theme park. With the new app, context-based messages are automatically sent to everyone approaching the park with instructions how to get in as quickly as possible. A table of case study on the use of iBeacon technology at a major theme park. Special events.
Security Affairs
OCTOBER 15, 2021
Experts demonstrated their attack technique with multiple case studies in real-world scenarios. . The team also demonstrated also how to exfiltrate data from kernel memory using simple Spectre gadgets in the Linux kernel. They monitored kernel activity (e.g. Pierluigi Paganini. SecurityAffairs – hacking, cyber security).

Thales Cloud Protection & Licensing
APRIL 18, 2023
You can experience customer and partner presentations and learn more from one-on-one conversations with Thales experts. By attending our live sessions at the Thales booth, you will learn how to: Discover and classify your data wherever it resides. Sarah will also present on FIDO2 Passkeys and the Future of Passwordless.

Security Affairs
APRIL 4, 2019
The platform was presented at the RSA Conference in San Francisco on Tuesday by Rob Joyce, former head of the NSA’s elite hacking team and now White House cybersecurity coordinator, Joyce has presented the code-analysis suite, he remarked the absence of backdoors. There is no backdoor in Ghidra,” he announced.

Elie
JULY 26, 2017
In this talk, we will present our methodology to assess "secure" USB devices both from the software and the hardware perspectives. We will demonstrate how this methodology works in practice via a set of case-studies.
CILIP
JULY 3, 2020
Facet Publishing announce the release of Resource Discovery for the Twenty-First Century Library: Case studies and perspectives on the role of IT in user engagement and empowerment, edited by Simon McLeish. New book tackles the challenges of discovery in the (post-Google) era. Noting the book?s 64.95 | hardback: 9781783301393| ?129.95

CILIP
JULY 31, 2019
Putting Library Assessment Data to Work takes common sources of data that academic libraries will already be collecting, and presents simple qualitative and quantitative techniques that can be used to evaluate and assess their services, both in detail and overall.

eSecurity Planet
FEBRUARY 2, 2024
Make sure your security and IT teams are aware of every connected device so your business knows how to best protect its networks and sensitive data from vulnerabilities and threat actors. Teslas Get the Spotlight in Recent Ethical Hacking Efforts Researchers have discovered multiple vulnerabilities within Teslas since March 2023.

The Schedule
MARCH 3, 2021
Mark your calendars for April 7th, 2021 1pm-3pm EST. Outline of Event: 7 wonderful presenters working in records management, with 7 minute lightning round presentations (see below!). Virtual meeting invite and presentation order coming soon! Presenters: Angela Ossar, Office of the Governor of Texas. Jennifer Thompson, J.

The Texas Record
OCTOBER 17, 2018
Once again, the Texas State Library and Archives Commission (TSLAC) and the Texas Department of Information Resources (DIR) have joined forces to bring you another outstanding selection of speakers sharing case studies and presentations. How assessments can engage your organization in an e-records journey.

IT Governance
APRIL 24, 2024
She gave a fascinating, interactive presentation on AI, focusing on its benefits, as well as the threats it presents, such as prompt hacking and jailbreaks. Bridget made interesting points around how large language models such as ChatGPT are constantly using data to train their systems. Something to keep an eye on!

IBM Big Data Hub
DECEMBER 13, 2023
Skills transfer : With so much legacy knowledge leaving industrial businesses, it’s important that logical and structured information be presented regarding the nature of assets, the type of work that is done and what to analyze in the context of ensuring operational performance.

Security Affairs
OCTOBER 8, 2018
This case study, as well as others associated with less-than-locked-down Bitcoin wallets, emphasizes how people should not get too comfortable after buying a Bitcoin wallet, even one considered as being among the best of the best. One of them stores the wallet’s private key and the other acts as a proxy.

Info Source
MARCH 29, 2019
OpenText will be jointly presenting with leaders from Pacific Life to discuss how secure, cloud-based information management help to transform their business. . Riley McIntosh of Pacific Life and Alison Clarke from OpenText will present a case study on how to build a strong information management framework on March 27 at 10:15 am.

Preservica
MAY 11, 2016
Visiting seven cities across the UK, from London, to Edinburgh, to Dublin, over 200 IRMS and Archives and Records Association (ARA) members attended the workshop sessions, with a further 250 joining for the six ‘how to’ webinars. Next up, we’ll be attending and presenting at the annual IRMS conference in Brighton.
CILIP
OCTOBER 15, 2021
The event will highlight challenges and look at how to best navigate and avoid potential issues. There will be Q&A after each presentation followed by a panel discussion where delegates will be asked to contribute their own experiences and delve deeper into the topic. s perspective.

The Schedule
SEPTEMBER 13, 2018
Snowden Becker (University of California, Los Angeles) presented first with “To Protect and (Pre)Serve: Making, Keeping, and Considering Police Records.” Anne Gilliland (University of California, Los Angeles) presented next with “Refugees, Records, and ICT at the Borders of the State.”

CGI
OCTOBER 16, 2018
Digital transformation is forcing a rethinking of business process simplification, data science is taking on a new importance with a push for data-driven insights, and federal CIOs are learning how to wield new authorities effectively to meet the accompanying new levels of accountability. Employ situational leadership?do Add new comment.

CGI
JULY 19, 2018
RPA offers an opportunity to reengineer business processes, and bringing automation in during the early stages of an initiative presents a much easier opportunity to integrate it into the broader plan. CGI will present a case study of RPA on the second day of the event.

The Texas Record
OCTOBER 17, 2017
My first experience with bucketing was a few years ago during a presentation by Susan Cisco (from the Gimmal Group) at our local chapter ARMA meeting. ” As with everything new, it was exciting to think about, and my thoughts raced at how to best implement bucketing right away. Advantages.

ARMA International
NOVEMBER 21, 2019
In a new AIEF report, Blockchain Technology and Recordkeeping , the authors aim to provide an overview of blockchain technology that helps information professionals know how to address the challenge of effectively managing records in these emerging recordkeeping environments.

The Last Watchdog
JANUARY 30, 2019
Members gain access to third-party IT security risk management best practices via case studies, surveys, whitepapers, webinars, meetings and conferences. There’s no question that third-party risks at this moment present a vexing, potentially catastrophic exposure to any organization plugged into Internet-centric supply chains.

Archive-It
MAY 24, 2018
In case you missed it live, want to revisit anything, or share with your colleagues, the recording, presentation materials, and space for continued discussion are all now online here in the Archive-It Community Forum. Please share your insights, case studies, and questions to keep it going!

Role Model Software
MARCH 1, 2021
Portfolio Presentation + Discovery An important part of providing useful information for future clients is to organize past work in a compelling way. Then, the team tagged RoleModel’s software case studies with the titles they came up with; things like “Manufacturing”, “Healthcare”, and “Agriculture”, among others.

Hunton Privacy
FEBRUARY 24, 2020
The Guidance contains advice on how to understand data protection law in relation to artificial intelligence (“AI”) and recommendations for organizational and technical measures to mitigate the risks AI poses to individuals. The ICO notes that it can be difficult to describe the processing activity of a complex AI system.

eDiscovery Daily
FEBRUARY 3, 2020
Case studies where DApps have been successfully deployed. GDPR & CCPA are Fueling High Demand for On-Point RegTech Solutions Presented by Thomson Reuters. In this session, we’ll explore the State of RegTech solutions and how they’re being leveraged to automate compliance with key parts of the GDPR & CCPA.

John Battelle's Searchblog
AUGUST 25, 2014
so I don’t know who is presenting, but it doesn’t matter – I want to get smart about this company once again. Founder and CEO Dennis Crowley will be presenting Foursquare much-anticipated reboot, and I’m looking forward to hearing about the strategy from the founder’s mouth. 10:30 am – Foursquare.

IT Governance
FEBRUARY 7, 2024
With ransomware presenting such a significant threat to organisations, we at IT Governance feel it’s important to raise staff awareness of the threat of ransomware and how to defend against it. How to protect yourself from ransomware. The course also features numerous examples and case studies. Of course!

Cyber Info Veritas
JULY 18, 2018
This means that the security initiatives that should be put in place must focus on how to decrease the time it takes to realize, contain and remediate suspicious activity on the information system. In my experience, it is also important to remember that C-suite executives respond well to case studies.

eDiscovery Daily
SEPTEMBER 5, 2018
ILTA and Relativity Fest Present Finding the Fun in Writing Fundamentals , Tuesday (10/2) at 11:10am, with David moderating a panel that includes Judge Peck and Gary Kinder of WordRake. Hey, after 2,000 or so blog posts, maybe I can finally learn how to do it right! Serenity now!
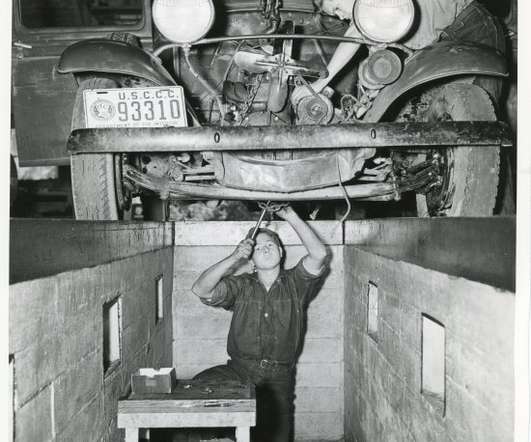
Unwritten Record
DECEMBER 3, 2019
According to John Salmond, author of The Civilian Conservation Corps, 1933-1942: A New Deal Case Study , “during its life span of nine years more than 2.5 This session aims to be an overview of how to navigate CCC records held by the Still Picture branch. Local Photo ID: 35-GE-3B-3.

Positively RIM
APRIL 29, 2010
From a records management point of view these "solutions" won't hold water and only demonstrate a serious lack of understanding how to support e-discovery and audit applications. “Of Of course, SharePoint has been the basis for many of these applications and more.

ChiefTech
AUGUST 19, 2008
for Information Professionals conference and I blogged some short summaries of each presentation. Last week I attended the second day of Key Forum's Enterprise 2.0 I thought might add some more reflective thoughts on the whole of that day: Neither open source or proprietary tools won out. environment.

Archive-It
JUNE 5, 2018
Our goal was to raise awareness about web archiving, how it works, who can be involved, and the special importance of collaborative efforts when building community-based thematic collections. . In order to archive the web, we will have to work together as networked yet local communities to capture our future digital heritage.

Archive-It
SEPTEMBER 1, 2021
This blog post was adapted and modified from my presentation at the IIPC Web Archiving Conference on June 16, 2021. by Yoo Young Lee, Head, Information Technology, University of Ottawa Library.

Collibra
JULY 6, 2022
Across business units, your colleagues spend too much time and effort trying to understand data, its relationships, and how to make it useful. > See how adaptive data and analytics governance can help. Despite the transformational promise, many organizations struggle to manage an increasingly complex data landscape. .

eDiscovery Daily
OCTOBER 20, 2019
District Judge Xavier Rodriguez, and moderator David Horrigan of Relativity as the panel covers the leading data discovery developments of the year, including the latest e-discovery cases and the landmark data privacy decision, Rosenbach v. ” dilemma presented by the pending U.S. Supreme Court case, Georgia v.

Archive-It
JANUARY 8, 2019
In 2017, our library applied for and received a grant to participate in the Community Webs program, designed to teach public libraries how to use web archiving tools and enable them to curate local history collections. History should help us connect our present lives to the continuity, or discontinuity, of our past.

eSecurity Planet
FEBRUARY 16, 2021
Here are some common and not so common malware threats and how to defend against them. How to Defend Against Adware. These adware strains often present themselves as a video, banner, full screen, or otherwise pop-up nuisance. How to Defend Against a Backdoor. How to Defend Against Botnets. Backdoors.

Thales Cloud Protection & Licensing
JANUARY 18, 2022
So software and device vendors that still operate on-premises are in a race against the clock, trying to figure out how to keep their customers happy. Read the case study to learn more about how Oxford enabled remote software accesses. Rachel Present Schreter | Director of Content/Product Marketing.

Thales Cloud Protection & Licensing
JANUARY 18, 2022
So software and device vendors that still operate on-premises are in a race against the clock, trying to figure out how to keep their customers happy. Read the case study to learn more about how Oxford enabled remote software accesses. Rachel Present Schreter | Director of Content/Product Marketing.

IT Governance
OCTOBER 31, 2019
On 5 and 6 November, professionals in the business continuity, cyber security, risk management and resilience sectors will gather in London to take part in workshops, explore case studies and listen to keynote speeches. The event will include a presentation by Prof Bill Buchanan of Edinburgh Napier University.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content