How Data Changes the Cyber-Insurance Market Outlook
Dark Reading
OCTOBER 16, 2023
By using data to drive policy underwriting, cyber-insurance companies can offer coverage without a price tag that drives customers away.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 tag policy
tag policy 
Dark Reading
OCTOBER 16, 2023
By using data to drive policy underwriting, cyber-insurance companies can offer coverage without a price tag that drives customers away.
Security Affairs
SEPTEMBER 8, 2023
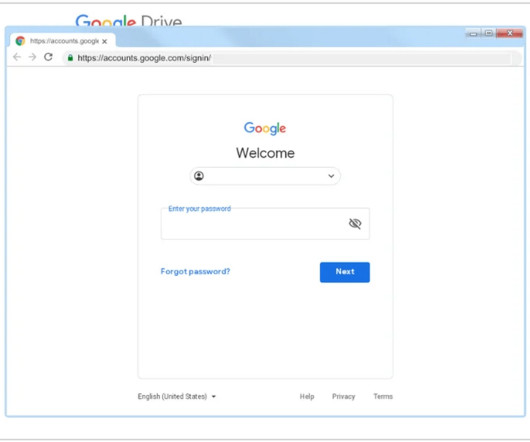
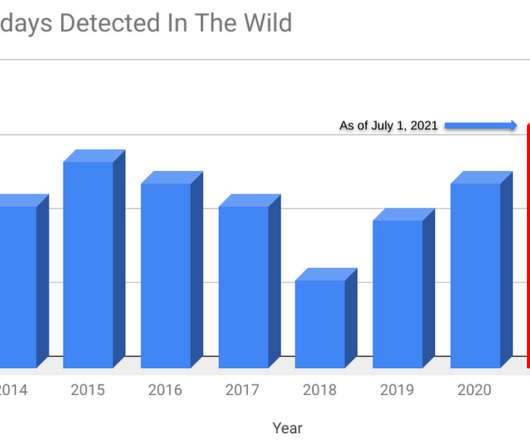
The attacks that took place in the past weeks were detected by researchers at Google’s Threat Analysis Group (TAG). “Recently, TAG became aware of a new campaign likely from the same actors based on similarities with the previous campaign. ” reads the advisory published by Google TAG.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
JUNE 1, 2023
Dependent Email Authentication Standards DMARC depends upon the successful establishment of the Sender Policy Framework (SPF) and the DomainKeys Identified Mail (DKIM) authentication standards. It is possible to define a DMARC policy in a DNS record without first setting up SPF and DKIM, but it won’t be able to do anything.

Security Affairs
FEBRUARY 5, 2024
Last week Ivanti warned of two new high-severity vulnerabilities in its Connect Secure and Policy Secure solutions respectively tracked as CVE-2024-21888 (CVSS score: 8.8) x), Policy Secure (9.x, and CVE-2024-21893 (CVSS score: 8.2). x) and Neurons for ZTA.
Security Affairs
DECEMBER 8, 2022
Our policy is to quickly report vulnerabilities to vendors, and within a few hours of discovering this 0-day, we reported it to Microsoft and patches were released to protect users from these attacks.” ” reads the post published by TAG. Google TAG shared indicators of compromise (IOCs) for this campaign.

HID Global
DECEMBER 7, 2022
Fish tagged with RFID Tags give the Government accurate data to inform policies leading to sustainable use of resources & investment in population recovery.
Security Affairs
APRIL 6, 2023
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. Google experts are tracking ARCHIPELAGO since 2012 and have observed the group targeting individuals with expertise in North Korea policy issues. ” reads the analysis published by Google TAG.

Collibra
MARCH 1, 2023
Also, a new Snowflake tag ingestion capability enables Snowflake tags to be incorporated into the Collibra Data Catalog. By leveraging Snowflake tags that categorize data users can develop more compliant business or policy processes and workflows.

Security Affairs
NOVEMBER 12, 2021
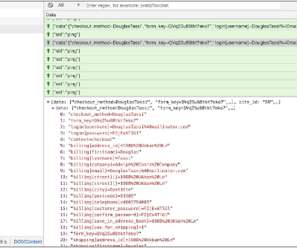
Google TAG researchers discovered that threat actors leveraged a zero-day vulnerability in macOS in a watering hole campaign aimed at delivering malware to users in Hong Kong. “To protect our users, TAG routinely hunts for 0-day vulnerabilities exploited in-the-wild. ” reads the analysis published by Google.

Collibra
NOVEMBER 16, 2021
With data governance, organizations can leverage the full power of Snowflake while complying with data privacy and policy requirements. Data masking and policy enforcement . But in order for customers to take advantage of this feature, they need Collibra’s Policy Enforcement. . Object tagging and ML-powered automation tagging .

DLA Piper Privacy Matters
AUGUST 22, 2023
It must also conduct security and ethical assessment on the algorithm and parametric models, record all the manual intervention involved in the annotation management and model training processes to prevent manipulation, and enable data subjects to amend or delete customized tags to opt out.

eSecurity Planet
MARCH 15, 2021
Microsegmentation is about identifying your organization’s most valuable network segments, establishing strict communication policies, and becoming the master of your network flows. This agent-based method translates to real-time protection of your policies. Tag Your Workloads. Outsource Endpoint Protection.

Security Affairs
AUGUST 7, 2020
Google published its second Threat Analysis Group (TAG) report which reveals the company has taken down ten coordinated operations in Q2 2020. Google has published its second Threat Analysis Group (TAG) report , a bulletin that includes coordinated influence operation campaigns tracked in Q2 of 2020. response to COVID-19.
Hunton Privacy
MARCH 1, 2024
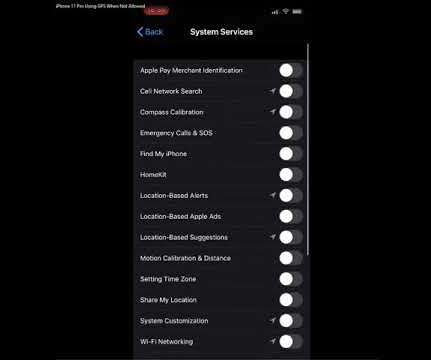
According to its statement, the ICO had been in discussions with the Home Office since August 2022 regarding its pilot, which involved the use of ankle tags and the GPS location tracking of up to 600 migrants who arrived in the UK and were on immigration bail.
Krebs on Security
DECEMBER 4, 2019
Apple says this is by design, but that response seems at odds with the company’s own privacy policy. ” The policy explains users can disable all location services entirely with one swipe (by navigating to Settings > Privacy > Location Services, then switching “Location Services” to “off”).

The Last Watchdog
AUGUST 8, 2023
With support for Microsoft CA and AWS Private CA, DigiCert Trust Lifecycle Manager enables discovery, issuance, automation and revocation, including the ability to tag, filter and apply policy to imported and discovered third-party digital certificates.

Collibra
DECEMBER 13, 2022
Specifically this year both companies gave greater focus to enabling governance of data policies and tagging as well as better lineage harvesting. . Snowflake includes an extensive set of native governance capabilities, expressed through SQL, for tag and data policy management.

DLA Piper Privacy Matters
JANUARY 19, 2022
Users must also be notified if algorithm recommendations are deployed on a site/platform/app – we anticipate this will be included in the privacy policy or website terms of use. Finally, users must be allowed to delete their individual tagging.

AIIM
AUGUST 10, 2021
Audit your existing legacy systems , content silos, and policies to determine where everything lives and determine your actual starting point. Put more intelligence into governance either by auto-tagging and categorizing content to kick off a retention workflow or by proactively managing the archival of business content and disposal of ROT.
Security Affairs
NOVEMBER 15, 2020
Once executed, a malicious JavaScript file is requested from the a C2 server (at https[:]//tags-manager[.]com/gtags/script2 The distinctive aspect of this attack is the use of WebSockets, instead of HTML tags or XHR requests, to extract the information from the compromised site that makes this technique more stealth.

The Texas Record
OCTOBER 8, 2021
How do I create policies for social media records? General Policies, Procedures, and More: How do I create an e-records management policy? General Policies, Procedures, and More: How do I create an e-records management policy? How do I capture social media records? What types of emails are routine or transitory?
Security Affairs
JULY 14, 2021
Security researchers from Google Threat Analysis Group (TAG) and Google Project Zero revealed that four zero-day vulnerabilities have been exploited in the wild earlier this year. As is our policy, after discovering these 0-days, we quickly reported to the vendor and patches were released to users to protect them from these attacks.”

AIIM
JANUARY 7, 2021
IT executives are also implementing new data use policies, deploying artificial intelligence, centralizing content, and restricting unauthorized apps. Stop End-User Tagging: For too long, end-user tagging has been the primary means by which most companies classify files that contain sensitive, proprietary, or regulated data.
Hunton Privacy
FEBRUARY 11, 2022
The proposed rules would require RIAs and registered funds to adopt and implement policies and procedures that are reasonably designed to address cybersecurity risks. The proposed rules would require RIAs and registered funds to review their cybersecurity policies and procedures no less frequently than annually. Recordkeeping.
Hunton Privacy
AUGUST 12, 2021
The Garante indicates that the Guidelines apply to a variety of different technologies, including not just cookies, but also other types of identifiers (such as fingerprinting and radio-frequency identification tags). Multilayer Policy: Banners and Unabridged Policy. 4 of January 9, 2004).

Collibra
APRIL 14, 2021
Together, the two companies help customers maximize value from their enterprise data, promoting agile data operations, helping to derive innovative business insights, while ensuring those insights can be trusted and relevant policies are complied with. . Enhancing data governance through policy enforcement.

Data Matters
MARCH 11, 2022
an unauthorized incident that has compromised the confidentiality, integrity, or availability of an information asset (data, system, or network) or violated the registrant’s security policies or procedures; b. previous cybersecurity incidents have informed changes in the registrant’s governance, policies and procedures, or technologies.

IBM Big Data Hub
DECEMBER 19, 2023
Codify security and compliance requirements into the patterns and guardrail them on the platform as set of policies. Address validation by integrating tooling, such as vulnerability scans, policy check tools (like cloud formation guard for AWS) and container security with the pipelines following shift-left principles.

Collibra
OCTOBER 13, 2021
Identifying, classifying and managing sensitive data as well as enabling security policies . Embed security policies with Collibra Policy Manager . With Collibra Policy Manager, as data moves to the cloud, Collibra can scan and identify sensitive data. Ownership and accountability .

erwin
JUNE 26, 2020
Tools should be provided that enable data experts to explore the data catalogs, curate and enrich the metadata with tags, associations, ratings, annotations, and any other information and context that helps users find data faster and use it with confidence. Clearly documents data catalog policies, rules and shares information assets.

eSecurity Planet
MARCH 21, 2022
“Our approach is that the visibility and the policy actually surrounds the data and define it for a particular type of data itself. ” Skyhigh’s approach is to determine what data is important and sensitive, how it’s being used, and who has access to it, and then base security policies on that.

Collibra
FEBRUARY 18, 2022
Business users work with organizational metrics and policies. Data enrichment through automatic discovery and user tagging and rating (for example, tagging personally identifiable information or PII). Support for security and privacy through rules and policy management. For example, .

eSecurity Planet
JANUARY 30, 2023
There are also manual additions for projects that lack labels in the GitHub API (tags, topics). According to Wang, this is how sophisticated security teams operate these days, by “managing security policies and operations like code.” Wang said the ranking excludes bots and anonymous accounts from the number of contributors.

IBM Big Data Hub
APRIL 24, 2024
Learn how organizations can use IBM Guardium® Data Protection software to monitor data wherever it is and enforce security policies in near real time. The price tag can add up quickly. Retention policies should also be limited. Organizations face fines of up to USD 7,500 per violation.
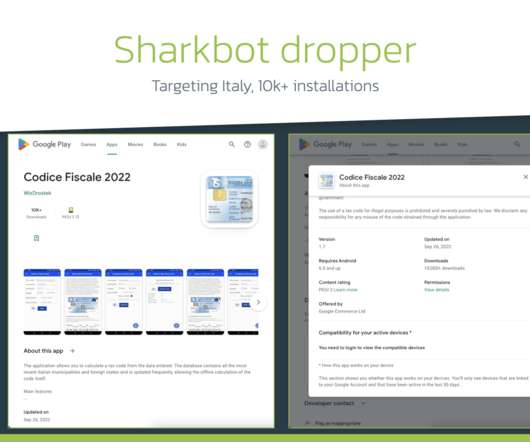
Security Affairs
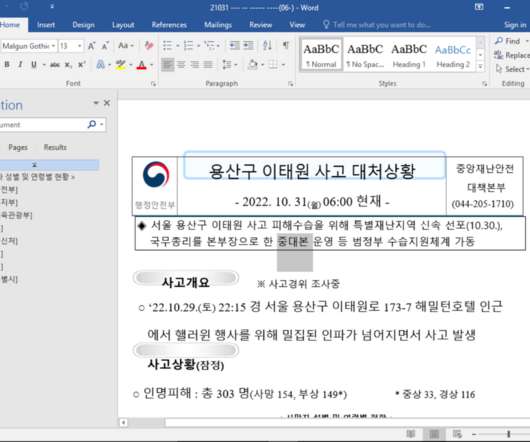
OCTOBER 31, 2022
“Following the updates to the “Developer Program Policy” and system updates, actors immediately introduce new ways to sneak to the official store, overcoming limitations or adjusting droppers to follow the guidelines and not arouse suspicion.” ” reads the analysis published by ThreatFabric. ” continues the report.

Collibra
MAY 4, 2021
Tagging, governance and classification to ensure the data housed in Databricks on Google Cloud is trustworthy and easy to find . Policies, standards and data quality rules to ensure data is consistent and accurate . Policy management for creating, reviewing and updating data policies to ensure adoption and maintain compliance .

IBM Big Data Hub
DECEMBER 19, 2023
Post-development (last-mile) wait time before go-live is easily 6–8 weeks or more due to: Manual evidence collection to get through security and compliance reviews beyond standard SAST/SCA/DAST (such as security configuration, day 2 controls, tagging and more).
erwin
AUGUST 6, 2020
erwin Data Intelligence (erwin DI) combines data catalog and data literacy capabilities for greater awareness of and access to available data assets, guidance on their use, and guardrails to ensure data policies and best practices are followed.

Troy Hunt
FEBRUARY 1, 2018
I've long been a proponent of Content Security Policies (CSPs). However, you can add a CSP via meta tag and indeed that's what I originally did with the upgrade-insecure-requests implementation I mentioned earlier when I fixed the Disqus issue. There's no faster way to generate a baseline policy than this!

Security Affairs
NOVEMBER 18, 2019
Even if AMP4Email implements a strong validator that only allows a list of tags and attributes in dynamic mails, it doesn’t implement a validation system to prevent cross-site scripting (XSS) attacks. Anyway, the code didn’t execute in the real-world case because of Content-Security-Policy deployed in AMP. testLocation.

The Texas Record
APRIL 26, 2021
Heck, there’s no way the student could have used metadata tags and targeted search terms to divine which of the invoices were legit, and which were self-dealing. When implementing a new system, policies should be updated accordingly. When implementing a new system, policies should be updated accordingly.

erwin
OCTOBER 31, 2019
Knowing where sensitive data is located and properly governing it with policy rules, impact analysis and lineage views is critical for risk management, data audits and regulatory compliance. Multiple components must be considered to effectively support a data governance, security and privacy trinity. They are: Data models.

DLA Piper Privacy Matters
APRIL 20, 2021
In practice this will require financial institutions to assess and classify/tag financial data against the five levels, and apply the relevant compliance obligations to each level accordingly. This could be a substantial task for some financial institutions. are fulfilled.

eSecurity Planet
APRIL 23, 2021
Policy control for sandboxing. When personnel rely on sandbox technology for security, collaboration, and more, there needs to be appropriate policies surrounding use. Tagging policy : Are you tagging resources for automated identification and allocation? The actual system where the program will be deployed.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content