Clorox Experiences Significant Financial Loss Stemming From Recent Cyber Attack
KnowBe4
OCTOBER 6, 2023
Popular American global manufacturer of cleaning products Clorox stated that recent sales and profit loss to a cyber attack.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

KnowBe4
OCTOBER 6, 2023
Popular American global manufacturer of cleaning products Clorox stated that recent sales and profit loss to a cyber attack.

IBM Big Data Hub
APRIL 5, 2024
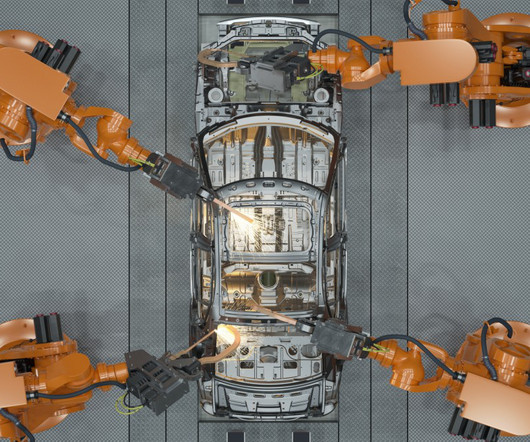
Prolonged development cycles might harm automotive manufacturers’ sales and customer loyalty. Automotive manufacturers, having a wealth of data related to existing designs, can use these large bodies of data to train AI models. However, in today’s market, consumers demand rapid releases of new models.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IBM Big Data Hub
FEBRUARY 13, 2024
The quality of outputs depends heavily on training data, adjusting the model’s parameters and prompt engineering, so responsible data sourcing and bias mitigation are crucial. Imagine training a generative AI model on a dataset of only romance novels. Garbage in, garbage out.

IBM Big Data Hub
JULY 12, 2023
GKN Aerospace is a leading global supplier in the aerospace industry, specializing in the design, manufacturing, and supply of advanced aerospace systems and components. With physical locations in 12 countries and 34 manufacturing sites worldwide, the company employs over 16,000 people.

IBM Big Data Hub
DECEMBER 19, 2023
These types of anomaly detection systems require a data analyst to label data points as either normal or abnormal to be used as training data. A machine learning model trained with labeled data will be able to detect outliers based on the examples it is given.

IT Governance
OCTOBER 13, 2023
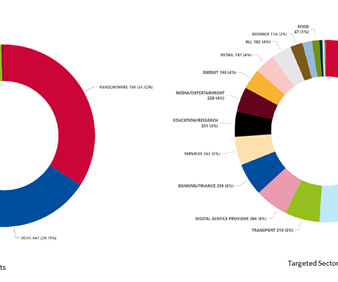
EvilProxy phishing campaign targets Microsoft 365 accounts via indeed.com A phishing campaign identified by Menlo Security has been targeting senior executives in various industries – most notably banking and financial services, property management and real estate, and manufacturing – since July.

Security Affairs
OCTOBER 23, 2020
Sopra Steria is a member of France’s Cyber Campus , a French initiative to spread cybersecurity awareness, training, and product sales. .” French authorities are investigating the incident. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->.

Info Source
OCTOBER 11, 2019
MFP software specialist Y Soft recently announced that its sales volume increased by 13% in its fiscal 2019 to reach $47 million. Based in the Czech Republic, the vendor recently beefed up its North American team with the appointment of Stephanie Kennard as EVP of sales. Kennard has formerly worked at Equitrac, Nuance, and OpenText. “Y

IBM Big Data Hub
SEPTEMBER 19, 2023
Overview: Data science vs data analytics Think of data science as the overarching umbrella that covers a wide range of tasks performed to find patterns in large datasets, structure data for use, train machine learning models and develop artificial intelligence (AI) applications. Watsonx comprises of three powerful components: the watsonx.ai

IBM Big Data Hub
AUGUST 8, 2023
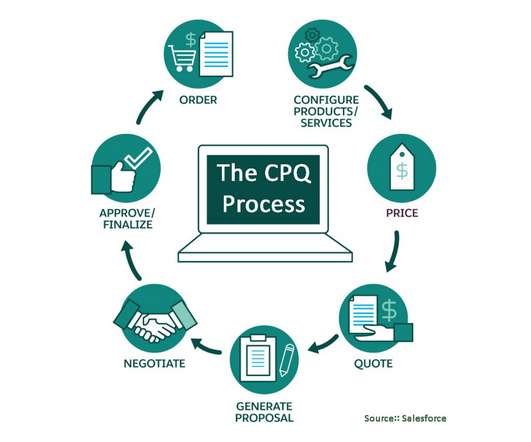
And trailblazers investing in AI are seeing a revenue uplift of 3 to 15 percent and a sales ROI uplift of 10 to 20 percent. Forrester projects a shift of $2 trillion away from traditional direct sales to digital marketplaces. Power of the Microsoft Azure Marketplace Digital marketplaces are disrupting the way clients buy software.

IBM Big Data Hub
NOVEMBER 10, 2023
Areas to assess can include, financial, manufacturing, inventory, sales and more. Team members should be put through user training and key stakeholders should be involved in this testing process as well. Make sure all employees are trained on the system; consider implementing ERP software in stages before going company-wide.
Role Model Software
MAY 4, 2021
In the manufacturing and design world, computer-aided design (CAD) is a commonly used tool. CAD software is usually very complicated That is why businesses who use CAD generally have trained professionals handling the software, someone who has put in those many hours to understand the process.

IBM Big Data Hub
JULY 19, 2023
Yet, it is burdened by long R&D cycles and labor-intensive clinical, manufacturing and compliancy regimens. Commercial: Marketing content creation, patient experience, rep onboarding & training sales enablement and knowledge hub. Robustness : AI systems should be able to withstand attacks to the training data.

eSecurity Planet
SEPTEMBER 14, 2022
According to the 2021 IBM Threat Force Intelligence Index , Manufacturing was the industry most likely to be attacked last year, comprising 23.2% This is the same trick business professionals might use to secure a sale (i.e. Further reading: Best Cybersecurity Awareness Training for Employees. of cyber attacks IBM handled.

IBM Big Data Hub
OCTOBER 16, 2023
Machine learning in marketing and sales According to Forbes , marketing and sales teams prioritize AI and ML more than any other enterprise department. Reinforcement learning uses ML to train models to identify and respond to cyberattacks and detect intrusions. The platform has three powerful components: the watsonx.ai

IBM Big Data Hub
MAY 17, 2024
Poorly run implementations of traditional or generative AI in commerce—such as models trained on inadequate or inappropriate data—lead to bad experiences that alienate consumers and businesses. These experiences result in higher engagement, increased customer satisfaction, and ultimately, higher sales.

IBM Big Data Hub
APRIL 25, 2024
An early case study of BPR was Ford Motor Company, which successfully implemented reengineering efforts in the 1990s to streamline its manufacturing processes and improve competitiveness. Organizations of all sizes and industries implement business process reengineering. BPR initiatives generally boost key performance indicators (KPIs).

Reltio
JANUARY 29, 2020
In a prior post , I also covered the intentional use of these by manufacturers. As you may have just experienced an HVAC repair or are getting ready to put your house on the market for the early spring real estate rush, you may be thinking about adding a home warranty policy to your sale to sweeten the deal for a buyer.

Info Source
JANUARY 28, 2019
Having joined The Crowley Company in 2017 after a long career in IT sales, project management and support with Fortune 50 and 100 companies, eldest brother Kevin Crowley has been named chief operating officer. Chris’ sons, Christopher Jr. (24) 24) and Brendan (22), are also employed by the firm. Conversion Services Director Named.

Hunton Privacy
SEPTEMBER 16, 2019
Vehicle information : Clarifies that the CCPA’s opt-out of sale right “shall not apply to vehicle information or ownership information retained or shared between a new motor vehicle dealer. and the vehicle’s manufacturer. as part of CCPA compliance training). Code § 1798.105(d)(1)). Code § 1798.145(l)(3)). Code § 1798.140(y)).
IBM Big Data Hub
JUNE 26, 2023
According to the recent statistics released by a local auto industry association, the sales of China’s fuel vehicle market have declined for three consecutive years. The auto parts manufacturers caught in it are facing the problem of how to survive and grow against the increasingly fierce competition.

CGI
MAY 26, 2015
Your competition now knows your pricing, your sales strategy, and your product roadmap. Theft of business strategy is just one threat that is universal in the corporate and manufacturing worlds. Training your workforce to recognize behaviors that are red flags for insider threats, and educate them on enterprise policies.

RFID Global Solution, Inc.
MARCH 22, 2018
Planes, Trains and Automobiles – How RFID is Transforming Transportation. It can also be used to track and control train locations and positioning, as well as railcar movement and railway conditions. Call 703-648-1550 or email us at sales@rfidgs.com. by Diana Hage. Learn More About RFID for Your Business.

IT Governance
MARCH 5, 2024
Publicly disclosed data breaches and cyber attacks: in the spotlight Millions of Pure Incubation Ventures records listed on hacking forum 183,754,481 records apparently belonging to the venture capital and private equity group Pure Incubation Ventures have been listed for sale on a hacking forum. The claim is yet to be verified.

IT Governance
DECEMBER 20, 2022
In the midst of all this, organisations across Europe reported delays as a result of alleged state-sponsored attacks – including Toyota’s Japanese plants and a kettle manufacturer in the Isle of Man. You can see more incidents from February in our list of data breaches and cyber attacks.

IT Governance
JANUARY 30, 2024
Mobile network database breach exposes 750 million Indians’ personal data The Indian security company CloudSEK claims to have found the personal data of 750 million Indians for sale on an “underground forum”. TB Four Hands Source (New) Manufacturing USA Yes 1.5 TB UK forex customers Source (New) Finance UK Yes 1,001,214 A.N.S.

ForAllSecure
APRIL 30, 2020
David Brumley: It's a completely fundamental, basic library routine used by everything from rendering software to, autos, planes, cars, trains, and cyber physical systems. There's a lot of words you could use for that sales model, but it's pretty cynical. I'd be like, "What? What's this? Remind me.". Dennis Fischer: Right.

ForAllSecure
APRIL 30, 2020
David Brumley: It's a completely fundamental, basic library routine used by everything from rendering software to, autos, planes, cars, trains, and cyber physical systems. There's a lot of words you could use for that sales model, but it's pretty cynical. I'd be like, "What? What's this? Remind me.". Dennis Fischer: Right.

ForAllSecure
APRIL 30, 2020
David Brumley: It's a completely fundamental, basic library routine used by everything from rendering software to, autos, planes, cars, trains, and cyber physical systems. There's a lot of words you could use for that sales model, but it's pretty cynical. I'd be like, "What? What's this? Remind me.". Dennis Fischer: Right.

IBM Big Data Hub
JANUARY 31, 2024
Companies generally outsource non-core tasks and functions that are similar across organizations, such as back-office operations (accounting, IT and human resources) and front-office operations (sales, marketing and customer support).

eSecurity Planet
SEPTEMBER 16, 2022
In its 2021 Threat Force Intelligence Index , IBM reported that manufacturing and financial services were the two industries most at risk for attack, making up 23.2% However, the UI can be a little complicated for some users, with certain tools and features seemingly not covered by Sift’s training kit.

Info Source
JANUARY 9, 2020
As a manufacturer and reseller of the best-known scanner brands in the industry, Crowley Imaging’s access to technology for quality digitization is unparalleled, resulting in the divisions’s third MLA platinum distinction. The firm also has manufacturing and sales offices in Basingstoke, U.K., Community involvement.

ForAllSecure
MARCH 8, 2023
Yeah, it was at CSO but I was actually chief strategy officer, and I ran some of I ran marketing on some of the pre sale, operations support. So the, you know, essentially a lot of the pre sale stuff. Oil and gas, manufacturing plants and healthcare system. WANG : Twistlock at Twistlock. She formed her own consulting firm.

IBM Big Data Hub
JUNE 29, 2023
Manufacturing has undergone a major digital transformation in the last few years, with technological advancements, evolving consumer demands and the COVID-19 pandemic serving as major catalysts for change. Here, we’ll discuss the major manufacturing trends that will change the industry in the coming year. Industry 4.0

eSecurity Planet
FEBRUARY 16, 2021
Boost your organization’s IT literacy with ongoing cybersecurity training so they recognize the threats posed by malware attacks. Most device or software manufacturers place backdoors in their products intentionally and for a good reason. When alerted to potential vulnerabilities, patch promptly. Backdoors. RAM Scraper.

Troy Hunt
APRIL 2, 2020
Also over and over again, manufacturers say “we take security seriously” [link] — Troy Hunt (@troyhunt) December 12, 2019 That last one is particularly apt here as it gets us on-topic with kids watches. The pattern is alarmingly predictable. This investigation was conducted by a 3rd party C.R.E.S.T

ForAllSecure
MAY 13, 2022
I don't kind of mix the two and I'm in charge of global sales operations, channel operations and go to market strategy. And I remember asking questions, who were the manufacturers? The train keeps going. The train isn't affected at all by this person hopping on. And were these things even vetted by a security community?

eSecurity Planet
MARCH 22, 2023
Operating technology (OT), also known as the industrial internet of things (IIoT), uses smart pumps, conveyor belts, motors, and manufacturing equipment — and the operations teams that install the devices may not always inform the network security team about them. More aggressive vendors might even intentionally oversell their clients.

IT Governance
APRIL 29, 2024
Publicly disclosed data breaches and cyber attacks: in the spotlight Data scraping site taken offline after billions of Discord users’ messages offered for sale A data scraping website called Spy.pet has been taken offline after harvesting more than 4 billion messages made by almost 630 million Discord users and offering them for sale.

Reltio
JANUARY 28, 2021
It also powers your real-time operations across digital channels and human interactions such as call center and sales so you can deliver omnichannel connected customer experiences and boost NPS scores. Seas of unused Big Data exist in your market segment, whether your industry is finance, healthcare, CPG, manufacturing, or B2B.
Thales Cloud Protection & Licensing
DECEMBER 4, 2023
The report also highlights that ransomware attacks are becoming more targeted, with attackers focusing on high-value targets with particular emphasis on the Industrial and Manufacturing sectors. Periodic security awareness training is critical, as social engineering and phishing are the initial actions that open the doors to attacks.

ForAllSecure
MAY 30, 2023
We know that you know, manufacturing is an area that we've seen a lot of targets over the last quarter. Again, because if you bring down manufacturing operations, there's a high impact to the business and necessity to recover quickly. Majority of time we will actually be working for counsel on behalf of the client.

KnowBe4
MARCH 7, 2023
New-school security awareness training teaches your employees to recognize social engineering tactics so they can avoid falling for phishing attacks. That's why training your end-users is so important. New-school security awareness training enables your employees to recognize phishing and other social engineering attacks.

Krebs on Security
OCTOBER 5, 2018
Supermicro has assembly facilities in California, the Netherlands, and Taiwan, but its motherboards—its core product—are nearly all manufactured by contractors in China. The reason is that by nearly all accounts it would be punishingly expensive to replicate that manufacturing process here in the United States. based firms.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content