Is Your Computer Part of ‘The Largest Botnet Ever?’
Krebs on Security
MAY 29, 2024
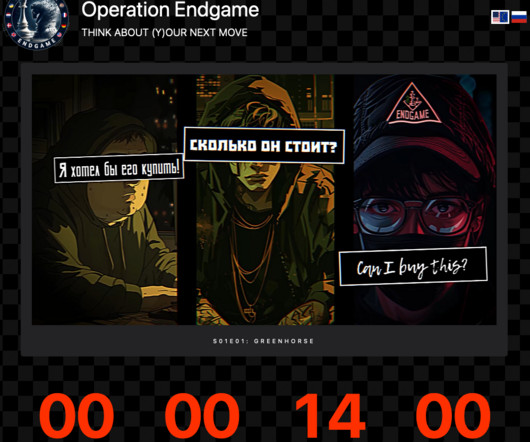
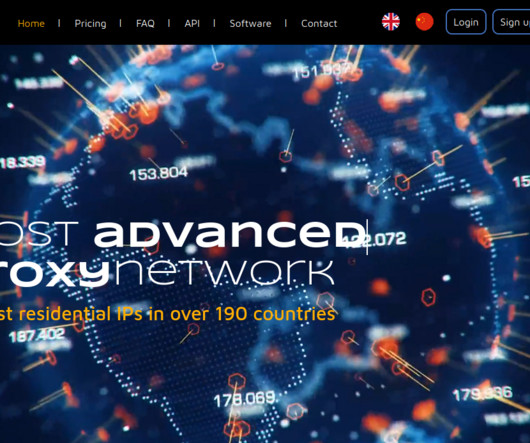
The U.S. Department of Justice (DOJ) today said they arrested the alleged operator of 911 S5 , a ten-year-old online anonymity service that was powered by what the director of the FBI called “likely the world’s largest botnet ever.” The arrest coincided with the seizure of the 911 S5 website and supporting infrastructure, which the government says turned computers running various “free VPN” products into Internet traffic relays that facilitated billions of dollars i






































Let's personalize your content