Authentication in the Changing Healthcare Industry
HID Global
JUNE 7, 2023
Protect sensitive healthcare data with modern authentication solutions. Learn about RFID technology for secure access in the changing healthcare industry.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 healthcare-data-security-solutions
healthcare-data-security-solutions  Industry Related Topics
Industry Related Topics 
HID Global
JUNE 7, 2023
Protect sensitive healthcare data with modern authentication solutions. Learn about RFID technology for secure access in the changing healthcare industry.

The Last Watchdog
NOVEMBER 8, 2021
Related: Hackers relentlessly target healthcare providers. However, healthcare data ranks at the top of the list for needing improvements in security and privacy protections. There are many reasons for the vulnerable state of healthcare data. Patient data exposures. Dealing with policy-based access.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
OCTOBER 25, 2023
25, 2023— DataPivot Technologies , a prominent provider of Data Center, Cloud and Data Protection Solutions, understands that healthcare providers today are scrambling to solve complex clinical, operational and patient data backup & recovery challenges. North Andover, Mass.,

IBM Big Data Hub
JANUARY 3, 2024
The COVID-19 pandemic revealed disturbing data about health inequity. With today’s new generative AI products, trust, security and regulatory issues remain top concerns for government healthcare officials and C-suite leaders representing biopharmaceutical companies, health systems, medical device manufacturers and other organizations.

The Last Watchdog
AUGUST 3, 2023
3, 2023 — Vaultree, a cybersecurity leader pioneering Fully Functional Data-In-Use Encryption (FFDUE), today announces a strategic integration with Tableau, a renowned platform for data visualization and business intelligence. San Francisco and Cork, Ireland, Aug. Today, we’re making that future a reality.”
Krebs on Security
DECEMBER 8, 2022
The first centers on targeting healthcare organizations that offer consultations over the Internet and sending them booby-trapped medical records for the “patient.” Alex Holden is founder of Hold Security , a Milwaukee-based cybersecurity firm. . healthcare organizations. Encrypting sensitive data wherever possible.

Security Affairs
MAY 8, 2023
NextGen Healthcare suffered a data breach, the security incident exposed the personal information of approximately 1 million individuals. Healthcare solutions provider NextGen Healthcare suffered a data breach that exposed the personal information of informing approximately one million individuals.

The Last Watchdog
JANUARY 28, 2024
However, over the past 20 years the practice of analyzing user data hasn’t advanced much beyond serving the business models of these tech giants. Rising data privacy regulations underscores the need for such a capability, Boyle told me. This, in turn, has led to rising data privacy regulations. That could be about to change.

IBM Big Data Hub
JANUARY 10, 2024
Hybrid cloud has become the dominant approach for enterprise cloud strategies , but it comes with complexity and concerns over integration, security and skills. To address these concerns the industry is embracing container runtime environments to abstract away infrastructure.

The Last Watchdog
JUNE 23, 2023
June 22, 2023 — Dasera , the premier automated data security and governance platform for top-tier finance, healthcare, and technology enterprises, is thrilled to unveil “Ski Lift,” a complimentary platform exclusively designed for Snowflake users.

Hunton Privacy
JANUARY 10, 2019
Department of Health and Human Services (“HHS”) recently announced the publication of “Health Industry Cybersecurity Practices: Managing Threats and Protecting Patients” (the “Cybersecurity Practices”). The Cybersecurity Practices also will include a Cybersecurity Practices Assessments Toolkit, but that is still under development.

IBM Big Data Hub
MARCH 20, 2024
For highly regulated industries, these challenges take on an entirely new level of expectation as they navigate evolving regulatory landscape and manage requirements for privacy, resiliency, cybersecurity, data sovereignty and more. This means actively minimizing downtime and closing gaps in the supply chain to remain competitive.

IBM Big Data Hub
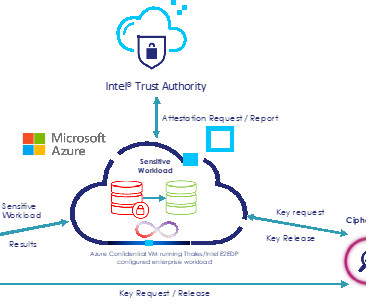
JANUARY 12, 2024
The integration of artificial intelligence (AI) has ushered in a new era of technological progress, offering a spectrum of benefits across industries. However, as AI services find a home in cloud platforms, the issue of data confidentiality takes center stage.

IBM Big Data Hub
NOVEMBER 7, 2023
Recent advances in areas like AI and quantum computing offer transformative potential for businesses, but may also bring new risks and security challenges. IBM is working to address these challenges and evolving threats by helping organizations support highly secure, resilient and durable storage through technology like Cloud Object Storage.

Security Affairs
JANUARY 17, 2023
How healthcare delivery organizations (HDOs) can manage the IT asset risks during a healthcare M&A process. An M&A is often associated with the “business world”; with industries such as finance, retail, technology, and more. An M&A should be a time for organizational improvement, not increased cyber security risks.

Thales Cloud Protection & Licensing
NOVEMBER 8, 2023
All data remains subject to the laws and regulations of its home country, regardless of where it resides. Additionally, in highly regulated sectors such as finance or healthcare or state and local government entities, organizations need to meet additional compliance laws and mandates.

IBM Big Data Hub
JANUARY 30, 2024
In the last post , we looked at creating a blueprint for a sustainable data center. Now we’ll look at how to get the most out of a modern data center. Get inspired A successful data center implementation can best be described as a distributed, dynamic, efficient and resilient IT nucleus.
Thales Cloud Protection & Licensing
NOVEMBER 14, 2023
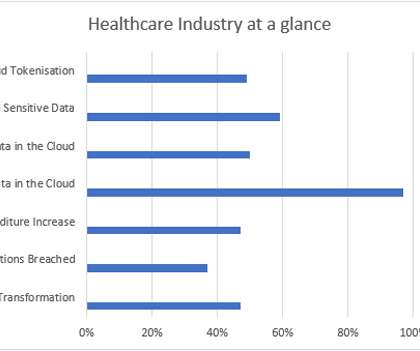
Nearly half (47%) of the respondents of the 2023 Thales Data Threat Report reported that cyberattacks are increasing in volume and severity. Therefore, there is a need to continually raise the bar in cloud security.

Thales Cloud Protection & Licensing
APRIL 25, 2022
How to protect healthcare and life-sciences data from a cyber attack pandemic. Once slow to adopt new technologies, healthcare-related industries have been rapidly embracing digitalization to enable patient-centric care that is more effective for patients and safer for patients, healthcare professionals and researchers.

IBM Big Data Hub
DECEMBER 18, 2023
For organizations of all types—and especially those in highly regulated industries such as financial services, government, healthcare and telco—considerations including the rise of generative AI, evolving regulations and data sovereignty laws and ongoing security challenges must be top of mind.

The Last Watchdog
DECEMBER 5, 2018
The healthcare industry has poured vast resources into cybersecurity since 2015, when a surge of major breaches began. While the nature of these breaches has evolved over the last four years, the growth in total healthcare incidents has unfortunately continued unabated. Related: How to get of HIPAA hit list. Weak links.

Reltio
JUNE 20, 2023
Every organization must solve daunting data challenges while managing risks, growing profits, and carefully monitoring costs. That’s why the quest for clean, connected, and actionable real-time data has become the linchpin of every successful digital transformation, even in this budget-constrained era.

The Last Watchdog
MAY 18, 2021
To make matters more difficult, implementing new security software and processes to address these issues is another big hurdle, often causing disruption—and not the good kind. So, how can businesses strike the balance between proper security measures and a modernized IT infrastructure with the headaches of migrating systems?

Security Affairs
FEBRUARY 28, 2024
Analyzing the Email Security Landscape and exploring Emerging Threats and Trends. VIPRE Security Group’s latest report, “Email Security in 2024: An Expert Insight into Email Threats,” delves into the cutting-edge tactics and technologies embraced by cybercriminals this year. million as malicious.

Data Matters
APRIL 11, 2022
The concept of “important data” is a cornerstone of China’s data regulatory regime. The Cyber Security Law (2017) (the CSL ) prohibits operators of critical information infrastructures ( CIIs ) from transferring their “important data” and personal information outside of China. Then, what are “important data”?

eSecurity Planet
FEBRUARY 23, 2022
How can an industrial recycler safely secure its $400,000 hard drive recertification rack with control software that only runs on Windows XP? The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks. Also read: Top IoT Security Solutions for 2022.
Thales Cloud Protection & Licensing
SEPTEMBER 27, 2023
” You’ll find Thales on stand 152, level Daghilev, and don’t miss our workshop at 3pm on October 11th as Didier Espinet, Chief Information Security Officer, Thales DIS and Laini Cultier, IAM expert at Thales will present a session entitled “Trust and Security: The Keys to Success in the Public Cloud”. Our event booth number is H25-C70.

Thales Cloud Protection & Licensing
SEPTEMBER 18, 2023
Compliance madhav Tue, 09/19/2023 - 05:17 It is essential for any business that stores, processes, and transmits payment card information to comply with the Payment Card Industry Data Security Standard (PCI DSS). Consumers’ payment data is a compelling target for criminals who continue to circumvent IT security defenses.

Thales Cloud Protection & Licensing
MAY 23, 2022
Access Management is Essential for Strengthening OT Security. These systems are connected to and managed from the cloud to fine-tune performance, provide data analytics, and ensure the integrity of critical infrastructure across all sectors. Healthcare sector. Tue, 05/24/2022 - 06:11. The threat landscape. This included $91.6

IBM Big Data Hub
FEBRUARY 22, 2024
While AI can undoubtedly offer a competitive edge to organizations that effectively leverage its capabilities, we have seen unique concerns from industry to industry and region to region that must be considered—particularly around data. And our work doesn’t stop there.

IBM Big Data Hub
FEBRUARY 23, 2024
This sophisticated foundation propels conversational AI from a futuristic concept to a practical solution. DL models can improve over time through further training and exposure to more data. ML and DL lie at the core of predictive analytics, enabling models to learn from data, identify patterns and make predictions about future events.

Armstrong Archives
DECEMBER 18, 2023
This reality has made data security increasingly important, requiring a sea change in the way companies handle their documents. The decisions you make have financial, operational, and security implications. Sensitive data leaks can lead to identity theft, fraud, or corporate espionage.

IBM Big Data Hub
APRIL 24, 2024
An online retailer always gets users’ explicit consent before sharing customer data with its partners. A navigation app anonymizes activity data before analyzing it for travel trends. One cannot overstate the importance of data privacy for businesses today. The user can accept or reject each use of their data individually.
Thales Cloud Protection & Licensing
NOVEMBER 16, 2020
Healthcare Organizations Need to Adapt Their Data Protection Policies to the New Threat Environment. Healthcare providers are at the epicenter of the fight against coronavirus. For example, data sprawl has significantly increased due to all of the new patient data that has been created during the pandemic.

eSecurity Planet
AUGUST 9, 2022
Regulatory compliance and data privacy issues have long been an IT security nightmare. And since the EU’s General Data Protection Regulation (GDPR) took effect May 25, 2018, IT compliance issues have been at the forefront of corporate concerns. GDPR-style data privacy laws came to the U.S.

Data Matters
MARCH 28, 2022
Department of Health and Human Service’s Office for Civil Rights (“OCR”) issued industry guidance for Health Insurance Portability and Accountability Act (“HIPAA”) regulated entities to take preventative steps to protect against some of the more common, and often successful, cyber-attack techniques. On March 17, 2022, the U.S.

The Last Watchdog
JANUARY 7, 2019
In 2019, and moving ahead, look for legacy IT business networks to increasingly intersect with a new class of networks dedicated to controlling the operations of a IoT-enabled services of all types, including smart buildings, IoT-enabled healthcare services and driverless cars. Related: Why the golden age of cyber espionage is upon us.

The Last Watchdog
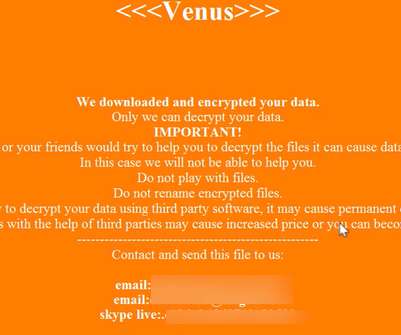
SEPTEMBER 7, 2022
The technology industry has met the dramatic rise in ransomware and other cyber attacks with an impressive set of tools to help companies mitigate the risks. Healthcare and public health, financial services, and IT organizations are frequent targets, although businesses of all sizes can fall victim to these schemes.

IT Governance
MAY 2, 2023
Welcome to our April 2023 list of data breaches and cyber attacks. You can find the full list of data breaches and cyber attacks below, along with our rundown of the biggest incidents of the month. Biggest data breaches of April 2023 1. million people.

Security Affairs
JUNE 20, 2023
Data-centric distributed resilience (DDR) offers a compelling approach to addressing data sovereignty in cybersecurity. As much of our modern life relies upon the cloud, the question of data protection is front of mind for many organizations. Data sovereignty plays a crucial role in a robust security strategy.

Thales Cloud Protection & Licensing
OCTOBER 5, 2022
Along with celebrating Cyber Security Awareness Month, several exciting events are taking place across the world, aiming to educate people on the latest trends in cybersecurity and privacy. GITEX GLOBAL is the biggest security and technology event and exhibition in the Middle East. GITEX GLOBAL, 10-14 October, Dubai.

eSecurity Planet
SEPTEMBER 14, 2022
Cybercrime is a growth industry like no other. A major focus of cybersecurity as an industry is its efforts to detect, root out, and respond to potential fraudsters attempting to trick companies and people out of their money, data, or both. Read More At: Top Secure Email Gateway Solutions for 2022.

Thales Cloud Protection & Licensing
MARCH 23, 2022
Shifting Risk and Business Environment Demand creates a Shift in Security Strategies. The 2022 Thales Data Threat Report, based on data from a survey of almost 2,800 respondents from 17 countries across the globe, illustrates these trends and changes. Malware and accidental human error are the biggest security threats.

IT Governance
NOVEMBER 13, 2023
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. The data included shoppers’ names, email addresses, phone numbers, countries of residence and membership numbers.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content