UK Sets Up Fake Booter Sites To Muddy DDoS Market
Krebs on Security
MARCH 28, 2023
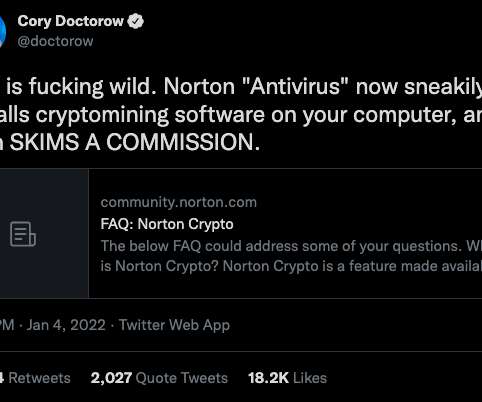
The NCA says all of its fake so-called “booter” or “stresser” sites — which have so far been accessed by several thousand people — have been created to look like they offer the tools and services that enable cyber criminals to execute these attacks. ” the NCA announcement continues. According to U.S.









































Let's personalize your content