How to Handle Retail SaaS Security on Cyber Monday the Hacker News
IG Guru
NOVEMBER 29, 2023
The post How to Handle Retail SaaS Security on Cyber Monday the Hacker News first appeared on IG GURU. Check out the article here.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

IG Guru
NOVEMBER 29, 2023
The post How to Handle Retail SaaS Security on Cyber Monday the Hacker News first appeared on IG GURU. Check out the article here.

Thales Cloud Protection & Licensing
JANUARY 20, 2022
How to activate multifactor authentication everywhere. Workstations are often shared between several workers (in call centers, shop floor, retail stores.). Many cloud authentication services available on the market offer only one mobile app as native authentication method. Thu, 01/20/2022 - 10:19.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
NOVEMBER 20, 2022
How to Secure Access for your Seasonal Workers. As the holiday season approaches, many retail, hospitality, logistics, and food manufacturing organizations hire seasonal workers to meet increasing demand. The Bureau of Labor Statistics reports a 7% job rise in the retail industry. Mon, 11/21/2022 - 05:36.

eSecurity Planet
SEPTEMBER 10, 2021
From the very beginning of the cloud computing era, security has been the biggest concern among enterprises considering the public cloud. In addition, 95 percent of survey respondents confirmed that they are extremely to moderately concerned about public cloud security. What is cloud security?

Thales Cloud Protection & Licensing
JANUARY 20, 2022
How to activate multifactor authentication everywhere. Workstations are often shared between several workers (in call centers, shop floor, retail stores.). Many cloud authentication services available on the market offer only one mobile app as native authentication method. Thu, 01/20/2022 - 10:19.

AIIM
MARCH 29, 2022
Google is creating a dedicated Digital Assets Team within Google Cloud to support building, transacting, storing value, and deploying new products on blockchain-based platforms. Retailers and brands will open virtual stores, launch virtual collections, or host exclusive digital events for their targeted NFT holders.

Reltio
JANUARY 9, 2020
Do you find yourself wondering how to win customers in this hyper-competitive, always-on era? But how do you create a CX that's unique and meaningful to your customers - and potential customers? How to Win Customers: Data Unlocks the Door . You're not alone. The answer is in the data.
Thales Cloud Protection & Licensing
NOVEMBER 25, 2021
How to Protect Your Systems from Unauthorized Access This Holiday Season. Many retailers and shipping services are planning to hire temporary workers for the upcoming holiday season. That’s 50,000 more seasonal employees than the retailer brought in at the end of 2020, noted CNBC. Thu, 11/25/2021 - 05:41.

IBM Big Data Hub
FEBRUARY 23, 2024
A data controller is any organization, group, or person that collects personal data and determines how it is used. Think: an online retailer that stores customers’ email addresses to send order updates. Learn how IBM data security and protection solutions secure data across hybrid clouds and simplify compliance requirements.

eSecurity Planet
JUNE 23, 2023
Also read: 9 Best Penetration Testing Tools 24 Top Open Source Penetration Testing Tools How to Implement a Penetration Testing Program in 10 Steps Third-Party Vendor Tests: Challenges and Maximizing Value Many organizations prefer to perform in-house penetration tests because of the challenges with third-party vendors.

The Last Watchdog
MAY 9, 2023
Related: Centralizing control of digital certificates I had the chance to sit down with Deepika Chauhan , DigiCert’s Chief Product Officer, and Mike Cavanagh , Oracle’s Group Vice President, ISV Cloud for North America. They divided the planet into 55 “ public cloud regions ” spread across 22 nations on five continents.

IBM Big Data Hub
JANUARY 30, 2024
Now we’ll look at how to get the most out of a modern data center. Retail: Manage e-commerce platforms, customer data analytics and supply chain logistics, where data analysis often must occur at the edge. VMware specializes in cloud computing and virtualization, critical components in modernizing data centers.

OpenText Information Management
APRIL 15, 2024
For most businesses, AI has introduced a new mindset, a new way to think, a new appreciation for trust and data, and a new outlook on how to unleash human potential. We have accelerated our portfolio into cloud, and we’ve placed strategic emphasis on key integrations--notably embedding security and intelligence everywhere.

The Last Watchdog
MAY 3, 2021
That said, it may not be well-suited, in its current form, to achieve the level of security needed in an environment where companies rely on multi-cloud and hybrid cloud networks and wide-open software development. PKI has worked very well for expanding e-commerce into what it is today. Customized keys.

OpenText Information Management
MARCH 29, 2024
Mark will be joined by OpenText customer Srinath Kanisapakkam, chief data and analytics officer at Nationwide Building Society (NBS) , who will share how OpenText Experience Cloud solutions give NBS the scalable, secure, communication platform they needed to meet highly regulated FSI communication requirements.

The Last Watchdog
SEPTEMBER 24, 2018
Related: 6 best practices for cloud computing. An excerpt from Reddit’s mea culpa says it all: “On June 19, we learned that between June 14 and June 18, an attacker compromised a few of our employees’ accounts with our cloud and source code hosting providers. This is because they are useful in targeting big companies.

Reltio
APRIL 1, 2020
This post offers a look at the topic of scalability, outlining what the concept means and how it applies to customer data management, with some customer examples. The issue is particularly prevalent in industries like retail and financial services, which can contend with massive spikes in usage based on seasonality and marketing initiatives.

CGI
MARCH 31, 2020
Despite significant digital investment, corporate and transaction banks are behind on their digital journey due to the lower (and slower) impact of digital transformation on traditional corporate banking products, as well as challenges in figuring out how to run their business better through effective data usage and digitization.

IBM Big Data Hub
NOVEMBER 9, 2023
And digital experiences define your brand, whether you’re a retailer, a bank, or the Recording Academy,” says Panos A. To better engage its members and attract new ones, the Recording Academy needed to modernize, migrating its legacy CRM database to a cloud-based solution. Panay, President of the Recording Academy.
IBM Big Data Hub
APRIL 20, 2023
What do a Canadian energy company, a Dutch coffee retailer and a British multinational consumer packaged goods (CPG) company have in common right now? All are transforming their procurement operations by leveraging state-of-the-art process mining and intelligent automation technology. dollars annually in direct or indirect procurement.

Thales Cloud Protection & Licensing
SEPTEMBER 20, 2021
Although the news headlines are flooded with incidents affecting areas from critical infrastructure and healthcare to retail and education, we have a great opportunity to address this challenge. Visit our ransomware solutions webpage to discover how to mitigate ransomware attacks , or get in touch with one of our Thales experts.

IBM Big Data Hub
DECEMBER 20, 2023
Hybrid cloud has become the IT infrastructure of choice, providing the interoperability and portability organizations need to access data where and when they need it. To capture the most value from hybrid cloud, business and IT leaders must develop a solid hybrid cloud strategy supporting their core business objectives.

IBM Big Data Hub
JUNE 7, 2022
For banks with multiple lines of business including retail and corporate clients, this becomes a daunting challenge to manage diverse technology, operational, brand and regulatory risk exposure with appropriate process, policies and compliance automation. It can be deployed on premises or in the cloud.

The Last Watchdog
APRIL 7, 2020
Here are key takeaways: Romance scams Like many modern companies, Zoosk, the popular San Francisco-based dating site, rests on infrastructure that’s predominantly cloud-based. Acohido is dedicated to fostering public awareness about how to make the Internet as private and secure as it ought to be. I’ll keep watch.

eSecurity Planet
JANUARY 28, 2022
Microsoft in November fended off a massive distributed denial-of-service (DDoS) attack in its Azure cloud that officials said was the largest ever recorded, the latest in a wave of record attacks that washed over the IT industry in the second half of 2021. Also read: How to Stop DDoS Attacks: 6 Tips for Fighting DDoS Attacks.

IBM Big Data Hub
APRIL 24, 2024
An online retailer always gets users’ explicit consent before sharing customer data with its partners. These are just some examples of how organizations support data privacy , the principle that people should have control of their personal data, including who can see it, who can collect it, and how it can be used.

The Last Watchdog
APRIL 7, 2021
The water plant hack, which took place in a Tampa Bay suburb a few days before Super Bowl LV, highlights how threat actors are taking advantage of the fact that companies are chasing after digital agility above all else. Financial institutions and online retailers have been the earlier adopters of passwordless solutions, for obvious reasons.

The Texas Record
OCTOBER 19, 2020
How to Convert Your Home Movie Tapes to Digital. It’s best to follow the LOCKSS (Lots Of Copies Keeps Stuff Safe) concept – keeping a digital copy on your hard drive, a backup drive, and on the cloud provides you some extra security in case of a drive failure or other catastrophic loss of the physical storage device. – Andrew.

Thales Cloud Protection & Licensing
AUGUST 7, 2018
If you have looked at our recently released annual Data Threat Report: Retail Edition , you understand this is not just hyperbole. retail sector needs to come to terms with some bad news. The retail sector is responding to the onslaught of breaches, with 84% of companies surveyed planning to increase IT security spending.

Thales Cloud Protection & Licensing
MARCH 10, 2021
Imagine a world where the retail value of your car actually grows over time – that’s now becoming a reality. Once you’ve figured out how to embed security at the device level, you need to next consider how to ensure security at the management and backend operations level. Cloud security. Management Platforms. Encryption.

eSecurity Planet
MARCH 22, 2023
Cloud Access Management: Even smaller organizations now use cloud resources, but most internal network controls do not extend to resources hosted outside of the network, such as Office 365, Google Docs, other software-as-a-service (SaaS) solutions, and even segregated branch office networks.

Schneier on Security
APRIL 12, 2018
Good article about how difficult it is to insure an organization against Internet attacks, and how expensive the insurance is. Companies like retailers, banks, and healthcare providers began seeking out cyberinsurance in the early 2000s, when states first passed data breach notification laws.

Reltio
MARCH 12, 2020
Check out some of the recent announcements: Postponed Conferences (Gartner Data & Analytics Summits, HIMSS) others going virtual (Google Cloud NEXT). COVID-19 is accelerating many companies' plans to transform to digital businesses. Companies asking employees to work from home. The pressure to move to digital has never been higher.
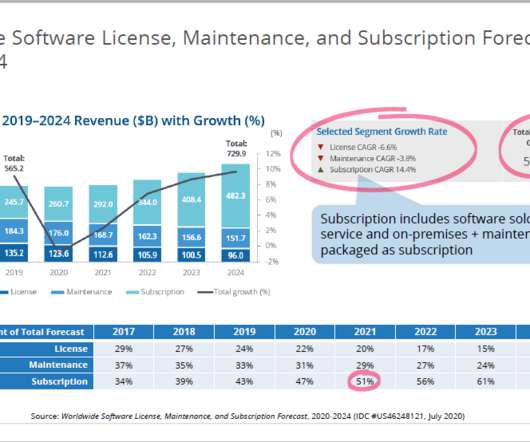
Thales Cloud Protection & Licensing
JUNE 23, 2021
Where Companies Fail and How to Avoid the Traps of Shifting to Subscriptions. Images credit: IDC presentation, Where Companies Fail and How to Avoid the Traps of Shifting to Subscriptions June 2021. . TRANSITIONING TO SUBSCRIPTIONS. Presented by Mark Thomason, IDC Research Director. ?Which Usership vs. Ownership .

The Last Watchdog
MAY 2, 2019
It grew steadily into a supplier of cloud-enabled security and productivity services, and today has some 250 employees servicing 60,000 SMBs worldwide. Growing reliance on cloud-based services, and third-party collaborations is only making it easier for threat actors. Last February, Dallas-based email encryption vendor Zix Corp.

The Last Watchdog
MARCH 1, 2019
SOAR, if you haven’t heard, is a hot new technology stack that takes well-understood data mining and business intelligence analytics methodologies — techniques that are deeply utilized in financial services, retailing and other business verticals – and applies them to cybersecurity. Demisto launched in May 2016.

Elie
MAY 30, 2018
This blog post survey the attacks techniques that target AI (artificial intelligence) systems and how to protect against them. This post is the fourth, and last, post in a series of four dedicated to providing a concise overview of how to use AI to build robust anti-abuse protections. first post. adversarial examples. this paper.

Thales Cloud Protection & Licensing
JULY 24, 2018
The 57 percent rate statistic is the highest of all verticals we measured in this year’s report (others include the healthcare industry, the retail industry, and the financial services industry) or any region surveyed. There also appears to be some confusion over how to best protect critical data.

IT Governance
MARCH 22, 2018
Such machine learning has been adopted in industries such as motoring, healthcare and retail. Malware is often communicated within encrypted web traffic, and sensitive data sent through Cloud systems, so the relevant tools need to be put in place to detect and prevent the use of encryption for masking malicious activity.

Elie
MAY 30, 2018
This blog post survey the attacks techniques that target AI (artificial intelligence) systems and how to protect against them. This post is the fourth, and last, post in a series of four dedicated to providing a concise overview of how to use AI to build robust anti-abuse protections. first post. adversarial examples. this paper.

IBM Big Data Hub
OCTOBER 5, 2022
In a manufacturing, distribution or retail context, this is the supply plan. Depending on the patterns of your business, predictive models can play a significant role in improving the accuracy of your demand plan, while also saving time through automation, as experienced by Arthrex , a global medical device company.

The Last Watchdog
APRIL 24, 2019
In an environment where a heating and ventilation subcontractor can pose an existential risk to a billion dollar retail chain – as infamously happened to Target – just knowing where to start assessing third party risk can be a challenge for any organization, Jordan told me. “We do white papers and thought leadership at conferences.

IT Governance
JUNE 8, 2023
Cyber criminals are constantly creating new attacks methods to outwit defences, meaning that the only consistent and effective way to thwart an attack is for the individual to understand how phishing works and how to identify the signs before clicking a malicious link.

eSecurity Planet
JANUARY 5, 2023
Also read: Ransomware Protection: How to Prevent Ransomware Attacks. Retailers have begun to launch digital goods available for purchase in virtual worlds. “Every organization, regardless of the size, keeps their data in at least two to three cloud environments,” said Normalyze CTO Ravi Ithal.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content