Jamf Event: Education recap
Jamf
APRIL 9, 2024
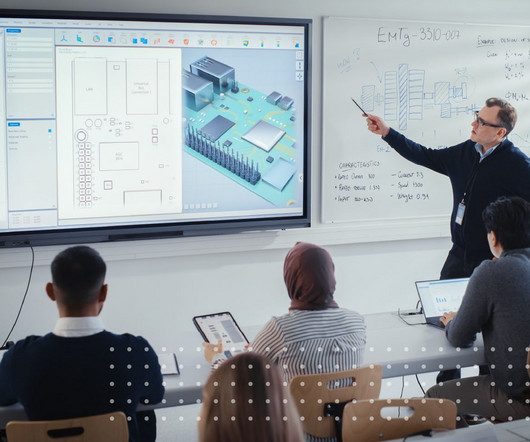
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.

Security Affairs
AUGUST 6, 2023
The Colorado Department of Higher Education (CDHE) finally disclosed a data breach impacting students, past students, and teachers after the June attack. In June a ransomware attack hit the Colorado Department of Higher Education (CDHE), now the organization disclosed a data breach.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Collibra
JUNE 27, 2023
1) How can institutions of higher education use data to start making strategic decisions? Get all the details in Collibra Data Intelligence Cloud for Higher Education , our helpful solution brief. Graduate to data intelligence It’s no secret that data is key to the educational mission. In 2020, the U.S.

eSecurity Planet
AUGUST 22, 2023
Remote access security is critical for protecting increasingly distributed work environments, ensuring that only authorized users can access your valuable information regardless of their location. We’ll cover a range of best practices for remote access security, from the simple and the practical to the more advanced.

The Last Watchdog
MAY 5, 2022
Let’s walk through some practical steps organizations can take today, implementing zero trust and remote access strategies to help reduce ransomware risks: •Obvious, but difficult – get end users to stop clicking unknown links and visiting random websites that they know little about, an educational challenge.
Hunton Privacy
NOVEMBER 7, 2022
On November 2, 2022, the ICO issued to the UK Department for Education (“ DfE ”) a formal reprimand following an investigation into the sharing of personal data stored on the Learning Records Service (“ LRS ”), a database which provides a record of pupils’ qualifications that the DfE has overall responsibility for.

Krebs on Security
OCTOBER 14, 2021
Louis Post-Dispatch ran a story about how its staff discovered and reported a security vulnerability in a Missouri state education website that exposed the Social Security numbers of 100,000 elementary and secondary teachers. Louis Post-Dispatch for reporting a security vulnerability that exposed teacher SSNs.

Krebs on Security
DECEMBER 3, 2021
Rarely do cybercriminal gangs that deploy ransomware gain the initial access to the target themselves. More commonly, that access is purchased from a cybercriminal broker who specializes in acquiring remote access credentials — such as usernames and passwords needed to remotely connect to the target’s network.
Security Affairs
NOVEMBER 21, 2023
Experts warn of a surge in NetSupport RAT attacks against education, government, and business services sectors. The most impacted sectors are education, government, and business services. In recent years, multiple threat actors, including the group TA569 , have been observed using the software as a Remote Access Trojan (RAT).

Security Affairs
DECEMBER 2, 2020
Online education giant K12 Inc. The education company Online education giant K12 Inc. is a for-profit education company that sells online schooling and curricula. is a for-profit education company that sells online schooling and curricula. “K12 Inc. .” Pierluigi Paganini.
Security Affairs
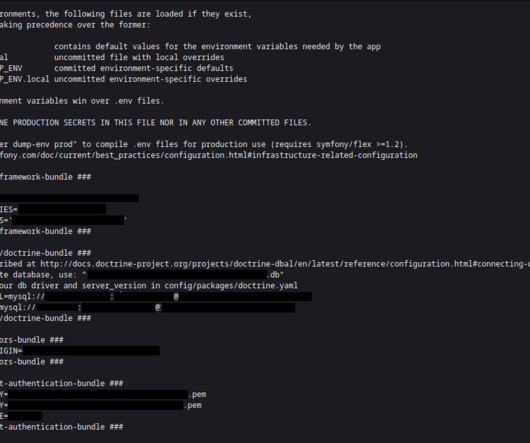
APRIL 25, 2023
A brand, best known for its lion roaring for over a century, has leaked access to its user data in Peru. And while the country is not that big of a market for the car maker, this discovery is yet another example of how big and well-known brands fail to secure sensitive data. env) hosted on the official Peugeot store for Peru.
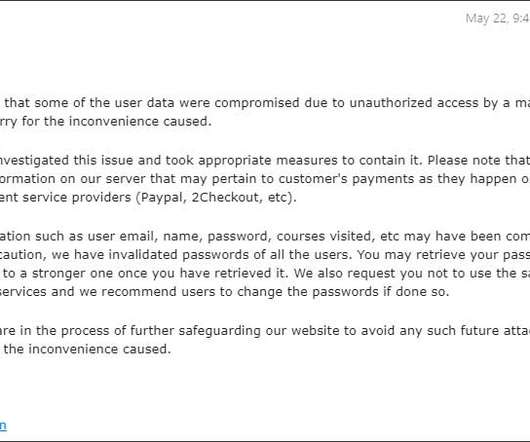
Security Affairs
MAY 24, 2020
The online education portal EduCBA discloses a data breach and is resetting customers’ passwords in response to the incident. Online education website EduCBA discloses a data breach, it has started notifying customers that in response to the incident it is resetting their passwords. Source BleepingComputer. Pierluigi Paganini.

Krebs on Security
FEBRUARY 22, 2022
Missouri Governor Mike Parson made headlines last year when he vowed to criminally prosecute a journalist for reporting a security flaw in a state website that exposed personal information of more than 100,000 teachers. Louis Post-Dispatch for reporting a security vulnerability that exposed teacher SSNs. In October 2021, St.

eSecurity Planet
MARCH 14, 2021
Network Access Control (NAC) helps enterprises implement policies for controlling devices and user access to their networks. NAC can set policies for resource, role, device and location-based access and enforce security compliance with security and patch management policies, among other controls. Auconet BICS.

Security Affairs
FEBRUARY 23, 2020
New Mexico sues Google for allegedly using the Google for Education platform to gather personal and private data from children. Google is facing a new lawsuit for allegedly using the Google for Education platform to gather personal and private data from students with an age of less than 13 years. Pierluigi Paganini.

IT Governance
SEPTEMBER 10, 2020
Staff and students can still access limited services, including email, office applications and video conference tools. This incident is the latest in a long line of cyber attacks on the education sector. A recent report found that many uni v ersities neglect basic cyber security best practices. Cyber Security as a Service.

The Last Watchdog
SEPTEMBER 6, 2023
Strong security measures become increasingly important as more people use this digital currency. Related: Currency exchange security issues For managing and keeping your Bitcoin assets, you must need a bitcoin wallet, which is a digital version of a conventional wallet. Select a reliable wallet. Use strong passwords, 2FA.

Security Affairs
MARCH 17, 2021
The FBI has issued an alert to warn about an increase in PYSA ransomware attacks on education institutions in the US and UK. The FBI has issued Tuesday an alert to warn about an increase in PYSA ransomware attacks against education institutions in the United States and the United Kingdom. Pierluigi Paganini.
Thales Cloud Protection & Licensing
OCTOBER 17, 2023
Cyber Security Awareness Month – Answering Google’s Most Commonly Asked Questions madhav Wed, 10/18/2023 - 05:25 This month is Cyber Security Awareness Month , highlighting how far security education needs to go in order to enable a secure interconnected world. Data Sovereignty What is data sovereignty?

The Last Watchdog
FEBRUARY 20, 2024
Related: The security case for AR, VR AI chatbots use natural language processing, which enables them to understand and respond to human language and machine learning algorithms. This widespread integration enhances accessibility and user engagement, allowing businesses to provide seamless interactions across various platforms.

The Last Watchdog
NOVEMBER 12, 2023
However, there’s still a long way to go to achieve deep interoperability of interconnected services in a way that preserves privacy and is very secure. It’s important that as consumers are shopping for these smart home devices that they learn to recognize the Matter trademark so that they can make educated decisions.”
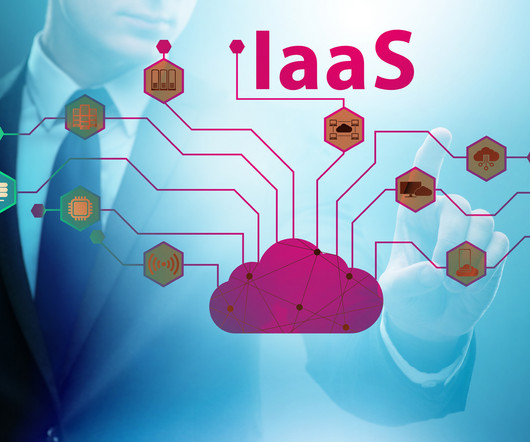
eSecurity Planet
DECEMBER 19, 2023
Infrastructure as a service security is a concept that assures the safety of organizations’ data, applications, and networks in the cloud. Understanding the risks, advantages, and best practices connected with IaaS security is becoming increasingly important as enterprises shift their infrastructure to the cloud.

Security Affairs
DECEMBER 4, 2020
A group of Iranian hackers gained access to a un unprotected ICS at an Israeli Water Facility and posted a video as proof of the hack. Researchers from industrial cybersecurity firm OTORIO revealed that a group of Iranian hackers gained access to a un unprotected ICS at the Israeli Water Facility. ” concludes the post.

The Last Watchdog
FEBRUARY 5, 2024
Fortunately, effective tools and wise best practices can help mitigate this this exposure enabling companies to indefinitely leverage Exchange Server as a productive, resilient and secure communications tool. The user interface is intuitive, making it accessible for users with varying levels of technical expertise. Backup strategies.

Security Affairs
APRIL 12, 2023
SAP April 2023 security updates include a total of 24 notes, 19 of which are new vulnerabilities. CVE-2023-28765 : An attacker with basic privileges in SAP BusinessObjects Business Intelligence Platform (Promotion Management) – versions 420, 430, can exploit the issue to access to lcmbiar file and further decrypt the file.

The Last Watchdog
JULY 1, 2022
This raises the concerns of corporate data security in remote working that still stand as a key challenge that organizations are trying to navigate, workforce productivity being the second. Managing endpoints securely . Tools and best practices.

Jamf
MARCH 30, 2021
The internet is an amazing resource filled with educational content, and the iPad has made it more accessible to students. Justin Payeur from National Education Technologies joined us to share the story of what’s next for security in schools with their new app on the Jamf Marketplace.

AIIM
JUNE 22, 2018
The threat of a hack is greater than it ever has been before with technology now reaching all parts of the world and granting access to the internet uniformly. In this article, we will examine how to educate your employees so that a lethal hack does not disrupt your business. It’s All About Passwords. It’s A Team Effort.

Security Affairs
APRIL 3, 2023
Western Digital disclosed a security breach, according to the company an unauthorized party gained access to multiple systems. Western Digital has shut down several of its services after discovering a security breach, the company disclosed that an unauthorized party gained access to multiple systems.

eSecurity Planet
OCTOBER 16, 2023
Public cloud security refers to protections put in place to secure data and resources in cloud environments shared by multiple users or organizations. Major cloud service providers have generally had good security , so cloud users can be pretty confident in the security of their data and applications if they get their part right.

IT Governance
NOVEMBER 24, 2021
They provide a cost-effective way to store data; and with the rise in hybrid workforces, they deliver a reliable way for employees to access information remotely. But as is often the case with technological solutions, the benefits of convenience comes with security risks. Phishing scams. Regulatory non-compliance.

Krebs on Security
JANUARY 31, 2020
11, 2019, two security experts at a company that had been hired by the state of Iowa to test the physical and network security of its judicial system were arrested while probing the security of an Iowa county courthouse, jailed in orange jumpsuits, charged with burglary, and held on $100,000 bail. On Thursday Jan.

eSecurity Planet
AUGUST 9, 2022
Regulatory compliance and data privacy issues have long been an IT security nightmare. GDPR (among other legal requirements in the EU and elsewhere) can expose multinational organizations to hefty financial penalties, additional rules for disclosing data breaches, and increased scrutiny of the adequacy of their data security.

The Last Watchdog
JULY 11, 2022
Essential security tool. Post Covid 19, these patterns are likely to become even more engrained as digitally remote work, education, healthcare and entertainment activities predominate. VPNs factor into this shift, as the burden on individual consumers to preserve privacy and secure their sensitive data is greater than ever.

CILIP
APRIL 15, 2024
CILIP Copyright COnference 2024 By Gary Horrocks THE summer 2023 issue of UKeiG’s open access journal, eLucidate , featured my reflections on the implications of a Members’ Day presentation by Ken Chad on the “library technology ecosystem". Ken notes there is “a dichotomy between the provision of library resources and learning resources.”

Security Affairs
APRIL 25, 2024
Cybersecurity and Infrastructure Security Agency (CISA) added the CVE-2022-38028 Microsoft Windows Print Spooler Privilege Escalation vulnerability to its Known Exploited Vulnerabilities (KEV) catalog. National Security Agency and Microsoft addressed it with the release of Microsoft October 2022 Patch Tuesday security updates.

eSecurity Planet
APRIL 24, 2023
Aqua Security’s cloud security research team recently found thousands of registries and artifact repositories exposed online, revealing more than 250 million artifacts and over 65,000 container images. “If attackers gain access to registries, they can propagate and potentially exploit the entire SDLC.”

The Last Watchdog
SEPTEMBER 25, 2023
If you’re a small business looking for the secret sauce to cybersecurity, the secret is out: start with a cybersecurity policy and make the commitment to security a business-wide priority. Taurins It’s also essential your business evaluates its technology and keeps it regularly updated to the latest security standards.
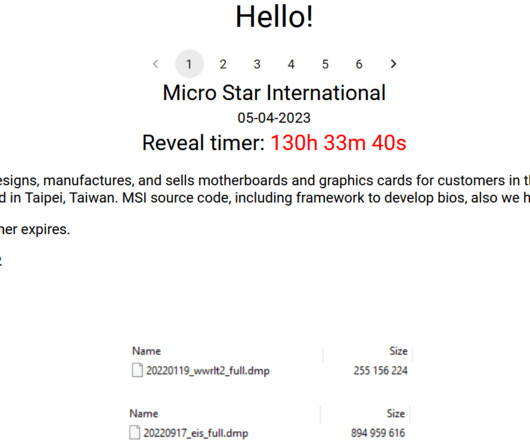
Security Affairs
APRIL 7, 2023
Multinational IT corporation MSI (Micro-Star International) confirms security breach after Money Message ransomware gang claimed the hack. Today MSI confirmed the security breach, it confirmed that threat actors had access to some of its information service systems. ” reads a statement published by the company.

IT Governance
OCTOBER 24, 2023
Incident details: An unauthorised party gained access to some employee email accounts and the information within them, including demographic, medical and financial information. It turned out that an unauthorised party had accessed and downloaded its business records, including files containing personal data.
Security Affairs
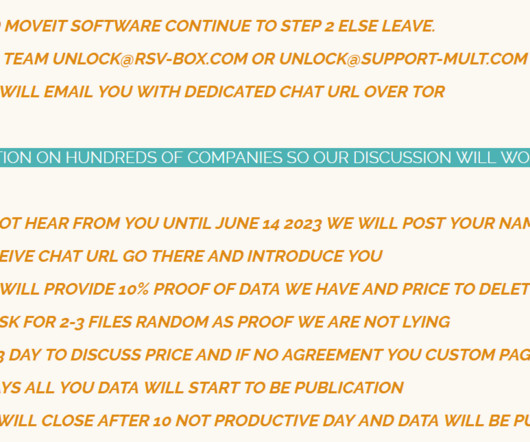
SEPTEMBER 24, 2023
educational nonprofit organization National Student Clearinghouse disclosed a data breach that impacted approximately 900 US schools. The security breach resulted from a cyber attack exploiting a vulnerability in the MOVEit managed file transfer (MFT).- The issue occurred on or around May 30, 2023.”

Thales Cloud Protection & Licensing
JANUARY 11, 2023
The Most Popular Data Security Webinars of 2022: Sovereignty, Cloud Security and Compliance Top the List. Throughout 2022, Thales hosted more than 40 webinars on a wide variety of cybersecurity topics, including, cloud security, data sovereignty, compliance, data threat trends, and rethinking approaches to role-based authentication.

IT Governance
JANUARY 9, 2024
They accessed 41.5 million customers’ data having gained access via a vulnerability in Hathaway’s Laravel web application framework. million individuals affected HealthEC LLC, a health technology company, has announced that it suffered a data breach in July 2023, in which systems were accessed and files were copied.

IT Governance
OCTOBER 21, 2021
The need for experienced and qualified cyber security professionals is a highlight of Cybersecurity Career Awareness Week , led by NICE (National Initiative for Cybersecurity Education). Cyber security focuses on protecting computer systems from unauthorised access or being otherwise damaged. UK skills gap.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content