Hundreds of Millions of Dell Users at Risk from Kernel-Privilege Bugs
Threatpost
MAY 4, 2021
The privilege-escalation bug remained hidden for 12 years and has been present in all Dell PCs, tablets and notebooks shipped since 2009.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Threatpost
MAY 4, 2021
The privilege-escalation bug remained hidden for 12 years and has been present in all Dell PCs, tablets and notebooks shipped since 2009.

Data Matters
MAY 6, 2022
Earlier this month, OCR released an RFI seeking public input on two requirements of the Health Information Technology for Economic and Clinical Health Act of 2009 (HITECH Act), as amended. RFI Regarding Recognized Security Practices. Comments must be submitted by June 6, 2022. Cybersecurity Industry Newsletter.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

CILIP
MARCH 2, 2021
Brexit means new risks for the sector. That means greater risk aversion, more obstacles and more costs for library and information professionals. Risk and orphan works. Naomi wrote a report in 2009 called In From the Cold which found there were in the region of 50 million orphan works in the UK sector. Risk manage it.

The Guardian Data Protection
JANUARY 22, 2020
The Australian government has spent $1.97bn since the system was introduced as the e-health record in 2009 A decade since it was first announced, the federal government has spent close to $2bn on its troubled My Health Record system, and half of the 23m records created lie empty almost a year after the government made the system opt-out.

Krebs on Security
MARCH 22, 2022
ChronoPay specializes in providing access to the global credit card networks for “high risk” merchants — businesses involved in selling services online that tend to generate an unusually large number of chargebacks and reports of fraud, and hence have a higher risk of failure. Click to enlarge.

The Last Watchdog
AUGUST 1, 2023
Survey Highlights As part of the study sponsored by AppViewX, EMA gathered data from multiple sources for this research report, including Google Trends from 5/6/2018 to 4/30/2023, Stack Exchange from 1/1/2009 to 12/31/2022, and Shodan in May 2023 focused on servers with SSL/TLS certificates on port 443.

ARMA International
SEPTEMBER 27, 2021
Here, Part 3 discusses how to manage the various DT risks. This discussion includes methods, tools, and techniques such as using personae and identifying use cases that have high business value, while minimizing project risks. This part also discusses managing CS risks such as ransomware, privacy, change management, and user adoption.

eSecurity Planet
FEBRUARY 10, 2023
The LookingGlass scoutPrime threat intelligence platform (TIP) integrates enterprise-grade external security threat information with information on internal architecture and security information to create actionable, prioritized risk scores for threats. This article provides more in-depth information on the product and its features.
Security Affairs
OCTOBER 23, 2023
billion Aadhaars issued by the UIDAI since this ID service launched in 2009, this system represents one of the largest biometric ID programs on the planet, according to a report published by think tank Brookings Institution. With roughly 1.4

Krebs on Security
APRIL 7, 2020
“We released a security advisory in June of 2009 and a security update that helps keep customers safe. Faced with either or both of these scenarios, most affected companies probably decided the actual risk of not applying these updates was comparatively low. Further reading: Mitigating the Risk of DNS Namespace Collisions (PDF).

Hunton Privacy
JUNE 22, 2010
On June 17, 2010, the French data protection authority (the “CNIL”) published its Annual Activity Report for 2009 (the “Report”) in which it outlines some of its priorities for the upcoming year. In February 2009, the CNIL published a report on online targeted advertising. When transferring personal data to the U.S.

Security Affairs
AUGUST 10, 2019
The vulnerability, tracked as CVE-2009-0692 , could be exploited by an attacker to crash the ISC DHCP client and execute arbitrary code with the permissions of the client. Avaya did not address the vulnerability issue in some of its VoIP devices by applying the necessary patches that were released after the discovery of the flaw in 2009.
Security Affairs
MAY 13, 2023
Founded in 2009, the company provides luggage and passenger transportation services on many popular hiking routes, including the famous Santiago de Compostela pilgrimage trail. Leaking employee credentials might put the company at risk of targeted cyberattacks. Why is leaking personal data dangerous? One of them is identity theft.

Security Affairs
OCTOBER 1, 2019
The experts found an unprotected Elasticsearch cluster that was containing personally identifiable information on Russian citizens spanning from 2009 to 2016. “The first database contained more than 14 million personal and tax records from 2010 to 2016, and the second included over 6 million from 2009 to 2015.”
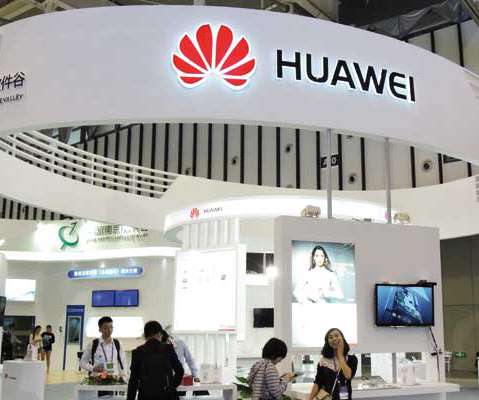
Security Affairs
OCTOBER 10, 2020
Orange Belgium is using Huawei equipment since 2007 for its mobile network in Belgium and Luxembourg, while the collaboration between Proximus and the Shenzhen-based company started in 2009 for the progressive upgrading of its network. There’s also a growing concern about Huawei’s capacity to produce its equipment,” the source added.

Hunton Privacy
MAY 1, 2009
The previous compliance date was May 1, 2009, which was an extension from the original deadline of November 1, 2008. " On March 20, 2009, the FTC published the Red Flags Rule Compliance Guide to assist organizations that must comply with the Red Flags Rule. The FTC’s news release is available here.

Security Affairs
OCTOBER 21, 2021
The two individuals, Aleksandr Skorodumov (33) of Lithuania, and Pavel Stassi (30) of Estonia, administrated the bulletproof hosting service between 2009 and 2015. Prosecutions like this one increase the costs and risks to cybercriminals and ensure that they cannot evade responsibility for the enormous injuries they cause to victims.”.

Data Matters
MARCH 28, 2022
OCR’s reminders and recommendations for regulated entities include to: assess and reduce risks and vulnerabilities to the availability of ePHI, which is defined as “the property that data or information is accessible and useable upon demand by an authorized person” pursuant to the HIPAA Security Rule. 45 CFR 164.308(a)(5)(i).

The Last Watchdog
APRIL 18, 2019
Imposing just the right touch of policies and procedures towards mitigating cyber risks is a core challenge facing any company caught up in digital transformation. Brinqa was founded in 2009 by Amad Fida and Hilda Perez, industry veterans seeking to leverage their collective expertise in risk management and identity and access management.

Security Affairs
MARCH 8, 2022
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities , FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog. Follow me on Twitter: @securityaffairs and Facebook.
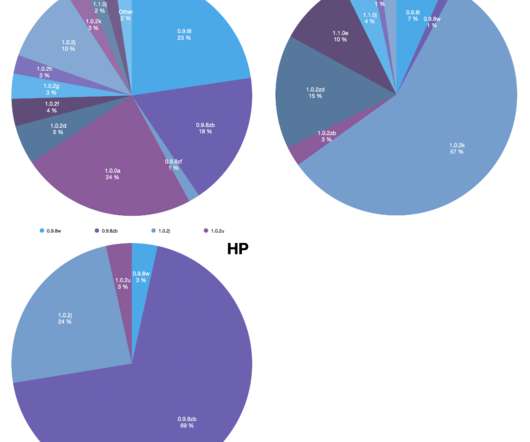
Security Affairs
NOVEMBER 25, 2022
that dates back to 2009. “A ‘trust-but-verify’ approach is the best way to deal with SBOM failures and reduce supply chain risks.” “A ‘trust-but-verify’ approach is the best way to deal with SBOM failures and reduce supply chain risks.” Some Lenovo devices used the version 1.0.0a that dates back 2012.

The Security Ledger
JANUARY 23, 2024
And yet, the awareness of cyber security risks – from phishing and social engineering attacks to software supply chain compromises – remains low. Software is now central to the operation of our economy – as digital transformation washes over every industry. Nobody knows that better than our guest this week.

Schneier on Security
JULY 23, 2019
More imagination leads to more movie-plot threats -- which contributes to overall fear and overestimation of the risks. Last month, at the 2009 Homeland Security Science & Technology Stakeholders Conference in Washington D.C., And that doesn't help keep us safe at all.
Security Affairs
MARCH 15, 2023
The vulnerability left the company at risk from cyberattacks over an extended period of time. Cybernews researchers advise the company to take swift action to mitigate risks and prevent future breaches by changing leaked credentials. According to its own estimates, Safran Group ’s revenue for 2022 was above €19 billion.

HL Chronicle of Data Protection
JANUARY 22, 2020
The PDPO Review Paper represents the first proposal for reform of the PDPO since the consultation in 2009-10 that led to the introduction of Hong Kong’s direct marketing controls in 2013. From a global perspective, data protection regulation has moved forward significantly since that time, so a review of the PDPO is timely.

Security Affairs
MAY 2, 2019
The availability of 10KBLAZE PoC exploits for old SAP configuration issue poses a severe risk of attacks for business applications. The risk of cyber attacks against SAP systems is increased after security researchers released PoC exploits for old SAP configuration flaws. ” reads the analysis published by Onapsis.

Security Affairs
MAY 15, 2019
Five Security Notes included in SAP Security Patch Day for May 2019 addressed missing authorization checks in SAP products, including Treasury and Risk Management, Solution Manager and ABAP managed systems, dbpool administration, and Enterprise Financial Services. . Two flaws received a CVSS score of 6.3, ” adds Onapsis.

Security Affairs
JULY 10, 2019
The experts at the healthcare cybersecurity firm CyberMDX have found some flaws in the firmware of the anesthesia machines, the issues could expose patients to serious risks. GE Healthcare has determined that this scenario does not provide access to data and does not introduce clinical hazard or patient risk.”

IT Governance
FEBRUARY 14, 2024
Tell us a bit about what you do for IT Governance I’ve been head of channel since December 2019, though have worked for the Group since October 2009. We are the market leader in data privacy and cyber security risk management solutions, so it makes sense to partner with us. We put those questions to channel sales director Sophie Sayer.

IG Guru
MAY 28, 2019
Stiles received the 2016 Pulitzer Prize for History, the 2010 Pulitzer Prize for Biography and the 2009 National Book Award for Nonfiction. StilesMay 7 via the Washington Post T.J. He is a member of the governing boards of the Society of American Historians and the Organization of American Historians.

Thales Cloud Protection & Licensing
AUGUST 22, 2019
It’s an understatement to say things have changed a lot since 2009, especially the cyber landscape. But will investment in its own technology infrastructure be commensurate with risks it faces? Without support and proper investment, the institutions they protect will remain at risk.

IT Governance
OCTOBER 29, 2018
Introduced in 2009 to help organisations manage personal information and comply with data protection laws, BS 10012 was until recently a niche standard, but it has garnered fresh attention since the EU GDPR (General Data Protection Regulation) took effect. Take a risk-based approach to data privacy management.

Hunton Privacy
JUNE 8, 2009
The template is entitled “A Do-It-Yourself Prevention Program for Businesses and Organizations at Low Risk for Identity Theft.” To take advantage of the template, an entity first must assess whether it is at low risk for identity theft. The assessment and the resulting conclusion must be documented in the template.

AIIM
OCTOBER 30, 2017
However, human error puts both consistency and accuracy at risk. Scan workflows that automatically sends the digital document to a pre-defined, authorized destination, remove the risk of the document getting lost or getting into the wrong hands. What are Automated Scan Workflows? Mr. Koelewijn is married and has two children.

eSecurity Planet
FEBRUARY 8, 2021
Netsparker was launched in 2009 to alleviate frustrations around manual vulnerability verification processes. It exploits the risks in a black box setting so it can obtain proof of the vulnerabilities without causing any disruption to your live deployment environment. . About Netsparker. Notable features.

Hunton Privacy
APRIL 13, 2009
The mere increased risk of identity theft following a data breach is sufficient to give the data subjects standing to bring a lawsuit in federal court but, absent actual identity theft or other actual harm, claims against the data owner and its service provider for negligence and breach of contract cannot survive, a federal judge ruled this month.

ChiefTech
JANUARY 12, 2008
©2005-2009. service model risk blown away - Google and Postini I noticed in this case study about a law firms decision to pick Google Apps for email and collaboration over Microsoft Exchange or IBM Lotus Domino , that they mention Google has acquired a company called Postini (actually back last year ).

Data Protection Report
OCTOBER 1, 2019
In January 2009, the OPC issued Guidelines for processing personal data across borders setting out its interpretation that a “transfer” of personal information by an organization for processing is a “use” and not a “disclosure” of that personal information. What’s Old is New Again.

Hunton Privacy
OCTOBER 5, 2018
Together, Regulations S-ID and S-P are designed to require covered entities to help protect customers from the risk of identity theft and to safeguard confidential customer information. The settlement represents the first SEC enforcement action brought under Regulation S-ID. The Identity Theft Red Flags Rule.

DLA Piper Privacy Matters
JUNE 13, 2018
7] See the Working Party 29 Opinion 5/2009 on online social networking. The possible liability of administrators is not entirely surprising. 7] The trend regarding social networks seems to be clear – Establish a (joint) liability of as many (joint) controllers as possible. 5] [link]. [6] 6] See case C?131/12,

Security Affairs
SEPTEMBER 12, 2019
According to the researchers, almost any mobile phone model is vulnerable to the SimJacker attack because it leverages a component on SIM cards and its specifications are the same since 2009. ” states the post. This compromises the security and trust of customers, mobile operators, and impacts the national security of entire countries.”

Hunton Privacy
AUGUST 10, 2017
According to the attorneys general, Nationwide and Allied had failed to deploy a critical software patch that was released in 2009 to address the vulnerability. hiring an independent third party to perform a patch management audit on an annual basis.

Data Matters
JULY 15, 2020
Regulators are monitoring these developments with growing interest and with an eye to potential risks to customers and markets as well as their ability to supervise regulated firms and their operations. In addition, the European Banking Authority (the EBA) has issued detailed guidelines on outsourcing by such firms. Data security.

Hunton Privacy
JULY 30, 2009
On July 29, 2009, the Federal Trade Commission ("FTC") announced another three-month delay in the enforcement of the provision of Identity Theft Red Flags and Address Discrepancies Rule (the "Rule") that requires creditors and financial institutions to implement an Identity Theft Prevention Program.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content