WEIS 2021 Call for Papers
Schneier on Security
FEBRUARY 18, 2021
The 20th Annual Workshop on the Economics of Information Security (WEIS 2021) will be held online in June. We just published the call for papers.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
FEBRUARY 18, 2021
The 20th Annual Workshop on the Economics of Information Security (WEIS 2021) will be held online in June. We just published the call for papers.

Schneier on Security
JUNE 16, 2023
I’m just back from the sixteenth Workshop on Security and Human Behavior , hosted by Alessandro Acquisti at Carnegie Mellon University in Pittsburgh. For the past decade and a half, this workshop has been the most intellectually stimulating two days of my professional year. This year’s schedule is here.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Schneier on Security
JUNE 4, 2021
Today is the second day of the fourteenth Workshop on Security and Human Behavior. SHB is a small, annual, invitational workshop of people studying various aspects of the human side of security, organized each year by Alessandro Acquisti, Ross Anderson, and myself. This year’s schedule is here.

Schneier on Security
MAY 31, 2022
Today is the second day of the fifteenth Workshop on Security and Human Behavior , hosted by Ross Anderson and Alice Hutchings at the University of Cambridge. For the past decade and a half, this workshop has been the most intellectually stimulating two days of my professional year.

Hunton Privacy
JANUARY 10, 2018
On January 9, 2018, the FTC issued a paper recapping the key takeaways from the FTC’s and National Highway Traffic Safety Administration’s June 2017 workshop on privacy and security issues involving connected cars. The workshop featured representatives from consumer groups, industry, government and academia.

Schneier on Security
JUNE 19, 2020
Today is the second day of the thirteenth Workshop on Security and Human Behavior. SHB is a small, annual, invitational workshop of people studying various aspects of the human side of security, organized each year by Alessandro Acquisti, Ross Anderson, and myself.

Schneier on Security
JUNE 7, 2023
New paper: “ Lessons Lost: Incident Response in the Age of Cyber Insurance and Breach Attorneys “: Abstract: Incident Response (IR) allows victim firms to detect, contain, and recover from security incidents. It should also help the wider community avoid similar attacks in the future.

Schneier on Security
JUNE 6, 2019
Today is the second day of the twelfth Workshop on Security and Human Behavior , which I am hosting at Harvard University. SHB is a small, annual, invitational workshop of people studying various aspects of the human side of security, organized each year by Alessandro Acquisti, Ross Anderson, and myself.

HL Chronicle of Data Protection
NOVEMBER 19, 2018
The Federal Trade Commission (FTC) recently published a paper recapping its December 2017 Informational Injury Workshop. The paper noted that several important points emerged from the workshop: Informational Injuries: Examples and Harms. More Research Needed.
Adam Shostack
DECEMBER 7, 2019
Earlier this year, I helped to organize a workshop at Schloss Dagstuhl on Empirical Evaluation of Secure Development Processes. I’m also pleased to say that the workshop report is now available at [link].

Schneier on Security
MAY 25, 2018
I'm at Carnegie Mellon University, at the eleventh Workshop on Security and Human Behavior. SHB is a small invitational gathering of people studying various aspects of the human side of security, organized each year by Alessandro Acquisti, Ross Anderson, and myself. Next year, I'll be hosting the event at Harvard.

Hunton Privacy
OCTOBER 22, 2018
The Paper listed several examples of informational injuries, including medical identity theft, doxing, disclosure of private information and erosion of trust, and emphasized that the risks of such injuries should be balanced against the value of the information collection. whether the data at issue is anonymized or identifiable.

Hunton Privacy
DECEMBER 6, 2016
On November 30, 2016, the Centre for Information Policy Leadership (“CIPL”) at Hunton & Williams LLP issued a white paper on The One-Stop-Shop and the Lead DPA as Co-operation Mechanisms in the GDPR (the “White Paper”). Other “concerned DPAs” will continue to have a role in addressing relevant data protection matters.
Security Affairs
MAY 16, 2021
The chipmaker AMD published guidance for two new attacks against its SEV ( Secure Encrypted Virtualization ) protection technology. The findings about the two attacks will be presented by two research teams at this year’s 15th IEEE Workshop on Offensive Technologies (WOOT’21). Follow me on Twitter: @securityaffairs and Facebook.
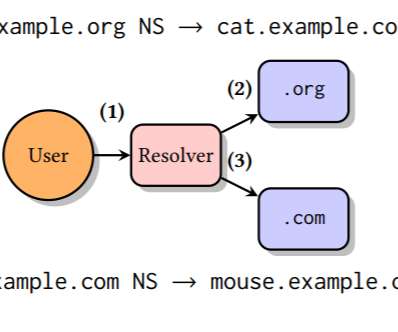
Security Affairs
MAY 9, 2021
” reads the research paper published by the experts. The researchers disclosed the tsuNAME flaw during the DNS OARC35 workshop and shared their findings with impacted organizations giving 90 days to address it before the vulnerability was disclosed. queries/s).” Follow me on Twitter: @securityaffairs and Facebook.

Security Affairs
AUGUST 8, 2020
In December 2019, the carmaker announced a partnership with the 360 Group to strengthen car IT security for the industry. We analyze the security of Mercedes-Benz cars. ” reads the research paper. ” reads the research paper. ” the paper concluded. Pierluigi Paganini.

Adam Shostack
JULY 26, 2019
There was a really interesting paper at the Workshop on the Economics of Information Security. The paper is “ Valuing CyberSecurity Research Datasets.” ” The paper focuses on the value of the IMPACT data sharing platform at DHS, and how the availability of data shapes the research that’s done.

Everteam
MARCH 14, 2019
This is to facilitate and accelerate the exchange of electronic documents and audit results with the entities supervised by the Bureau through the Governmental Secured Network (GSN) and the National Information Center (NIC). The overall progress includes managing and archiving documents with the application of security standards.

Hunton Privacy
OCTOBER 6, 2010
On September 29, 2010, the Centre for Information Policy Leadership (the “Centre”) hosted a pre-conference workshop at the International Association of Privacy Professionals (”IAPP”) Privacy Academy in Baltimore, Maryland.

Hunton Privacy
JUNE 30, 2014
The Centre for Information Policy Leadership at Hunton & Williams (the “Centre”) has published a white paper entitled A Risk-based Approach to Privacy: Improving Effectiveness in Practice. This is the first paper in the Centre’s new multi-year Privacy Risk Framework Project.

Everteam
DECEMBER 27, 2022
1 workshop on Solution trade show. 1 white paper (link to landing page). The role of IT in the implementation of an Information Governance program” or the need to control the data and document information assets, in a clean and secure manner. Content created for you on 2022. . 2 Webinars. 1 Documation exhibition.

Hunton Privacy
JANUARY 20, 2023
On January 20, 2023, The Centre for Information Policy Leadership (“CIPL”) at Hunton Andrews Kurth published “Digital Assets and Privacy,” a discussion paper compiling insights from workshops with CIPL member companies that explored the intersection of privacy and digital assets, with a particular focus on blockchain technology.

Schneier on Security
MARCH 31, 2024
Of course it was before 2008, when we created the Security and Human Behavior workshop. It was well before 2001, when we created the Workshop on Economics and Information Security. I know I was at the Fast Software Encryption workshop in December 1993, another conference he created. And he read it.

Everteam
MARCH 14, 2019
This is to facilitate and accelerate the exchange of electronic documents and audit results with the entities supervised by the Bureau through the Governmental Secured Network (GSN) and the National Information Center (NIC). The overall progress includes managing and archiving documents with the application of security standards.

Hunton Privacy
MARCH 11, 2009
The Federal Trade Commission, the Asia-Pacific Economic Cooperation forum, and the Organisation for Economic Co-operation and Development are hosting a multinational workshop on “Securing Personal Data in the Global Economy” in Washington, D.C. on March 16-17, 2009. Continue Reading…

AIIM
MARCH 16, 2021
During this step, conduct interviews, surveys, or workshops to gain input from business, IT, and records management stakeholders. Look at paper-reduction initiatives and assess how scanning projects can use extracted or OCRed text to pre-fill Metadata fields or forms to accelerate the digitization of routine processes.

IBM Big Data Hub
APRIL 25, 2024
This transformation entails replacing manual, paper-based workflows with digital systems that use technologies like Robotic Process Automation (RPA) for routine tasks. This might include streamlining payroll processes, digitizing HR operations or automating invoicing procedures.

Hunton Privacy
DECEMBER 16, 2014
In light of these new references, Thomas outlined the Centre’s Privacy Risk Framework project, including references to the Paris and Brussels workshops and the second white paper of the project, and explained the link between risk and accountability.

Hunton Privacy
NOVEMBER 30, 2010
Marty Abrams shared this paper on November 30, 2010, at the European Data Protection and Privacy Conference in Brussels and plans to present the paper on December 1, 2010, at the Organization for Economic Cooperation and Development. Read the white paper.

Hunton Privacy
MARCH 12, 2013
On March 8, 2013, the Federal Trade Commission issued a staff report entitled Paper, Plastic… or Mobile? An FTC Workshop on Mobile Payments (the “Report”). The Report is based on a workshop held by the FTC in April 2012 and highlights key consumer and privacy issues resulting from the increasingly widespread use of mobile payments.

Archive-It
JUNE 15, 2022
Register now to secure your place and benefit from the early bird fee. Learn more about the research papers, keynotes, workshops, and tutorials being offered @jcdl2022. Upcoming iPRES Conference. Registration for iPres 2022 is now open! Upcoming JCDL Conference. What we’re reading.

Hunton Privacy
JULY 20, 2012
This led to a 2004 multistakeholder workshop in Berlin that adopted the “Berlin Memorandum,” which in turn led to a white paper by the Article 29 Working Party on multilayered notices. The results of that work were released at a 2006 meeting of OECD Working Party on Information Security and Privacy.

Data Protection Report
DECEMBER 6, 2017
The Board has been active since its establishment, working on draft regulations, seeking opinions and comments from public and private institutions on those drafts, publishing user-friendly manuals, and organizing meetings, conferences and workshops to hold discussions. paper records vs. digital records).

Hunton Privacy
OCTOBER 5, 2016
In September, the Centre for Information Policy Leadership (“CIPL”) held its second GDPR Workshop in Paris as part of its two-year GDPR Implementation Project. Since the inaugural workshop in March 2016 in Amsterdam, participation in the project has grown significantly. Risk-based Enforcement and Oversight by the DPAs.
Hunton Privacy
SEPTEMBER 27, 2021
In May 2021 , NIST released a draft white paper that summarized its review of the currently available confidence mechanisms for the security of consumer IoT devices and in August 2021 , NIST released a draft white paper that detailed draft baseline security criteria for consumer IoT devices.

The Last Watchdog
MAY 24, 2023
Zero trust networking architecture (ZTNA) is a way of solving security challenges in a cloud-first world. The 4th Annual Multi-Cloud Conference and Workshop on ZTNA is an upcoming event for anyone interested in how the federal government is advancing standards in ZTNA. federal government or not. Let’s look at each of those five.

Hunton Privacy
FEBRUARY 13, 2017
On March 6 and 7, 2017, the Centre for Information Policy Leadership (“CIPL”) at Hunton & Williams LLP and over 100 public and private sector participants in CIPL’s GDPR Implementation Project will convene in Madrid, Spain, for CIPL’s third major GDPR implementation workshop.

Hunton Privacy
MARCH 15, 2016
On March 16, 2016, the Centre for Information Policy Leadership (“CIPL”) at Hunton & Williams LLP will co-host a one-day workshop in Amsterdam, Netherlands, together with the Dutch Ministry of Security and Justice, to kick off a new long-term CIPL project on the implementation of the EU General Data Protection Regulation (“GDPR”).

The Falcon's View
AUGUST 29, 2017
A month into the role as security lead for the Mid-Atlantic, where I was billable on day 1, the managing director left and a re-org merged us in with a different region where there was already a security lead. 2 of 3 sales reps left and the remaining person was unable and unwilling to sell security. on 10/10/10.
Adam Shostack
APRIL 23, 2020
This week’s threat model Thursday looks at an academic paper, Security Threat Modeling: Are Data Flow Diagrams Enough? The short (4 page), readable paper looks at the strengths and weaknesses of forms of DFDs, and what we might achieve with variations on the form and different investments of effort.

HL Chronicle of Data Protection
OCTOBER 25, 2018
Department of Homeland Security (DHS) earlier this month. Consistent with the U.S. Cybersecurity recommendations for devices that have already received clearance or approval from FDA are provided in FDA’s guidance: “ Postmarket Management of Cybersecurity in Medical Devices ” (postmarket cybersecurity guidance).

ForAllSecure
APRIL 7, 2021
Welcome to the hacker mind and original podcast from for all secure, it's about challenging our expectations about the people who hack for a living. I've got a lot of industry certifications, but having all those paper degrees proved to be a poor equivalent to having actual hands on experience in information security.

ForAllSecure
APRIL 7, 2021
Welcome to the hacker mind and original podcast from for all secure, it's about challenging our expectations about the people who hack for a living. I've got a lot of industry certifications, but having all those paper degrees proved to be a poor equivalent to having actual hands on experience in information security.

Brandeis Records Manager
SEPTEMBER 10, 2015
Likewise, the ICRM exam preparation workshop—which I’d highly recommend to prospective candidates—gave me a bead on what subject areas to target, especially for the management part, which can come across at first glance as a pan-MBA undertaking. BYOD can introduce threats to the security of your organization’s information.”.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content