Accelerating Data Security and Manufacturing Production for Medical Sensors by 20x with nTropy.io and Thales
Thales Cloud Protection & Licensing
AUGUST 21, 2023
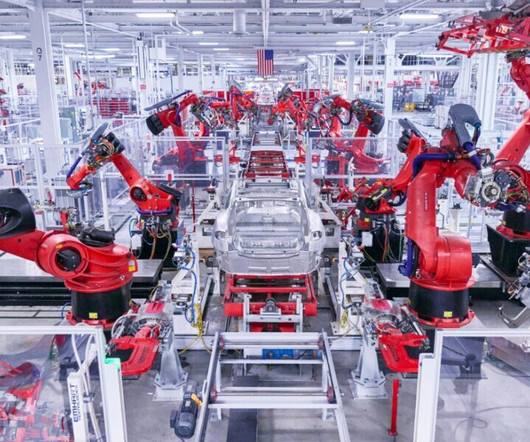
Accelerating Data Security and Manufacturing Production for Medical Sensors by 20x with nTropy.io Each device relies on wireless data transmission to relay collected data back to the patient’s phone or other monitoring tool. They offer security solutions to clients in MedTech, V2X, and Industrial manufacturing.












































Let's personalize your content