Jamf Event: Education recap
Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.

Thales Cloud Protection & Licensing
OCTOBER 5, 2022
Global October Cybersecurity Events: Where You Can Find Thales. The summer is now over, and October is a month full of cybersecurity events for Thales around the world. Below are just some of the events Thales will be at over the next few weeks. Les Assises turns 22 this year, and the event motto is "In 2022, We Speed Up!"
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

ForAllSecure
JUNE 7, 2023
We have 4 upcoming events planned for June 2023: Mayhem Unleashed Webinar: Discover our Next Generation Security Testing Solution DevSecOps Roundtable CyberSecurity Summit Hartford ForAllSecure APFT (Adversary, Penetration, and FuzzTesting) Training Read on to learn more about June’s events. We hope to see you there!

Security Affairs
APRIL 30, 2023
Thales cybersecurity researchers have shown this week how they seized control of a European Space Agency (ESA) satellite. Credit: ESA – European Space Agency The offensive cybersecurity team at Thales demonstrated how to take control of the ESA satellite, the is considered the world’s first ethical satellite hacking exercise.

Thales Cloud Protection & Licensing
JANUARY 28, 2020
An extension of the celebration for Data Protection Day in Europe, Data Privacy Day functions as the signature event of the National Cyber Security Centre’s ongoing education and awareness efforts surrounding online privacy. January 28, 2020 marks the 13th iteration of Data Privacy Day. A Streamlined Data Security Strategy.

The Last Watchdog
JANUARY 13, 2021
The question isn’t whether we should educate children about online safety, but how we can best inspire them to learn to be thoughtful, careful, and safe in the cyber world for their lifetime. I’ve also been brought in to host virtual reading events with the book for corporate and nonprofit efforts.

CILIP
JANUARY 8, 2024
Children’s author Julia Donaldson joins the Great School Libraries Campaign and shares how everyone can help to ensure a school library in every school in a new video. CILIP advocates for librarians and libraries We support and develop our members and our sector, through advocacy campaigns, events and resources aimed at the general public.

CILIP
MARCH 4, 2024
The forum was a unique opportunity for both groups to hear from each other on the skills that librarians and information managers will need in the future, and the opportunity it brings to libraries to take the lead in policy and education around AI. The day was made possible with sponsorship from CB Resourcing and WF Education.

eSecurity Planet
MARCH 15, 2021
Sources of additional could be configuration management databases (CMDBs), orchestration tools, system inventories, traffic add events logs, firewalls and SIEM , and load balancers. . Educate all team members about the purpose and functionality of microsegmentation. Integrate logs, events, and threats. Description .

IBM Big Data Hub
NOVEMBER 30, 2023
Attend industry events: Participate in conferences, webinars, speaking engagements, award competitions and other events to establish a presence and engage with potential candidates. Conduct background checks: Include employment verification, education verification and criminal record checks.

eSecurity Planet
JUNE 23, 2023
Also read: 9 Best Penetration Testing Tools 24 Top Open Source Penetration Testing Tools How to Implement a Penetration Testing Program in 10 Steps Third-Party Vendor Tests: Challenges and Maximizing Value Many organizations prefer to perform in-house penetration tests because of the challenges with third-party vendors.

The Last Watchdog
JANUARY 23, 2024
Throughout the week, NCA will emphasize the critical significance of digital privacy for both consumers and businesses through a series of educational webinars featuring experts from various industries. “Knowing how to safeguard your personal information has never been more important than it is today.

AIIM
SEPTEMBER 21, 2021
“Do our training courses offer the most practical and relevant educational experience possible?” The overwhelming response was more practical, how-to-oriented training and more opportunities to connect with other information professionals. Best-in-Class Education, Available Anywhere, Anytime. How to Digitize Paper Documents.

IBM Big Data Hub
OCTOBER 2, 2023
If proven possible, then future use cases of AI models could be explored, like matching users to potential employment and education opportunities based on their skill profiles. Chamber Foundation to demonstrate they had thoughtfully considered how to help mitigate potential risks associated with using AI.

CILIP
APRIL 25, 2024
Although her educational background and initial work was in education, a career in libraries is where her professional interests and ambitions came together. “I I enjoy challenges, adapting my skills and learning new ones, and I’ve always been an academic, so most of my professional life has been in education.”
Security Affairs
JANUARY 22, 2024
Attackers often exploit current events or emergency situations to elicit emotional responses and induce victims to act hastily without carefully evaluating the legitimacy of the communications. How to Protect Yourself To protect against these evolving threats, it is crucial to adopt good cybersecurity practices.

HL Chronicle of Data Protection
MARCH 29, 2019
Please join us for our April events. Bret will be speaking on the panel, “Trends in Global Privacy Enforcement and How to Allocate Scarce Compliance Resources,” and Tim will be speaking on the panel, “Navigating ePrivacy Requirements: New Ways to Tackle Consent, Cookies and Other Marketing Challenges.”

erwin
JUNE 11, 2020
Educators can provide a more valuable learning experience and environment for students. With the use of data intelligence tools, educational institutes can provide teachers with a more holistic view of a student’s academic performance. Apply real-time data in marketing strategies. Enhance logistical and operational planning.

HL Chronicle of Data Protection
MAY 31, 2019
Please join us for our June events. Bret Cohen and Stephanie Gold are presenting at the annual conference of the National Association of College and University Attorneys on the panel, “Focus on GDPR and Other Privacy Laws: How to Develop and Implement a Practical Approach to Compliance.” Privacy Breakfast. Location : Denver, Colorado.
Security Affairs
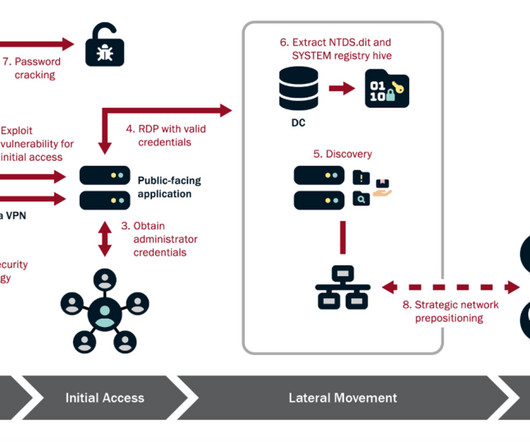
FEBRUARY 8, 2024
In the most recent campaign, the group targeted organizations in the communications, manufacturing, utility, transportation, construction, maritime, government, information technology, and education sectors. The APT group is using almost exclusively living-off-the-land techniques and hands-on-keyboard activity to evade detection.

The Last Watchdog
APRIL 13, 2022
Educate your employees on threats and risks such as phishing and malware. Enforce strong passwords and implement multi-factor authentication (MFA) — by educating users about using a unique password for each account and enforcing higher security for privileged accounts (administrators, root).

Adam Levin
AUGUST 26, 2020
Online classes for some 25,000 students in Rialto, California were cancelled following a malware attack and still remain offline as of this writing while school administrators are left to figure out how to collect and inspect several thousand laptops. . Competing services such as Skype and Google Meet offer free versions.

ForAllSecure
APRIL 26, 2023
” And, “Nearly half (48.8%) of C-suite and other executives expect the number and size of cyber events targeting their organizations’ accounting and financial data to increase in the year ahead.” According to a Deloitte Center for Controllership poll , “During the past 12 months, 34.5%

Security Affairs
NOVEMBER 29, 2022
In today’s technological world, educating people about cybersecurity awareness is an absolute necessity. It is important when developing and implementing these programs to be aware of what methods of education work best. While cybersecurity awareness training can take many forms, most training programs are computer-based.
eSecurity Planet
MARCH 15, 2024
Vulnerability assessment: HackerGPT makes it easier to analyze vulnerabilities by offering instructions on how to discover, prioritize, and mitigate security flaws. HackerGPT entails understanding how to bypass lock screens or exploit software defects for ethical motives. Its proper usage could result in a safer digital environment.

IT Governance
JANUARY 24, 2022
It’s why, for the past fifteen years, 28 January has marked Data Privacy Day – an international event raises awareness about online privacy and educates people on the ways they can protect their personal information. That’s why now is an ideal time to educate your children on the importance of data privacy.

Adam Levin
JUNE 4, 2021
You would think that ExaGrid, a backup appliance and anti-ransomware service might know how to avoid ransomware, but it was hit. . Practice the 3Ms: Minimize your risk of exposure: Don’t take unnecessary risks and invest in cyber defenses and education. The post Anti-Ransomware Company Exagrid Pays $2.6

Preservica
MARCH 10, 2022
We’ll be digging into the differences in a lot more detail in our upcoming 3-part virtual education series run in conjunction with Henry Stewart Events. In our 3-part virtual education series we’ll be looking in more depth at: How to ensure the long-term authenticity, integrity and reuse of digital assets.

The Last Watchdog
OCTOBER 5, 2023
The grants are part of the state’s SOC/Range Initiative, a program managed by MassTech’s MassCyberCenter that aims to help build a diverse generation of cybersecurity professionals through education, training, and workforce development. Preparation, communication, and active monitoring are key to defending against online attacks.” “The

Info Source
DECEMBER 10, 2018
Already well known in the content services industry for their annual DocuWorld Partner Conferences, DocuWare’s User Conference differs in that the focus is on educational enrichment and support for customers, not partners. Fujitsu, J&H, Inc., Kyocera Document Solutions America, Inc.,

KnowBe4
OCTOBER 13, 2023
Doing simulated phishing tests is the best way to educate your workforce about various social engineering threats. It is the best type of security awareness education, far more effective than regular training content alone. Bad actors intentionally pick and use news events with two highly charged sides.

eDiscovery Daily
MAY 7, 2019
Common Searching Mistakes and How to Avoid Them. As always, I’ll be presenting the webcast, along with Tom O’Connor, whose white paper regarding production challenges and how to address them was published last month on the blog. Avoiding the Redaction “Epic Fail” Understanding Load Files and Common Issues with Them.
CILIP
AUGUST 6, 2020
Science, technology, engineering, and mathematics (STEM) learning is a key part of conversations about education, policy, the economy, and our future. The majority (95%) of research participants have offered STEM events, and over half of respondents (52%) offer STEM frequently. STEM-event-in-a-box? s School of GeoSciences.

Rocket Software
JANUARY 29, 2021
The number of women participating in tech events has increased year over year, highlighting the importance of a more inclusive culture. In 2020, there was even greater participation in conferences, summits and seminars, including many events dedicated exclusively to women in tech. . There’s always a new technology making waves.

eSecurity Planet
SEPTEMBER 23, 2022
Our analysis will then need to consider what it will take to prepare to meet that request and how to communicate it clearly, without technical jargon, to our executives, to the board, and possibly to a judge and jury. In the event of a breach, the last thing the tech team will want to do is figure out how to make a report.

erwin
OCTOBER 17, 2022
Whether you’re new to erwin ® by Quest ® , or you’re a loyal user of our industry-leading solutions, you’ll benefit from learning how to maximize the business value of your data. You don’t even have to attend the live event to catch all the presentations. Because we truly hope you’ll join us for this special virtual event.

The Last Watchdog
OCTOBER 27, 2023
“That is why we have taken a multi-pronged approach that educates students about the opportunities that exist in a cybersecurity career, providing the critical training on cutting-edge tools, and the mentorship they need to succeed in a career.

IBM Big Data Hub
APRIL 15, 2024
To understand human behavior and how to change it, there are a few factors we must assess and measure, supported by the COM-B Behavior Change Wheel. While security awareness training remains vital and should not be overlooked, we must diversify our educational methods to foster a more positive culture.

Collibra
MAY 28, 2021
In the Birds of a Feather Roundtable, customers and prospects alike will come together to discuss adoption and scaling, how to build a data literate culture, the importance of data quality, and how to measure success and calculate the ROI on your data intelligence investment. And more! .
Security Affairs
OCTOBER 31, 2022
Italy was also marginally affected by the attack and the case was dealt with by the Computer Crime Operations Centre of the Postal Police (CNAIPIC ) [link] , which promptly issued an alert [link] on the very day of the event, recommending some useful actions also to prevent further possible propagation. Twitter @Slvlombardo.

eSecurity Planet
JUNE 16, 2022
Also read: How to Recover From a Ransomware Attack Best Ransomware Removal Tools Best Ransomware Removal and Recovery Services Best Backup Solutions for Ransomware Protection. Security information and event management (SIEM). Educating and training employees is a must-do in modern endpoint security. Mobile attacks.

DLA Piper Privacy Matters
NOVEMBER 29, 2021
Among the organizations that have designated a DPO, the most represented sectors are, unsurprisingly, the public administration, education and health sectors. The DPO may assist the organization representative in the event of a dawn raid to respond to the CNIL’s questions on the basis of his/her expertise.
IT Governance
OCTOBER 23, 2023
In addition, Leon has won hackathon events in the UK and internationally, and is accredited for multiple bug bounties. Specifically, companies are increasingly asking me about how to secure their data and infrastructure while continuing to be able to work remotely. He’s also been featured in various articles relating to cyber security.

eDiscovery Daily
SEPTEMBER 25, 2018
If you want to know how to leverage IG best practices to prepare for litigation before it happens, this is the webcast for you! The post Today is the Day to Learn How to Prepare for Litigation Before it Happens: eDiscovery Webcasts appeared first on CloudNine. To register for it, click here. So, what do you think?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content