Jamf Event: Education recap
Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.

Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.

IBM Big Data Hub
NOVEMBER 10, 2023
This blog will focus on the integration of IBM Cloud Code Engine and IBM Cloud Event Notifications along with IBM Cloud Secrets Manager to build a robust use case that will automate your certificate renewal process for applications in your code engine project. What is IBM Cloud Event Notifications? What is IBM Cloud Secrets Manager?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IBM Big Data Hub
JUNE 21, 2023
IBM Cloud Event Notifications is a service that can filter and route events received from other IBM Cloud services or custom applications to communication channels like email, SMS, push notifications, webhook, Slack, Microsoft® Teams, ServiceNow, IBM Cloud Code Engine and IBM Cloud Object Storage.

Thales Cloud Protection & Licensing
OCTOBER 5, 2022
Global October Cybersecurity Events: Where You Can Find Thales. The summer is now over, and October is a month full of cybersecurity events for Thales around the world. Below are just some of the events Thales will be at over the next few weeks. Les Assises turns 22 this year, and the event motto is "In 2022, We Speed Up!"

Speaker: Steve Pappas, Chief Strategist, Startup and Early Stage Growth Advisor, Keynote Speaker, CX Podcaster
Don't miss this exclusive event! Register today and receive FREE GIFTS from Steve after the webinar! 🗓 Thursday, January 11th, 2024 at 9:30am PST, 12:30pm EST, 5:30pm GMT

IBM Big Data Hub
JANUARY 8, 2024
In modern enterprises, where operations leave a massive digital footprint, business events allow companies to become more adaptable and able to recognize and respond to opportunities or threats as they occur. Teams want more visibility and access to events so they can reuse and innovate on the work of others.
eSecurity Planet
MAY 10, 2022
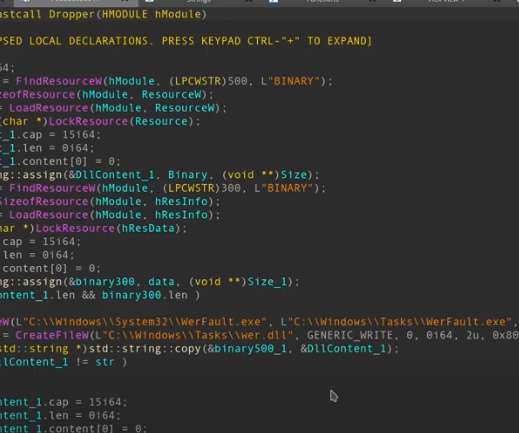
Hackers have found a way to infect Windows Event Logs with fileless malware , security researchers have found. During a “very targeted” campaign, hackers used Windows Event Logs to inject shellcode payloads and operate stealthily. How the Attackers Injected Code in Windows Logs. How to Protect Against Event Log Attacks.

Speaker: Dave Seaton, CEO of Seaton CX
You'll walk away with a deep understanding of: What a customer journey map is, and why it's important for success 🎯 The 5 key elements that must be on every map 🔑 How to create a customer journey map that truly drives change 📈 You won't want to miss this event! Register today to save your seat!

Speaker: Keith Kmett, Principal CX Advisor at Medallia
🔑 Connection to Customer Journey Maps: How to effectively integrate customer journey mapping into the CX orchestration process. You will gain insights into how to use journey maps to identify pain points, opportunities, and touchpoints where orchestration can make the most impact. Register today to save your seat!
Let's personalize your content