Top 5 Application Security Tools & Software for 2023
eSecurity Planet
MAY 19, 2023
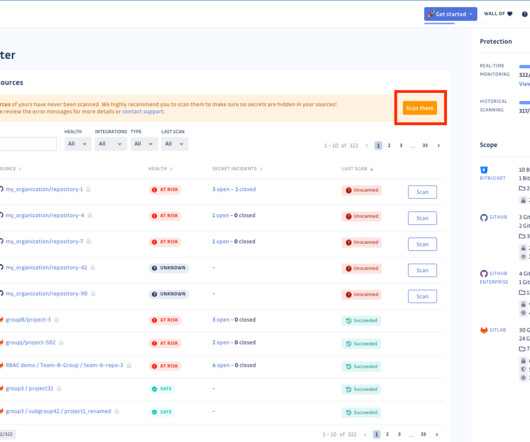
Application security tools and software solutions are designed to identify and mitigate vulnerabilities and threats in software applications. These tools play a vital role in ensuring the security, integrity, and confidentiality of sensitive information, such as personal data and financial records.




























Let's personalize your content