Updates to Format Guidance Bulletin
National Archives Records Express
MARCH 16, 2023
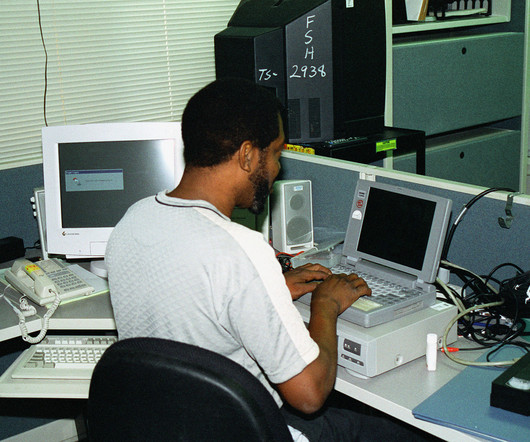
Department of the Army civilian uses a laptop computer to check out a video projector (Not shown) for Visual Information (VI) Presentation Services at Fort Sam Houston, San Antonio, Texas.













































Let's personalize your content