Challenges of User Authentication: What You Need to Know
Security Affairs
SEPTEMBER 7, 2022
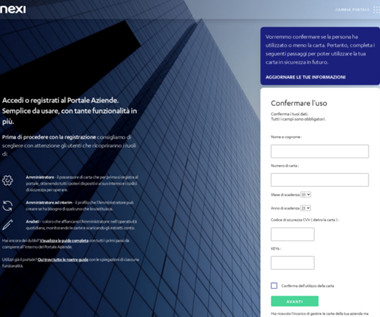
In the digital age, authentication is paramount to a strong security strategy. Which are the challenges of user authentication? In the digital age, authentication is paramount to a strong security strategy. User authentication seems easy, but there are inherent challenges to be aware of. User Authentication.











































Let's personalize your content