GUEST ESSAY: Everything you should know about the cybersecurity vulnerabilities of AI chatbots
The Last Watchdog
FEBRUARY 20, 2024
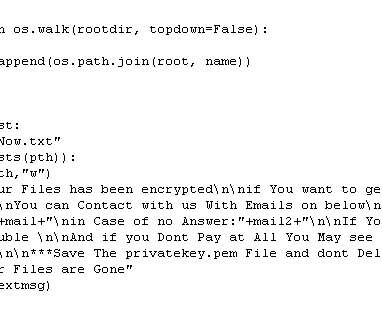
Examples of AI chatbot platforms include: •Dialogflow: Developed by Google, Dialogflow is renowned for its comprehension capabilities. Authentication and authorization vulnerabilities: Weak authentication methods and compromised access tokens can provide unauthorized access. Using MFA can prevent 99.9% of cyber security attacks.












































Let's personalize your content