How process mining improves IT service management to save your business time and money
IBM Big Data Hub
MAY 17, 2023
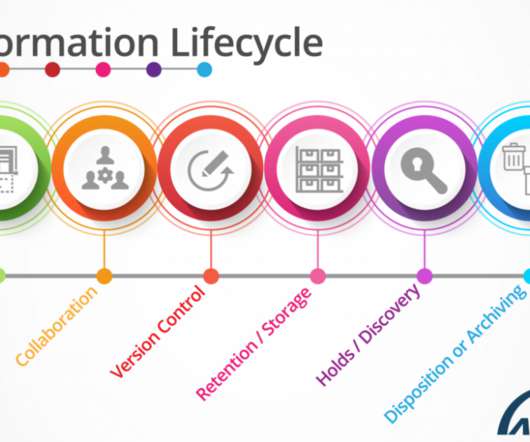
For example, if a user’s email is down, they submit a ticket to IT. Auto-discovery tools like process mining — a tool gaining popularity with organizations — does just that. Continuous process optimization and technological breakthroughs in process mining are now competitive differentiators.












































Let's personalize your content