Jamf Event: Education recap
Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Jamf
APRIL 9, 2024
The 2024 Jamf Event showed how to transform learning for students, teachers and parents; better protect students; and maintain seamless, secure access.

IBM Big Data Hub
FEBRUARY 12, 2024
Recognizing the need to harness real-time data, businesses are increasingly turning to event-driven architecture (EDA) as a strategic approach to stay ahead of the curve. At the forefront of this event-driven revolution is Apache Kafka, the widely recognized and dominant open-source technology for event streaming.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IBM Big Data Hub
NOVEMBER 29, 2023
By leveraging AI for real-time event processing, businesses can connect the dots between disparate events to detect and respond to new trends, threats and opportunities. AI and event processing: a two-way street An event-driven architecture is essential for accelerating the speed of business.

IBM Big Data Hub
SEPTEMBER 29, 2023
” [1] Real-time intelligence helps improve responsiveness To accelerate the speed of business, organizations should acquire the ability to access, interpret and act on real-time information about unique situations arising across the entire organization. This stream provides a persistent, real-time log of all orders received.

IBM Big Data Hub
JANUARY 8, 2024
In modern enterprises, where operations leave a massive digital footprint, business events allow companies to become more adaptable and able to recognize and respond to opportunities or threats as they occur. Teams want more visibility and access to events so they can reuse and innovate on the work of others.
Thales Cloud Protection & Licensing
SEPTEMBER 27, 2023
Around the World with Thales: Our Upcoming Events madhav Thu, 09/28/2023 - 05:01 The summer is long gone, and we are all back to work. However, there will be plenty of opportunity for us all to catch up as the Fall season is bustling with cybersecurity events worldwide. Our event booth number is H25-C70.

IBM Big Data Hub
APRIL 2, 2024
A messaging queue technology is essential for businesses to stay afloat, but building out event-driven architecture fueled by messaging might just be your x-factor. The core of building this real-time responsiveness lies in messaging, but its value can be expanded through event-driven architectures.

IT Governance
APRIL 24, 2024
Previously , I had the pleasure of sitting down with Sophie Sayer, our Channel Sales Director, to talk about the IT Governance partner programme and partner event on 9 April 2024. When I asked her how the event went, she said: The Channel Partner Event and Awards 2024 in Ely was an absolute triumph!

Thales Cloud Protection & Licensing
OCTOBER 5, 2022
Global October Cybersecurity Events: Where You Can Find Thales. The summer is now over, and October is a month full of cybersecurity events for Thales around the world. Below are just some of the events Thales will be at over the next few weeks. Les Assises turns 22 this year, and the event motto is "In 2022, We Speed Up!"

OpenText Information Management
NOVEMBER 29, 2023
How individuals engage with businesses, their evolving expectations, their demand for quicker responses, and recent global events, such as the COVID-19 pandemic, have compelled organizations to re-evaluate how they serve their customers.

Security Affairs
NOVEMBER 30, 2023
Researchers at AppOms discovered a vulnerability in Zoom Room as part of the HackerOne live hacking event H1-4420. The experts discovered the vulnerability in June 2023, they warned that an attacker can take over a Zoom Room’s service account and gain access to the victim’s organization’s tenant. ” concludes the report.

The Last Watchdog
JANUARY 6, 2022
They also enrich documents with metadata and place them in crypto-containers, access to which is only granted by permission. In addition, in the event of a leak, the watermark will not help to determine who leaked the document if an attacker cleverly cleans up the document, deletes it, or hides it. Demyanchuk. Identifying leakage.

HID Global
MAY 1, 2023
The Security Event 2023 discussed and displayed the latest solutions for keeping organizations safe as well as predicting the future of physical access control.

eSecurity Planet
AUGUST 22, 2023
Remote access security is critical for protecting increasingly distributed work environments, ensuring that only authorized users can access your valuable information regardless of their location. We’ll cover a range of best practices for remote access security, from the simple and the practical to the more advanced.

Data Breach Today
FEBRUARY 14, 2024
Attackers Accessed Details of State Visits to UK, France in Private Email Account The South Korean President's Office told local media Tuesday that suspected North Korean hackers had targeted the private email account of an official in November ahead of the president's state visits to the U.K. and France.
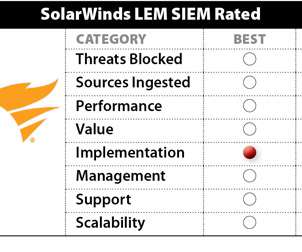
eSecurity Planet
FEBRUARY 6, 2023
SolarWinds lacks the full security suite presence of some competitors, but is well-integrated across a variety of bonus IT operation capabilities such as threat intelligence platform capabilities, privileged access management, USB security, and botnet detection. SolarWinds Security Event Manager (SEM) 2022.4 Throughput: Good.

Schneier on Security
JULY 15, 2022
Currently, the police can only request historical footage from private cameras related to specific times and locations, rather than blanket monitoring.

AIIM
NOVEMBER 7, 2023
This new event concept highlighted a local chapter and community while creating greater accessibility to AIIM's leadership and strategy. This terrific event was well attended and featured some great education. Here are my top takeaways from the event.

AIIM
JULY 22, 2019
That’s what we’ll be discussing when I host AIIM’s next virtual event on Thursday, July 25th, from 1pm-3pm. We’ll learn how IIM addresses a critical business objective: how do we give users access to the information they need, when and where they need it, and in the best format for performing a particular business application or function?

Security Affairs
APRIL 14, 2022
Threat actors are actively exploiting a critical vulnerability in VMware Workspace ONE Access and Identity Manager recently patched by the vendor. Threat actors are actively exploiting a critical flaw, tracked as CVE-2022-22954 , in VMware Workspace ONE Access and Identity Manager recently patched by the vendor. Pierluigi Paganini.

ForAllSecure
MAY 4, 2023
Upcoming Events We have two upcoming events planned for May 2023: Webinar: How to Uncover and Address Vulnerabilities in Open-Source Libraries GlueCon Read on to learn more about May’s events. While they provide access to pre-built components and tools, they can also introduce security vulnerabilities into your code.

Thales Cloud Protection & Licensing
NOVEMBER 20, 2022
How to Secure Access for your Seasonal Workers. These temporary employees will require immediate access to mobile catalogues, ordering systems, loyalty programs, and even point-of-sales (POS) systems. Access management risks of seasonal workers. The importance of effective access management. Mon, 11/21/2022 - 05:36.

eSecurity Planet
MARCH 14, 2021
Network Access Control (NAC) helps enterprises implement policies for controlling devices and user access to their networks. NAC can set policies for resource, role, device and location-based access and enforce security compliance with security and patch management policies, among other controls.

Security Affairs
OCTOBER 5, 2021
Syniverse service provider discloses a security breach, threat actors have had access to its databases since 2016 and gained some customers’ credentials. The company is a privileged target for threat actors that could hit the firm to access their customers’ information. ” states Motherboard.

Security Affairs
SEPTEMBER 23, 2020
E-commerce platform provider Shopify revealed that two members of its support staff accessed customer information without authorization. E-commerce platform provider Shopify on Tuesday confirmed that two employees of its support staff were accessing customer information without authorization. products and services purchased).

Data Matters
DECEMBER 2, 2019
On 4 November 2019, the European Data Protection Board (EDPB), the EU-wide data supervisory authority, held a stakeholders’ event on data subject rights under the GDPR. The post EDPB Stakeholder Event Highlights Continued Confusion over Data Subject Rights Compliance under the GDPR appeared first on Data Matters Privacy Blog.

Thales Cloud Protection & Licensing
JUNE 6, 2023
Modern Identity and Access Security - Keeping the Good Guys In and the Bad Guys Out madhav Tue, 06/06/2023 - 07:27 Regarding identity and access, it's becoming harder and harder, if not impossible, to distinguish the "good guys" from the "bad guys." Access security and authentication play an important role.

Security Affairs
NOVEMBER 27, 2018
Hacker compromised third-party NodeJS module “Event-Stream” introducing a malicious code aimed at stealing funds in Bitcoin wallet apps. The Event-Stream library is a very popular NodeJS module used to allow developers the management of data streams, it has nearly 2 million downloads a week. ” wrote Tarr.

Schneier on Security
MARCH 21, 2019
The Daily Beast is reporting that First Look Media -- home of The Intercept and Glenn Greenwald -- is shutting down access to the Snowden archives. The Intercept has given full access to multiple media orgs, reporters & researchers. Eventually it'll all become public, but not before it is 100% history and 0% current events.

Archives Blogs
DECEMBER 6, 2019
The Innovation Hub accomplishes an important part of NARA’s mission to make access happen through digitization, and also serves as an important event space to bring together both internal and external stakeholders for collaborative activities and cooperative learning. Photo courtesy of @wshs_applied_history.

DLA Piper Privacy Matters
JANUARY 15, 2021
Data Subject Access Requests – no unqualified right to documents. Section 13 DPA 98 permits individuals to seek compensation for damages and distress from a Data Controller in the event that the Data Controller is found to have breached any requirements of that legislation.

AIIM
APRIL 24, 2019
Make your valuable information more accessible, automated, and intelligent. This event is supported by Box, who will also be on hand to share a number of real-world use cases of how companies of different sizes and in a variety of industries are embracing the cloud to drive real business value.

KnowBe4
JANUARY 11, 2024
In a surprising turn of events for Formula 1 enthusiasts, the Haas F1 Team is grappling with the departure of its widely-respected Team Principal, Guenther Steiner. Let's dive into the implications of Guenther Steiner's departure and more information on a new template that our KnowBe4 customers can access in the ModStore now!

The Last Watchdog
FEBRUARY 5, 2024
The user interface is intuitive, making it accessible for users with varying levels of technical expertise. Robust access control. Implement strong password policies and multi-factor authentication to prevent unauthorized access. Comprehensive monitoring. Backup strategies.

HL Chronicle of Data Protection
SEPTEMBER 30, 2019
Please join us for our October Events. 2019 Privacy and Access Law Symposium. at The Canadian Bar Association Access to Information and Privacy Law Symposium. October 15. Privacy + Security Forum. Location : Washington, D.C. Location : Washington, D.C. October 18. Location : Ottawa, Ontario, Canada.

Security Affairs
APRIL 2, 2019
to 2.4.38, with MPM event, worker or prefork, code executing in less-privileged child processes or threads (including scripts executed by an in-process scripting interpreter) could execute arbitrary code with the privileges of the parent process (usually root) by manipulating the scoreboard. . “In Apache HTTP Server 2.4 release 2.4.38

OpenText Information Management
MAY 3, 2024
Re-ignite the spark: In-person events are back, for good Oh, how we love the buzz of in-person events! Ready to make your in-person events the talk of the town? Studies by Eventbrite show that events boil down to one simple thing: connection. AI, the Event Planning Wizard: As always, Forrester is on to something.

eSecurity Planet
FEBRUARY 2, 2024
Rapid7’s Zero Day Initiative hosts an event called Pwn2Own, and at the 2023 event, computer security firm Synactiv hacked a Tesla computer within two minutes. This year, electric cars were a major focal point of the 2024 event, called Pwn2Own Automotive.

IBM Big Data Hub
OCTOBER 13, 2023
This creates a domino effect: if your product teams are unable to access this pricing information in real-time, marketing strategy teams might then struggle to provide up-to-date messaging to potential customers. If you had access to real-time pricing data, you could receive immediate notification of drops in prices and take earlier action.

Security Affairs
NOVEMBER 3, 2023
Threat actors who breached the Okta customer support system also gained access to files belonging to 134 customers. Threat actors who breached the Okta customer support system in October gained access to files belonging to 134 customers, the company revealed. ” reads the post published by the company.

Info Source
JULY 28, 2022
This event will encourage scanner manufacturers, Independent Software Vendors as well businesses evolve their Capture strategy with driverless web and mobile document scanning applications by eliminating the need for legacy USB scanner connectivity. This event is supported by Silver Sponsor Visioneer, Inc., Atalasoft, Microtek, Inc.,

Info Source
JULY 28, 2022
This event will encourage scanner manufacturers, Independent Software Vendors as well businesses evolve their Capture strategy with driverless web and mobile document scanning applications by eliminating the need for legacy USB scanner connectivity. This event is supported by Silver Sponsor Visioneer, Inc., Atalasoft, Microtek, Inc.,

The Last Watchdog
SEPTEMBER 25, 2023
In the era of cloud computing, where programs and your information can be accessed anywhere, your business needs to keep its software up-to-date and back up critical systems. These back-ups can also be used to form a disaster recovery plan in the event of a natural disaster. Set access privileges and internal controls.
Security Affairs
NOVEMBER 15, 2023
VPNs, RDPs) to gain initial access to the target network and maintain persistence. The group relied on compromised credentials to authenticate to internal VPN access points. AnyDesk A common software that can be maliciously used by threat actors to obtain remote access and maintain persistence [ T1219 ].
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content