Calendar Meeting Links Used to Spread Mac Malware
Krebs on Security
FEBRUARY 28, 2024
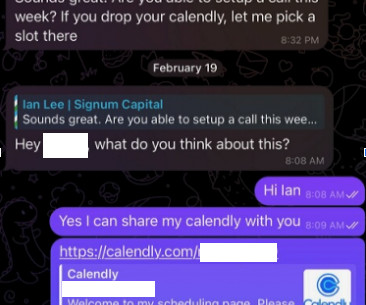
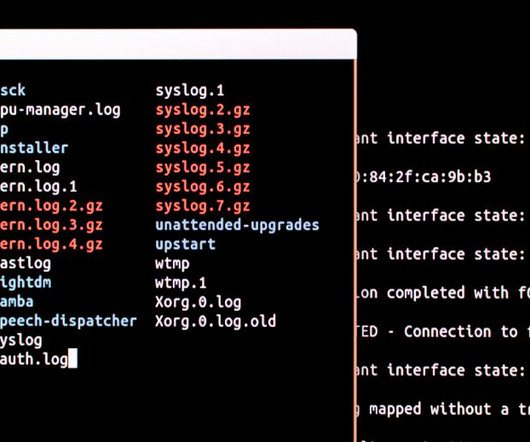
Malicious hackers are targeting people in the cryptocurrency space in attacks that start with a link added to the target’s calendar at Calendly , a popular application for scheduling appointments and meetings. It didn’t dawn on Doug until days later that the missed meeting with Mr. Lee might have been a malware attack.











































Let's personalize your content