New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
Security Affairs
AUGUST 28, 2023
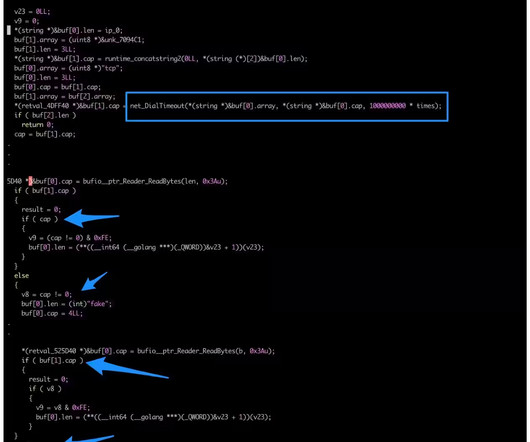
Researchers spotted an updated version of the KmsdBot botnet that is now targeting Internet of Things (IoT) devices. The Akamai Security Intelligence Response Team (SIRT) discovered a new version of the KmsdBot botnet that employed an updated Kmsdx binary targeting Internet of Things (IoT) devices.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
AUGUST 9, 2021
A malicious advertising campaign originating out of Eastern Europe and operating since at least mid-June is targeting Internet of Things (IoT) devices connected to home networks, according to executives with GeoEdge, which offers ad security and quality solutions to online and mobile advertisers. Malvertising is Evolving.

Security Affairs
DECEMBER 21, 2018
2018 was the year of the Internet of Things (IoT), massive attacks and various botnets hit smart devices, These are 5 IoT Security Predictions for 2019. IoT Attacks in 2018. Do the increased attacks mean the industry is becoming accustomed to IoT cyber attacks? Insights from VDOO’s leadership.

Ascent Innovations
MAY 17, 2018
The new cyber intelligence report expects the monetary benefits will allure the use of crypto-mining malware and cryptocurrencies by cyber attackers this year. Healthcare IoT. The healthcare IoT is problematic due to the increase in networked medical devices. State Attackers Moving from Stealing Data to Social Meddling.

eSecurity Planet
JUNE 16, 2022
These new attacks affect everything from private citizens and businesses to government systems; healthcare organizations; public services; and food, water, and fuel supply chains. From laptops to smartphones, virtual desktops, or IoT, an organization may have thousands of active endpoints at any given time. Ransomware. Other methods.

IT Governance
APRIL 16, 2018
Cryptojacking is when cryptocurrency miners are delivered through malware, using a computer’s processing power to illicitly mine cryptocurrency. With the number of Internet-connected devices increasing, more attackers will use the Internet of Things (IoT) to commit cyber crimes. Cryptojacking. Gartner has predicted that 11.2
Let's personalize your content