New Report on IoT Security
Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
SEPTEMBER 28, 2022
The Atlantic Council has published a report on securing the Internet of Things: “Security in the Billions: Toward a Multinational Strategy to Better Secure the IoT Ecosystem.”

eSecurity Planet
JANUARY 22, 2021
billion Internet of Things (IoT) devices. As more information about IoT device vulnerabilities is published, the pressure on industry and government authorities to enhance security standards might be reaching a tipping point. government, standards will not apply to the IoT market at-large. By 2025, we expect 21.5
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
IBM Big Data Hub
FEBRUARY 29, 2024
Here, we will look at examples and applications of renewable energy across a variety of industries, its impact on energy systems and the energy technologies that will drive its use in the future. By integrating smart grids and Internet of Things (IoT) devices, businesses can better manage their energy use. trillion in 2023.

Security Affairs
SEPTEMBER 21, 2020
House of Representatives passed the IoT Cybersecurity Improvement Act, a bill that aims at improving the security of IoT devices. House of Representatives last week passed the IoT Cybersecurity Improvement Act, a bill designed to improve the security of IoT devices. Mark Warner (D-Va.) Pierluigi Paganini.

Schneier on Security
JUNE 25, 2020
New research: " Best Practices for IoT Security: What Does That Even Mean? " We consider categories of best practices, and how they apply over the lifecycle of IoT devices. by Christopher Bellman and Paul C. Back in 2017, I catalogued nineteen security and privacy guideline documents for the Internet of Things.

Security Affairs
OCTOBER 13, 2020
The number of sensors and smart devices connected to the internet is exponentially rising, which are the 5 Major Vulnerabilities for IoT devices. If you take a look at the global market for IoT, you can easily spot the trend. IoT devices are exposed to cybersecurity vulnerabilities. IoT is a complicated concept.

Thales Cloud Protection & Licensing
NOVEMBER 6, 2019
As most of us know, IoT devices are on the rise in enterprise networks. According to McKinsey & Company , the proportion of organizations that use IoT products has grown from 13 percent in 2014 to 25 percent today. The issue is that these tens of billions of new devices will likely amplify the inherent security risks of IoT.

Thales Cloud Protection & Licensing
JULY 15, 2021
Key Developments in IoT Security. Remember the early days of the emergence of Internet of Things (IoT) devices? Vulnerabilities have been discovered in many of these IoT devices. Ellen has extensive experience in cybersecurity, and specifically, the understanding of IoT risk. Thu, 07/15/2021 - 10:09.

Security Affairs
DECEMBER 21, 2018
2018 was the year of the Internet of Things (IoT), massive attacks and various botnets hit smart devices, These are 5 IoT Security Predictions for 2019. IoT Attacks in 2018. Do the increased attacks mean the industry is becoming accustomed to IoT cyber attacks? Insights from VDOO’s leadership.

Thales Cloud Protection & Licensing
SEPTEMBER 11, 2018
This aptly describes the Internet of Things (IoT), where many small things are coming together to shape what we all hope will deliver a great leap in the way we live and do business. According to Maciej Kranz, Cisco VP for strategic innovation, writing for IoTechExpo.com , “[In 2018] IoT security will become the No.

The Last Watchdog
MARCH 13, 2019
The drivers of IoT-centric commerce appear to be unstoppable. Count on the wide deployment of IoT systems to continue at an accelerated rate. There are already more IoT devices than human beings on the planet, according to tech industry research firm Gartner. This time the stakes are too high. Security-by-design lacking.

IBM Big Data Hub
MAY 31, 2023
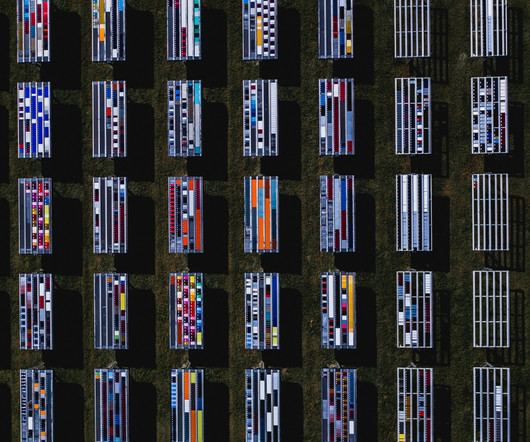
There are many overlapping business usage scenarios involving both the disciplines of the Internet of Things (IoT) and edge computing. This is especially true in manufacturing and industrial engineering. Robots on the manufacturing floor are programmed to be aware of and work with other robots. to connected products.

Data Matters
MARCH 7, 2022
If adopted in its current form, the new rules will impose far-reaching obligations on tech companies (such as manufacturers of connected products and cloud service providers) and give national authorities new enforcement powers to sanction infringements with fines of up to EUR 20 million or 4% of annual global revenue, whichever is higher.

IBM Big Data Hub
JULY 11, 2023
Over the years, the Internet of Things (IoT) has evolved into something much greater: the Economy of Things (EoT). The number of IoT connected devices are growing in practically every industry, and is even predicted to reach 29 billion worldwide by 2030. These IoT connected devices form a critical backbone of data for industry.

IBM Big Data Hub
FEBRUARY 7, 2024
Businesses, governments and individuals now see sustainability as a global imperative. As more companies set broad environmental, social and governance (ESG) goals, finding a way to track and accurately document progress is increasingly important.

Krebs on Security
OCTOBER 12, 2018
Tony Sager (TS): The federal government has been worrying about this kind of problem for decades. In the 70s and 80s, the government was more dominant in the technology industry and didn’t have this massive internationalization of the technology supply chain. BK: Right, the Trusted Foundry program I guess is a good example.

The Security Ledger
NOVEMBER 3, 2021
Related Stories Spotlight: When Ransomware Comes Calling Episode 226: The Cyber Consequences Of Our Throw Away Culture Spotlight: Automation Beckons as DevOps, IoT Drive PKI Explosion. In recent years, even “old economy” industrial and manufacturing firms like Ford, GM and John Deere got into the act. Click the icon below to listen.

eSecurity Planet
NOVEMBER 19, 2021
IoT security is where endpoint detection and response ( EDR ) and enterprise mobility management ( EMM ) meet the challenges of a rapidly expanding edge computing infrastructure. As the enterprise attack surface grows, IoT is yet another attack vector organizations aren’t fully prepared to defend.

IBM Big Data Hub
AUGUST 8, 2023
Examples of transportation systems include roadways, public transit systems, airports, train stations, bus stations, ferry terminals, pipelines and warehouses. This ambitious bill, largely managed by the US Department of Transportation, will distribute USD 1 trillion to fund construction, manufacturing initiatives and public works.

Data Protection Report
NOVEMBER 3, 2017
Now, a new Internet of Things (IoT) botnet, called IoT Reaper, or IoTroop, has been discovered by researchers and could present a threat that could dwarf the 2016 attacks and create a major disruption to internet activity around the world. Negotiating/Reviewing Contractual Liability.

HL Chronicle of Data Protection
JANUARY 18, 2019
Increasing numbers of initiatives, devices, and solutions related to the Internet of Things (IoT) are substantially impacting the development of cybersecurity and data privacy regulations throughout Asia. At the same time, it is clear that many Asian jurisdictions see IoT as a key driver for economic growth. Mark Parsons: Definitely.
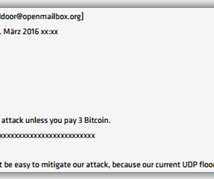
eSecurity Planet
NOVEMBER 11, 2021
Hackers targeted a wide range of organizations, such as banks, mail services, Bitcoin sites, VoIP providers, vaccination registration portals, information security media, gaming platforms, government sites, and even security agencies. For example, cybercriminals performed DDoS attacks on VoIP providers, affecting Britain, Canada, and the U.S.,

Thales Cloud Protection & Licensing
AUGUST 16, 2018
In the past, most strategies from the government have been fairly heavily focused on networking – connecting devices and ensuring access to certain parts of the world. And to do so, we must know, for example, that this vote was cast by this person at this location with the correct identity.

Thales Cloud Protection & Licensing
JUNE 6, 2018
Gartner defines digital risk management as “the integrated management of risks associated with digital business components, such as cloud, mobile, social, big data, third-party technology providers, OT and the IoT.” While the threat level has risen, IT, operational technology (OT) and Internet of Things (IoT) have continued to converge.

Thales Cloud Protection & Licensing
MAY 30, 2018
The DHS Cybersecurity Strategy is a well-thought-out framework with five pillars of cybersecurity goals to support critical infrastructure, government networks and non-government entities. We need to encourage manufacturers and suppliers to create “trusted” products that are secure and come from secure supply chains.

Schneier on Security
NOVEMBER 13, 2018
Due to ever-evolving technological advances, manufacturers are connecting consumer goods -- from toys to lightbulbs to major appliances -- to the internet at breakneck speeds. But it's just one of dozens of awful "security" measures commonly found in IoT devices. This is the Internet of Things, and it's a security nightmare.

ARMA International
SEPTEMBER 13, 2021
Gartner (2021) has two related definitions: Digital Transformation: “can refer to anything from IT modernization (for example, cloud computing), to digital optimization, to the invention of new digital business models.” DRM is used by publishers, manufacturers and IP owners for digital content and device monitoring” (Techopedia 2021).

IBM Big Data Hub
AUGUST 7, 2023
For instance, in response to sustainability trends, product manufacturers may need to prove the carbon footprint of their products to regulators and clients. Orion can serve as a robust repository for storing the carbon footprint data of all product components, provided by part manufacturers.

Reltio
JUNE 20, 2019
But that was my route into data management and going from there into MDM PIM and data governance. Product data looks very different depending on the product you are talking about and manufacturers see products very differently from the merchants. “On We will see scope-creep from IoT into data management – it will have a huge impact.

Data Matters
APRIL 18, 2018
The Framework was originally developed to focus on energy, banking, communications, and defense sectors, but has been adopted voluntarily by a much broader group of companies and government agencies. Significantly, version 1.1 NIST’s fact sheet on the updated version is available here: [link]. It can drive up costs and affect revenue.

Security Affairs
SEPTEMBER 30, 2019
After 2 years of waiting, MalwareMustDie returns with an excellent page of malware analysis of a new IoT malware: Linux/AirDropBot. The beginning of the story: another IoT malware in the wild? One of them, for example , is the C2 server. Coming to the core topic: IoT botnet threat and their ecosystem.

CGI
FEBRUARY 19, 2019
partners with Google to use their data for solar generation and cost saving simulations, and with German battery manufacturer SOLARWATT for energy storage. For example, Tennet and DSOs in the Netherlands are working together to develop market platforms for trading demand side flexibility.

Reltio
OCTOBER 20, 2019
But that was my route into data management and going from there into MDM PIM and data governance. Product data looks very different depending on the product you are talking about and manufacturers see products very differently from the merchants. “On We will see scope-creep from IoT into data management – it will have a huge impact.

eSecurity Planet
SEPTEMBER 1, 2021
Service providers and 5G-enabled device manufacturers both have critical roles to play in the success and sustainability of this wireless network rollout. Exposing the Internet of Things (IoT) Universe. IoT products are notoriously vulnerable appliances because the build prioritizes ease of use and connectivity.
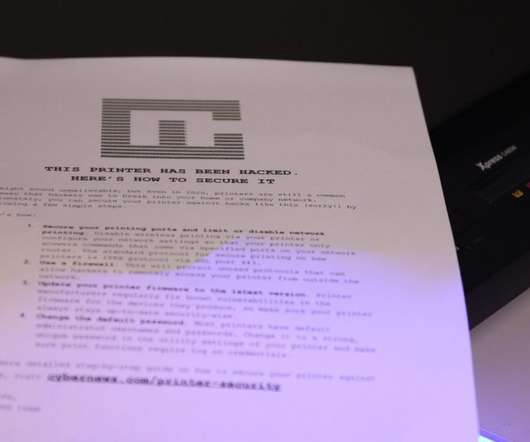
Security Affairs
AUGUST 27, 2020
To perform the experiment, we used Internet of Things (IoT) search engines to search for open devices that utilized common printer ports and protocols. To find out how many printers were on the menu for our experiment, we searched for IP addresses with open ports on specialized IoT search engines, such as Shodan and Censys.

Collibra
APRIL 3, 2019
Continued adoption of IoT technologies will pose both opportunities and challenges. Yet along that path there will be numerous obstacles to overcome – chiefly related to data privacy and governance. Any organisation engaged in IoT will be amassing datasets that have the potential to become extremely valuable.

IBM Big Data Hub
MAY 15, 2024
This situation will exacerbate data silos, increase costs and complicate the governance of AI and data workloads. Unified, governed data can also be put to use for various analytical, operational and decision-making purposes. This process is known as data integration, one of the key components to a strong data fabric.

eSecurity Planet
FEBRUARY 16, 2021
This article dives into the lexicon of malware, offering descriptions, protections, and examples of each. Examples of Adware Malware Attacks. While there are hundreds of adware versions, some of the most common examples include Fireball, Appearch, DollarRevenue, Gator, and DeskAd. Examples of Backdoor Malware Attacks.

Data Protection Report
JANUARY 13, 2020
For example, the initiative would potentially extend the 12-month “look-back” period so that a consumer could request data from more than 12 months prior to the request with respect to information collected on or after January 1, 2022. .* This version has some potential surprises for companies subject to CCPA and is worth monitoring.

Data Protection Report
JANUARY 13, 2020
For example, the initiative would potentially extend the 12-month “look-back” period so that a consumer could request data from more than 12 months prior to the request with respect to information collected on or after January 1, 2022. .* This version has some potential surprises for companies subject to CCPA and is worth monitoring.

Thales Cloud Protection & Licensing
JANUARY 24, 2024
Threats to cryptography are generally prevented by using common cybersecurity hygiene practices defined in clear and achievable governance. This type of threat poses interesting questions on the design of systems that have long life cycles – for example cars, transport infrastructure, core banking applications, and blockchain applications.

eSecurity Planet
APRIL 7, 2023
Customers for the privately-held customer include Fortune 100 organizations and government agencies. In 2000, Forescout entered the security market as an NAC provider and then expanded capabilities to encompass more security and asset control features. Agents Forescout Platform is an agentless solution. USMC ATO (Authority to Operate) U.S.

ForAllSecure
MARCH 8, 2023
I wrote two books, one on IoT Security and another with Kevin Mitnick, then jumped around a couple of different jobs. I’m Robert Vamosi, and in the episode I’m talking about diversity, equality, and inclusion in information security with one of the industries' most successful examples. So I learned.

ForAllSecure
APRIL 26, 2022
You're really looking at a government agency from some some country who's politically motivated and who can afford to put the money and the time into building a threat like this and who has the insider information from a uranium enrichment facility that would facilitate building a threat? Van Norman: Right right.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content