GUEST ESSAY: Best practices to shrink the ever-present risk of Exchange Server getting corrupted
The Last Watchdog
FEBRUARY 5, 2024
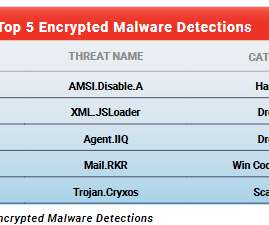
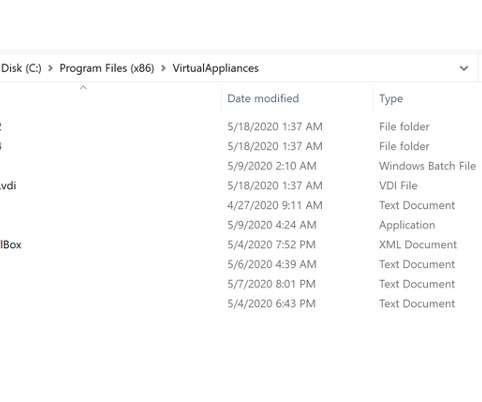
Encrypt sensitive data and maintain regular, secure backups to ensure data integrity and availability, even in the event of system failures or cyber attacks. •Comprehensive monitoring. Employ continuous monitoring for suspicious activities and have a well-defined incident response plan ready to address any security breaches.





































Let's personalize your content