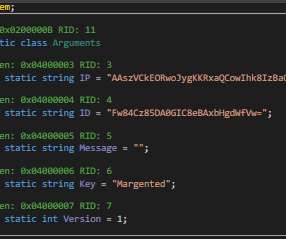
Hyundai Uses Example Keys for Encryption System
Schneier on Security
AUGUST 22, 2022
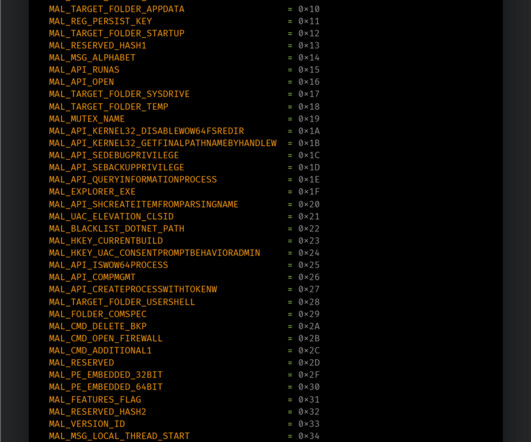
This is a dumb crypto mistake I had not previously encountered: A developer says it was possible to run their own software on the car infotainment hardware after discovering the vehicle’s manufacturer had secured its system using keys that were not only publicly known but had been lifted from programming examples. […].































Let's personalize your content