NEW TECH: DigiCert Document Signing Manager leverages PKI to advance electronic signatures
The Last Watchdog
JULY 21, 2021
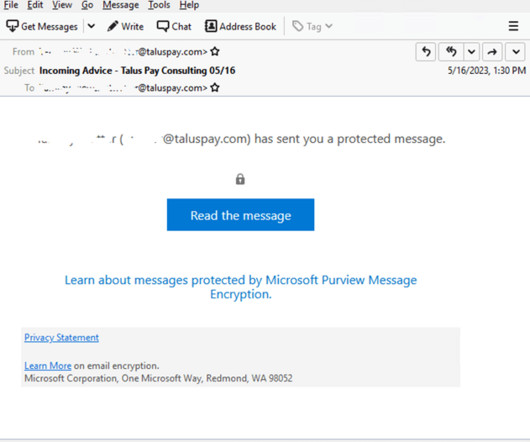
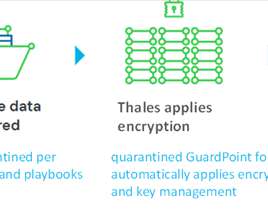
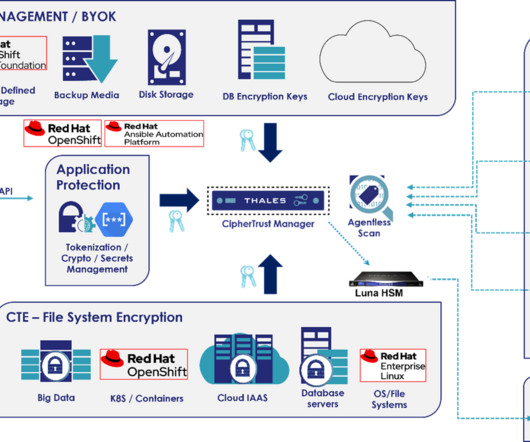
And this is why DigiCert recently introduced DigiCert® Document Signing Manager (DSM) – an advanced hosted service designed to increase the level of assurance of the identities of persons signing documents digitally. And PKI , of course, is the behind-the-scenes authentication and encryption framework on which the Internet is built.
































Let's personalize your content