Palo Alto's Biggest Bets Around AppSec, SecOps, SASE & Cloud
Data Breach Today
DECEMBER 15, 2022
Palo Alto Networks has committed to having best of breed features and functionality in each of the technology categories where it chooses to play.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 category technology
category technology 
Data Breach Today
DECEMBER 15, 2022
Palo Alto Networks has committed to having best of breed features and functionality in each of the technology categories where it chooses to play.

Dark Reading
NOVEMBER 13, 2017
A rundown of some of the hottest security product areas, and vendors helping to shape them.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Thales Cloud Protection & Licensing
NOVEMBER 1, 2023
Google Cloud Technology Partner of the Year Award Thales was selected as the Google Cloud Technology Partner of the Year in the Security – Data Protection category. With over 20 categories recognizing MSP and vendor achievements, the awards are among the most prestigious in the industry.

AIIM
NOVEMBER 19, 2020
In organizations, change can be grouped into two broad categories – transformational and transitional. Let’s take a look at both categories of organizational change to gain a better understanding. We’re not talking about small change with this category. What is Transformational Change? Real change requires a real plan.

Advertisement
Why do some embedded analytics projects succeed while others fail? We surveyed 500+ application teams embedding analytics to find out which analytics features actually move the needle. Read the 6th annual State of Embedded Analytics Report to discover new best practices. Brought to you by Logi Analytics.
Hunton Privacy
FEBRUARY 12, 2024
On February 8, 2024, the Federal Communications Commission declared that calls using AI- generated, cloned voices fall under the category of “artificial or prerecorded voice” within the Telephone Consumer Protection Act (“TCPA”) and therefore are generally prohibited without prior express consent, effective immediately.

The Last Watchdog
MAY 11, 2023
Related: The need for timely training At RSA Conference 2023 , I learned all about a new category of email security — referred to as integrated cloud email security ( ICES ) – that is helping companies more effectively keep email threats in check. These filters look for known bad attachments and links.

The Last Watchdog
JANUARY 31, 2024
The funding will be used for core research and development to build new AI technology and products to protect against generative AI threats, such as deepfake social engineering and autonomous fraud. About Reken: Reken is building a new category of AI products and platform to protect against generative AI threats.
IT Governance
DECEMBER 5, 2023
Data Breach Dashboard For a quick, one-page overview of this month’s findings, please use our Data Breach Dashboard: Note: From this month, zero-day vulnerabilities are excluded from the ‘unpatched or misconfigured’ category. This is part of the reason this category is lower than last month (24% vs 32%). Where ‘up to’, etc.
Hunton Privacy
AUGUST 29, 2023
In issuing the Draft Regulations, the CPPA Board makes clear that it has not yet started the formal rulemaking process for cybersecurity audits, risk assessments or automated decision-making technology, and that these Draft Regulations are intended to facilitate Board and public discussion and are subject to further changes.

Security Affairs
JULY 1, 2021
RRA could be used by organizations to determine their level of exposure to ransomware attacks against their information technology (IT), operational technology (OT), or industrial control system (ICS) assets. ” CISA says.

IBM Big Data Hub
FEBRUARY 2, 2024
Not an easy task when you need to celebrate the achievements and stories of more than 1,000 nominees across nearly 100 categories. Next they select an artist or award category to feature, the subject of the post, such as biographical information, GRAMMY achievements, or philanthropic causes, and any topics to exclude from the output.
Hunton Privacy
MARCH 16, 2023
The new content in this chapter relates to AI and inferences, affinity groups and special category data. For example, the updated guidance notes that it may be possible, using AI, to infer or guess details about a person, which may constitute special category data.

eSecurity Planet
DECEMBER 7, 2022
Despite all this, there is one tech category that has held up fairly well: Cybersecurity. Vaibhav Narayanam, who is the Director of Corporate Development & Venture Investments at ServiceNow, invests in a variety of technologies. One of the firm’s investments in this category is Immuta. Data Compliance and Protection.

Data Protection Report
AUGUST 29, 2022
On July 13, 2022, the Office of the Superintendent of Financial Institutions (OSFI) released its final Guideline B-13 (the Guideline), setting out technology and cyber risk management expectations for all federally regulated financial institutions (FRFIs), such as banks, insurance and trust companies. Read the full update here.

The Last Watchdog
JULY 13, 2023
London, July 13, 2023 — Beazley, the leading specialist insurer, today published its latest Risk & Resilience report: Spotlight on: Cyber & Technology Risks 2023. The economic impact of cybercrime on business across the globe continues to reach new levels, with the cost predicted to reach US$10.5
eSecurity Planet
SEPTEMBER 8, 2023
Technology reviews can be a temptingly easy way to gain insight into the often impenetrable world of enterprise cybersecurity products, but you need to know how to use them. To help, we’ll cover the pros, built-in biases, and suitability of each type of technology review and how to use each review type as a buyer.
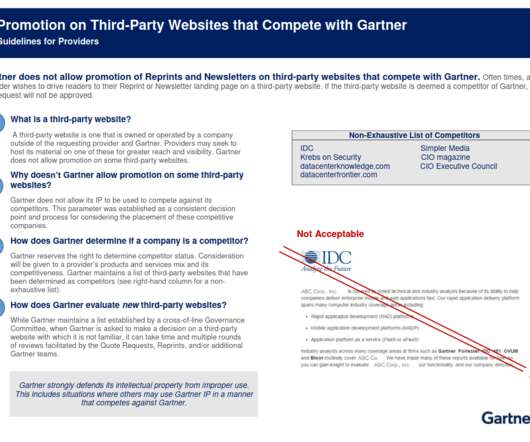
Krebs on Security
APRIL 20, 2021
NYSE:IT ] — a $4 billion technology goliath whose analyst reports can move markets and shape the IT industry. As the largest organization dedicated to the analysis of software, Gartner’s network of analysts are well connected to the technology and software industries.

The Last Watchdog
NOVEMBER 14, 2023
” Gupta, an accomplished technology executive, brings over 20 years of experience in driving growth and innovation for startups and public companies in the fields of cybersecurity, data analytics, and enterprise infrastructure software. “Conversations with customers have confirmed 1touch.io ” 1touch.io
Hunton Privacy
OCTOBER 5, 2023
The Guidance emphasizes that employers must comply with the data protection principles of the UK GDPR, regardless of the monitoring technology being used, and select the least intrusive means to achieve the purposes of their monitoring.

The Last Watchdog
JULY 30, 2018
The painful impact of cyber attacks on businesses is worsening despite advances in technology aimed at protecting enterprises from malicious network traffic, insider threats, malware, denial of service attacks and phishing campaigns. Over the past decade, cyber security solutions have evolved into specific categories of solutions.

IBM Big Data Hub
FEBRUARY 15, 2024
I’m a firm believer that exceptional brick-and-mortar retail, no matter the product category, stands on three essential pillars for success: Proud, well-trained, engaged team members with clear career paths A brand deeply rooted in strong cultural values A backbone of superior technology Missing any of these elements?

Hunton Privacy
APRIL 4, 2023
million to TikTok Information Technologies UK Limited and TikTok Inc (together, “TikTok”) for a number of breaches of UK data protection law, including failing to use children’s personal data lawfully. On April 4, 2023, the data protection regulator of the UK, the Information Commissioner’s Office (ICO), issued a fine of a £12.7
Hunton Privacy
MAY 18, 2023
On May 17, 2023, the European Data Protection Board (EDPB) adopted the final version of its Guidelines on facial recognition technologies in the area of law enforcement (the “Guidelines”).

Data Protection Report
OCTOBER 17, 2022
In July of this year, the Office of the Superintendent of Financial Institutions (OSFI) released the final version of its Guideline B-13 (the Guideline), setting out technology and cyber risk management expectations for all federally regulated financial institutions (FRFIs), such as banks, insurance and trust companies.

IBM Big Data Hub
SEPTEMBER 7, 2023
The results from the first global CEMM benchmark of 90 transmission and distribution utilities paint a telling picture of the role that technology can play in this critical transformation. According to the CEMM study, the most mature 25% of transmission and distribution utilities still only achieved the modest overall score of 2.2

The Last Watchdog
OCTOBER 4, 2023
LW: Your ‘continuous security protection lifecycle’ argument suggests we’re in an early phase of what: co-mingling; consolidating; integration of these three categories? But Omdia believes that a mix of preventative, reactive, and proactive tools are appropriate across all components of the digital landscape. Braunberg: Absolutely.

IT Governance
SEPTEMBER 15, 2022
There are two sub-categories of information security. The second sub-category of information security relates to the protection electronic information. The second sub-category of information security relates to the protection electronic information. This is cyber security. Examples of information security.

The Last Watchdog
JULY 26, 2023
The company has the vision, technology and expertise to capture a lion’s share of this new market category.” “Protect AI’s founders have built and managed the largest AI/ML businesses in the world for AWS and Oracle, and have assembled one of the most accomplished teams I’ve seen in a startup.
Hunton Privacy
MAY 26, 2022
As reported in the Hunton Employment & Labor Perspectives Blog : Assembly Bill 1651 , or the Workplace Technology Accountability Act, a new bill proposed by California Assembly Member Ash Kalra, would regulate employers and their vendors regarding the use of employee data.

IBM Big Data Hub
FEBRUARY 22, 2024
The IBM AI Ethics Board publication Foundation models: Opportunities, risks and mitigations addresses those concerns and explores the technology’s benefits, risks, guardrails, and mitigations. Known risks from prior or earlier forms of AI systems.

The Last Watchdog
JUNE 13, 2022
These pitches fall into two categories: pre-product companies and companies with working prototypes of their solutions. The recent swoon in public markets for technology stocks may lead one to predict that there will be a lull in funding of cybersecurity solutions, along with a downtick in valuations.
Security Affairs
JANUARY 19, 2024
Quantum has been discussed and theorized for years, and like the “sudden” rise of AI and generative technology that seemed to happen in early 2023, efficient and cost-effective use of quantum computing may also jump to a critical mass, and sooner than expected, despite its long voyage of research and development.
Hunton Privacy
MAY 13, 2021
As defined in the TDPA, a “smart access” building is one that uses keyless entry systems, including electronic or computerized technology ( e.g. , a key fob), RFID cards, mobile apps, biometric information or other digital technology to grant access to the building, common areas or individual dwelling units.

eDiscovery Law
DECEMBER 1, 2022
The K&L Gates e-Discovery Analysis & Technology (“e-DAT”) Group has spent the last few weeks adding additional content and making a number of revisions and updates to our ediscoverylaw.com website.
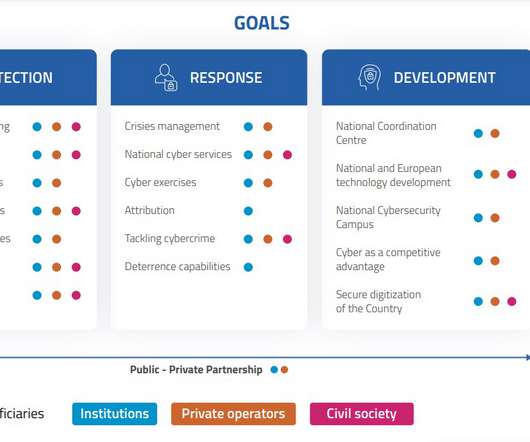
Security Affairs
MAY 26, 2022
“The ongoing evolution of technology that has shaped our current society keeps raising new risks as it continues to develop, along with most sophisticated attack techniques. Please vote for Security Affairs and Pierluigi Paganini in every category that includes them (e.g. A secure country is a more competitive country.

IT Governance
NOVEMBER 28, 2023
This week, we’re taking a slightly different approach with the ‘publicly disclosed data breaches and cyber attacks’ category, presenting the most interesting data points in a table format. The ‘enforcement’ and ‘other news’ categories remain unchanged. This should make it easier for you to quickly find the information you want.

Zapproved
JULY 23, 2020
There are two major categories of security features cloud vendors can offer to address threats. Technology and operations each contribute to data security.

Info Source
JULY 7, 2023
The new scanner is equipped with Ricoh’s Clear Image Capture (CIC) technology designed to produce higher quality images with limited color shift and distortion. Ricoh/PFU is the market leader in the Desktop Workgroup category and holds 37.8% touchscreen displays in the distributed scanner categories. as its predecessor.

ARMA International
JUNE 19, 2023
Records managers, compliance, finance, information technology, legal, and privacy departments are all concerned with the proper management of information. Information Technology : For IT systems to work effectively with electronic records they need rules. Software and IT products, however, often change on a much more frequent basis.

Rippleshot
JULY 25, 2019
Bank Director has announced the finalists for the 2019 Best of FinXTech Awards, which recognizes the efforts of the emerging financial technology solutions within their FinXTech Connect platform that best help financial institutions grow revenue, create efficiencies or reduce risk.

IBM Big Data Hub
APRIL 10, 2024
Organizations must keep up with the technology of today so they can innovate and satisfy the ever-changing needs of the customers. Many organizations have disappeared from the technology map because of failing to adapt and adopt innovation quickly. Modernization can substantially address sustainability goals.

eSecurity Planet
JUNE 14, 2022
But it is also a large category and the latest funding will certainly help drive the growth. Web3 is one of the buzziest categories in technology today. He is still an assistant professor of Computer Science at Columbia University and is the developer of core Web3 security technology like CertiKOS and SeKVM.

Lenny Zeltser
MAY 10, 2023
Helen Patton helps CISOs understand how they should spend their time by discussing seven circles of security : Technology, data, business, etc. You know how to bring in the right technologies to enable your vision for the program. You enjoy revising processes and adjusting how technology supports them to match the organization's needs.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content