Will cryptocurrency mining soon saturate AWS, Microsoft Azure and Google Cloud?
The Last Watchdog
JUNE 20, 2018
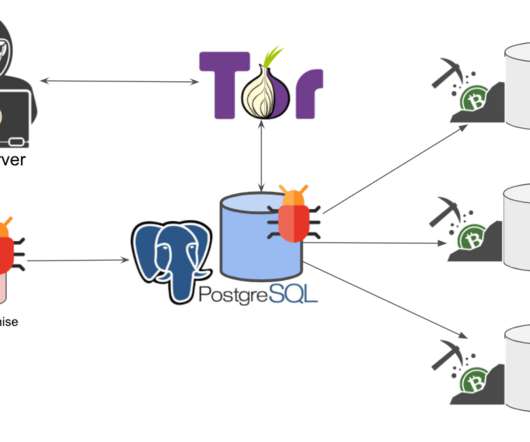
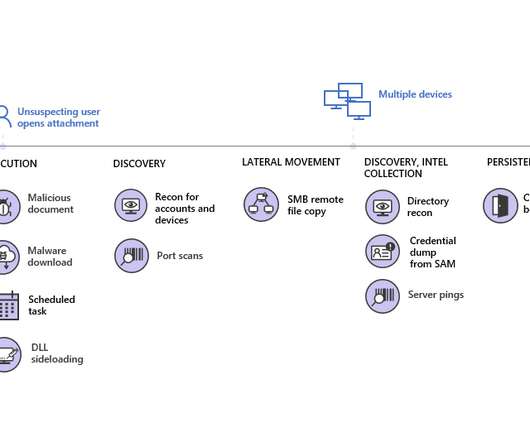
On the face, the damage caused by cryptojacking may appear to be mostly limited to consumers and website publishers who are getting their computing resources diverted to mining fresh units of Monero, Ethereum and Bytecoin on behalf of leeching attackers. Related: Why cryptojacking is more insidious than ransomware. And people would pay that.






































Let's personalize your content