Security Vulnerability of Switzerland’s E-Voting System
Schneier on Security
OCTOBER 17, 2023
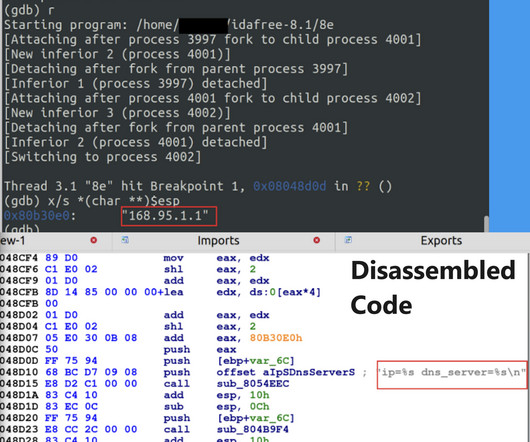
Like any internet voting system, it has inherent security vulnerabilities: if there are malicious insiders, they can corrupt the vote count; and if thousands of voters’ computers are hacked by malware, the malware can change votes as they are transmitted. Here I am saying that in 2004.) Again, the solution is paper.








































Let's personalize your content