Episode 245: How AI is remaking knowledge-based authentication
The Security Ledger
NOVEMBER 1, 2022
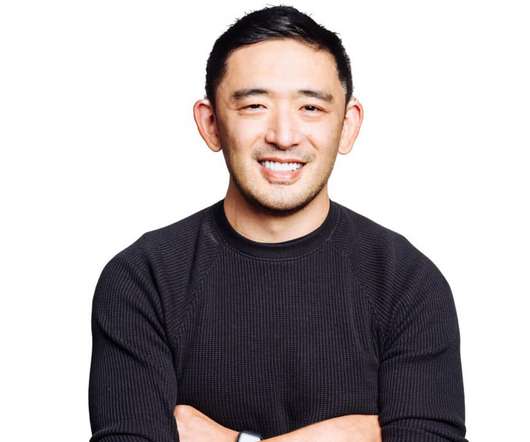
We talk with Matt Salisbury of Honeybadger HQ, which is using AI and machine learning to re-imagine knowledge-based authentication. The post Episode 245: How AI is remaking knowledge-based authentication appeared first on The Security. AI juices knowledge-based authentication. Read the whole entry. »










































Let's personalize your content