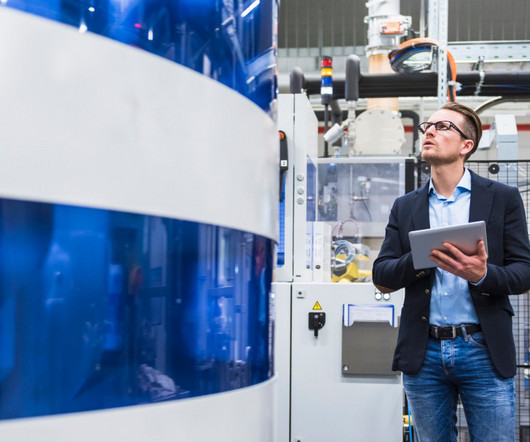
Process Excellence: A transformational lever to extreme automation
IBM Big Data Hub
APRIL 20, 2023
All are transforming their procurement operations by leveraging state-of-the-art process mining and intelligent automation technology. A Process Mining exercise drawing data from enterprise SAP has helped measure KPI performance and define the transformation roadmap. dollars annually in direct or indirect procurement.








































Let's personalize your content