Hardware Vulnerability in Apple’s M-Series Chips
Schneier on Security
MARCH 28, 2024
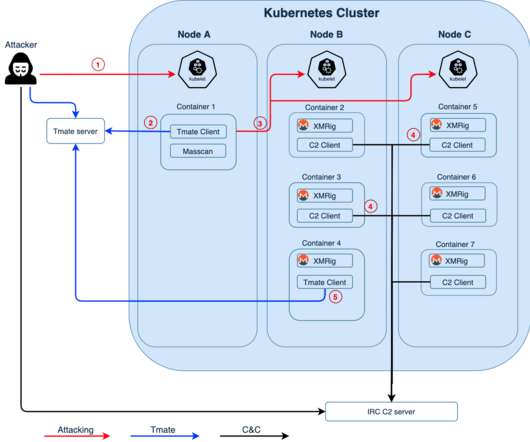
The M1, for example, has two clusters: one containing four efficiency cores and the other four performance cores. As long as the GoFetch app and the targeted cryptography app are running on the same performance cluster—even when on separate cores within that cluster—GoFetch can mine enough secrets to leak a secret key.










































Let's personalize your content