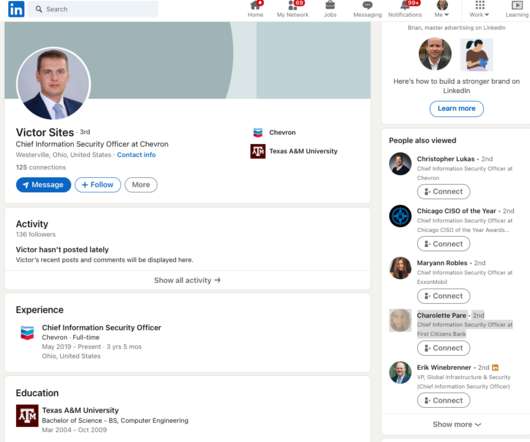
Fake CISO Profiles on LinkedIn Target Fortune 500s
Krebs on Security
SEPTEMBER 30, 2022
Someone has recently created a large number of fake LinkedIn profiles for Chief Information Security Officer (CISO) roles at some of the world’s largest corporations. It’s not clear who’s behind this network of fake CISOs or what their intentions may be. But the fabricated LinkedIn identities are confusing search engine results for CISO roles at major companies, and they are being indexed as gospel by various downstream data-scraping sources.



































Let's personalize your content