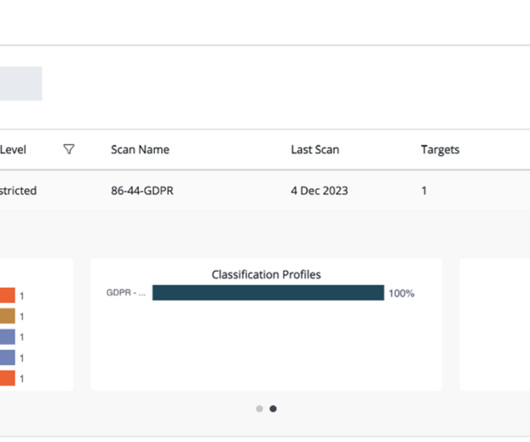
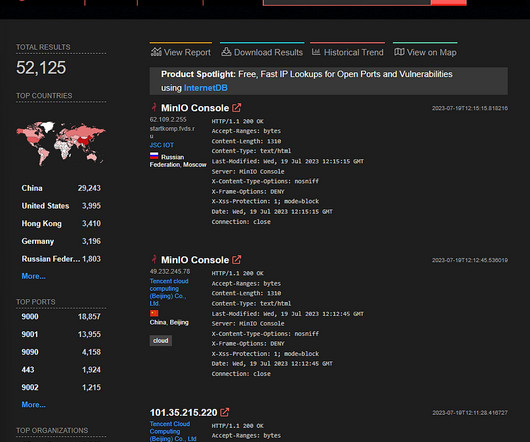
Play ransomware attack on Xplain exposed 65,000 files containing data relevant to the Swiss Federal Administration.
Security Affairs
MARCH 8, 2024
The ransomware attack on Xplain impacted tens of thousands Federal government files, said the National Cyber Security Centre (NCSC) of Switzerland. The National Cyber Security Centre (NCSC) published a data analysis report on the data breach resulting from the ransomware attack on the IT services provider Xplain.







































Let's personalize your content