US Government And Allies Disrupt Massive Russian Botnet
Data Breach Today
JUNE 18, 2022
Botnet Targets IoT And Android Devices; Industrial Control Systems And Computers The U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
JUNE 18, 2022
Botnet Targets IoT And Android Devices; Industrial Control Systems And Computers The U.S.

Armstrong Archives
APRIL 29, 2022
The terms “digital” and “electronic” are often used interchangeably these days, including when it comes to talking about records management. Digital Vs. Electronic Records – FAQs and Differences To understand the differences between digital and electronic records, let’s define each of them and look at the uses of each.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Armstrong Archives
APRIL 29, 2022
The terms “digital” and “electronic” are often used interchangeably these days, including when it comes to talking about records management. Digital Vs. Electronic Records – FAQs and Differences. To understand the differences between digital and electronic records, let’s define each of them and look at the uses of each.

IBM Big Data Hub
DECEMBER 8, 2023
Simultaneously, onboard electronics evolve from individual electronic control units to high-performance computers with higher performance and simplified integration. The SDV separates hardware from software, allowing for updates and upgrades, automation or autonomy and constant connectivity.

The Last Watchdog
FEBRUARY 27, 2024
For this reason, the industry has been investing heavily in nanomaterials like carbon nanotube, graphene and TMDs, which are expected to enable chips with unprecedented functionality. Jung Seoho Jung, Co-founder and CEO at Chiral commented : “At Chiral, we are pioneering the next generation of electronic devices across industry.

Thales Cloud Protection & Licensing
AUGUST 5, 2019
Preparing for Data Security in the Quantum Computing Era. Each passing day brings the world closer to the exciting reality of powerful quantum computing. Quantum computing is a threat to public key infrastructure and security systems that rely on it. Waiting until quantum computing is widely available ?

Everteam
APRIL 4, 2019
While everyone is digging deep into the Artificial Intelligence, Machine Learning, Blockchain and many other new digital transformation phenomena, Quantum Computing has been transformed from theory to reality. Let’s move to how it’s related to computers. What is Quantum Computing? A Quick Quantum look. Too much physics?

John Battelle's Searchblog
JANUARY 8, 2014
The post The Four Phases of CES: I, Consumer, Am Electronic appeared first on John Battelle's Search Blog. CES is a huge event, one that almost everybody in our industry has been to at least once, if not multiple times. Call that the first incarnation of CES – literally, electronics for consumers.

IBM Big Data Hub
APRIL 5, 2024
Many industries rely on high-performance computing (HPC) to achieve this goal. For example, HPC offers high levels of computational power and scalability, crucial for running performance-intensive workloads. In the era of gen AI and hybrid cloud, IBM Cloud® HPC brings the computing power organizations need to thrive.

Krebs on Security
OCTOBER 28, 2020
Department of Homeland Security hastily assembled a conference call with healthcare industry executives warning about an “imminent cybercrime threat to U.S. based Sky Lakes Medical Center’s computer systems. Lawrence Health System led to computer infections at Caton-Potsdam, Messena and Gouverneur hospitals.

Security Affairs
OCTOBER 17, 2018
Yoroi security firm uncovered a targeted attack against one of the most important companies in the Italian Naval Industry leveraging MartyMcFly Malware. I am a computer security scientist with an intensive hacking background. I do have a MD in computer engineering and a PhD on computer security from University of Bologna.

IBM Big Data Hub
FEBRUARY 22, 2024
While AI can undoubtedly offer a competitive edge to organizations that effectively leverage its capabilities, we have seen unique concerns from industry to industry and region to region that must be considered—particularly around data. We believe this is particularly important with the rise of generative AI.

Thales Cloud Protection & Licensing
SEPTEMBER 12, 2018
The Internet of Things (IoT) is rapidly growing and expected to affect all industry verticals as well as our private lives. In this blog, we reached out to our technology partner Nexus to better understand the challenges that the industry faces to ensure safe deployment and management of IoT technologies. Weak authentication.

Security Affairs
JULY 26, 2023
Swedish software firm Ortivus suffered a cyberattack that has resulted in at least two British ambulance services losing access to electronic patient records. Two British ambulance services were not able to access electronic patient records after a cyber attack that hit their software provider Ortivus. ” reads the advisory.

Security Affairs
JULY 23, 2021
Estonian hacker Pavel Tsurkan has pleaded guilty in a United States court to the counts of computer fraud and of creating and operating a proxy botnet. The Estonian national Pavel Tsurkan has pleaded guilty in a United States court to two counts of computer fraud and abuse. ” reads the press release published by DoJ. . .

Krebs on Security
MAY 30, 2019
Section 8 involves the surreptitious installation of computer programs on computers or networks including malware and spyware. “CASL defines spam as commercial electronic messages without consent or the installation of software without consent or the intercepting of electronic messages,” Barratt said.
Security Affairs
DECEMBER 15, 2023
” The Snatch ransomware was first spotted at the end of 2019, Sophos researchers discovered a piece of the Snatch ransomware that reboots computers it infects into Safe Mode to bypass resident security solutions. HENSOLDT is a company specializing in military and defense electronics. ” reads the alert.

The Last Watchdog
JANUARY 24, 2023
These often come as unsolicited phone calls or computer notifications and might sound convincing and well-intentioned, claiming they can solve all the vulnerabilities in the electronics if recipients buy the report. About the essayist: Zac Amos writes about cybersecurity and the tech industry, and he is the Features Editor at ReHack.

AIIM
MAY 28, 2020
Using such algorithms can free up entire departments, and certain tasks can then be delegated to automated computer processing. From the simplest to the most complex applications, automation is also paving the way for better customer service across industries. Customer Service.

Security Affairs
JUNE 18, 2022
The RSOCKS was composed of millions of compromised computers and other electronic devices around the world, including industrial control systems, time clocks, routers, audio/video streaming devices, and smart garage door openers. “The U.S. ” reads the announcement published by DoJ.

Rocket Software
JUNE 2, 2022
FTP servers need to be set up on computer hardware in the DMZ of a company, usually by IT people. Powered by two decades of hands-on EDI expertise across multiple industries. . Cost of Ownership . Then, usernames and passwords need to be distributed so users can access shared and/or dedicated folders. Improve productivity. .

IBM Big Data Hub
AUGUST 1, 2023
Whether it’s addressing customer demands for seamless digital experiences or helping clients navigate complex industry regulations, IBM Cloud is committed to helping clients drive innovation today while preparing them for tomorrow.

Krebs on Security
FEBRUARY 1, 2019
In the United Kingdom, police have seized more than 60 personal electronic devices from a number of Webstresser users, and some 250 customers of the service will soon face legal action, Europol said in a statement released this week. Now, those same authorities are targeting people who paid the service to conduct attacks. According to U.S.

Security Affairs
SEPTEMBER 13, 2021
Olympus issued a statement to announce that its European, Middle East and Africa computer network was hit by a ransomware attack. BlackMatter ransomware operators announced that they will not target healthcare organizations, critical infrastructure, organizations in the defense industry, and non-profit companies.

DLA Piper Privacy Matters
FEBRUARY 15, 2022
Under Section 702, the US Attorney General and Director of National Intelligence may issue directives compelling US electronic communication service providers (ECSPs) to provide such information. An ECS is defined as any service which provides to users the ability to send or receive wire or electronic communications.

eDiscovery Daily
APRIL 9, 2019
Cellebrite recently conducted an industry trends survey targeting Law Enforcement and reported the results in their 2019 Report on Industry Trends for Law Enforcement (link to download the free report available here , hat tip to Rob Robinson’s Complex Discovery site for the reference ).

The Last Watchdog
MAY 23, 2022
Related: Leveraging PKI to advance electronic signatures. It used to be that trusting the connection between a workstation and a mainframe computer was the main concern. We also must find ways to encourage high levels of compliance with industry standards and government regulations.

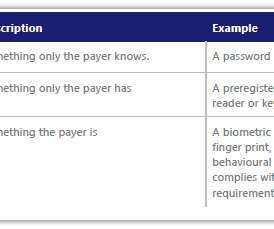
IT Governance
JULY 14, 2022
Organisations that fall within Levels 2–4 of the PCI DSS (Payment Card Industry Data Security Standard) can attest to compliance with an SAQ (self-assessment questionnaire). Dial-out terminals are electronic machines that use chip and PIN and swipe cards, or require users to manually key in information.

Information Management Resources
JANUARY 24, 2020
The firm's quarterly sales and profit forecast was in line with estimates, indicating that demand from electronics makers is poised to improve amid progress resolving the China-U.S. trade dispute.

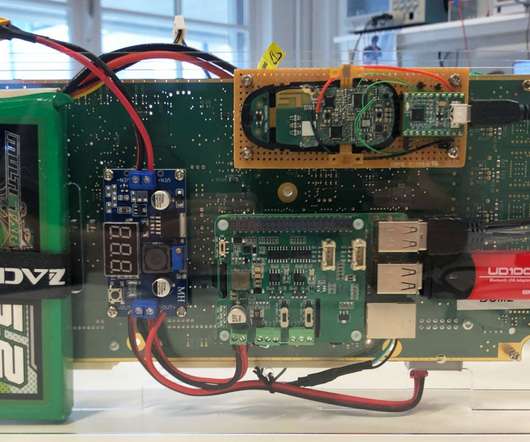
IBM Big Data Hub
NOVEMBER 10, 2023
Semiconductors act as the secret powerhouse behind various industries, from healthcare to manufacturing to financial services. As semiconductor manufacturers strive to keep up with customer expectations, electronic design automation (EDA) tools are the keys to unlocking the solution.

IBM Big Data Hub
FEBRUARY 5, 2024
Furthermore, the integration and support of computer programming in the modelling tool helped us to implement complex features of the thermomix.” “In the past, we used other industry tools, but they were very limited,” says A/Prof Paw.

The Security Ledger
MARCH 26, 2021
In this week’s Security Ledger Podcast, sponsored by Trusted Computing Group, we’re talking about securing the hardware supply chain. In this week’s Security Ledger Podcast, sponsored by Trusted Computing Group, we’re talking about securing the hardware supply chain. When we think about cyber threats to the hardware supply chain, we.

IBM Big Data Hub
MAY 6, 2024
Industry analysts report that dropout rates in phase 3 clinical trials can sometimes reach 20% to 30%. Computer vision models, such as convolutional neural network models, can assist doctors in detecting and classifying diseases in 2D and 3D medical images. This knowledge gap is even more pronounced among minority populations.

Information Governance Perspectives
JANUARY 29, 2024
Health Information Technology (HIT) is the application of information processing involving computer hardware and software that deals with storing, retrieving, sharing, and using healthcare information, data, and knowledge for communication and decision-making. Their “Health Information Ecosystem” strategy recognizes industry limitations.

Security Affairs
OCTOBER 28, 2020
Steelcase is a US-based furniture company that produces office furniture, architectural and technology products for office environments and the education, health care and retail industries. Bleeping Computer, citing a source in the cybersecurity industry, confirmed that Steelcase suffered a Ryuk ransomware attack.

IBM Big Data Hub
JULY 27, 2023
In today’s competitive business landscape, having high compute power can be critical. The solution also includes security and controls built into the platform and is designed to allow clients across industries to consume HPC as a fully managed service while helping them address third- and fourth-party risks.
Krebs on Security
JANUARY 8, 2024
In 2020, the United States brought charges against four men accused of building a bulletproof hosting empire that once dominated the Russian cybercrime industry and supported multiple organized cybercrime groups. All four pleaded guilty to conspiracy and racketeering charges. The Spamdot admins went by the nicknames Icamis (a.k.a.

Security Affairs
FEBRUARY 6, 2019
I am a computer security scientist with an intensive hacking background. I do have a MD in computer engineering and a PhD on computer security from University of Bologna. I do have experience on security testing since I have been performing penetration testing on several US electronic voting systems. Hope you enjoy it!

IBM Big Data Hub
OCTOBER 31, 2023
Electronic design automation (EDA) is a market segment consisting of software, hardware and services with the goal of assisting in the definition, planning, design, implementation, verification and subsequent manufacturing of semiconductor devices (or chips). The primary providers of this service are semiconductor foundries or fabs.

Security Affairs
FEBRUARY 18, 2019
I am a computer security scientist with an intensive hacking background. I do have a MD in computer engineering and a PhD on computer security from University of Bologna. I do have experience in security testing since I have been performing penetration testing on several US electronic voting systems.
Thales Cloud Protection & Licensing
JANUARY 26, 2021
This largely follows the trend in the industry of moving transactions primarily to a more web-focused infrastructure. Figure 1: Web application breaches in the Retail industry. The banking and finance industry is taking proactive steps to secure online and contactless transactions. Source: Verizon DBIR 2020.

Lenny Zeltser
JUNE 2, 2018
Computer security, perhaps? If we examine the factors that influence our desire to use one security title over the other, we’ll better understand the nature of the industry and its driving forces. Are you in cybersecurity? Information security? Yet, the term cybersecurity is growing in popularity.

eSecurity Planet
AUGUST 4, 2022
Encryption technology has evolved over the years to cover data in use, and the emerging power of quantum computing has given rise to quantum cryptography. The advent of quantum computing has given them far more juice to crack traditional encryption methods. This adds a vital extra layer of security. New Quantum Encryption Standards.
Security Affairs
NOVEMBER 23, 2020
A team of researchers from the Computer Security and Industrial Cryptography (COSIC) group at the KU Leuven University in Belgium has demonstrated how to steal a Tesla Model X in minutes by exploiting vulnerabilities in the car’s keyless entry system.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content