Deployable architecture on IBM Cloud: Simplifying system deployment
IBM Big Data Hub
APRIL 22, 2024
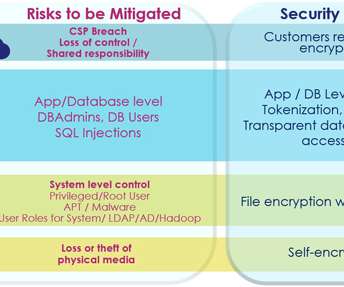
This allows for easier management and reduces the risk of dependencies causing deployment issues. Resilience : Deployable architecture is designed to be resilient, with built-in redundancy and failover mechanisms that ensure the system remains available even in the event of a failure or outage.







































Let's personalize your content