Hackers Steal Credit Card Data of Deal-Seeking Shoppers
Data Breach Today
MAY 10, 2024
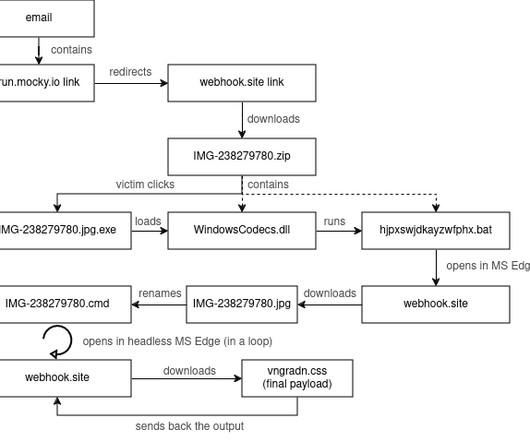
China-Linked Criminals Processed Orders Worth $50M: Security Research Labs Hackers linked to Chinese fraudsters are targeting online shoppers to steal credit card information, likely making off with about $50 million from victims in the United States and Western Europe who order premium shoes at discount prices on fraudulent deal websites.































Let's personalize your content