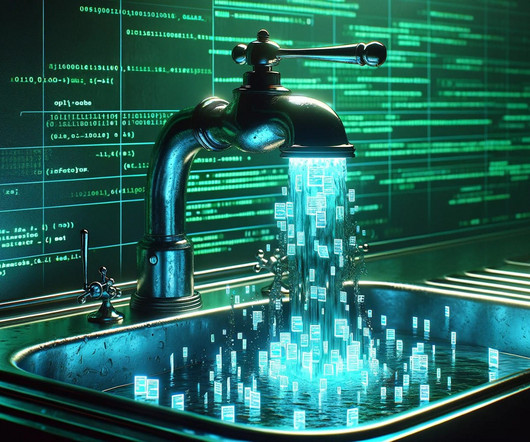
Recent ‘MFA Bombing’ Attacks Targeting Apple Users
Krebs on Security
MARCH 26, 2024
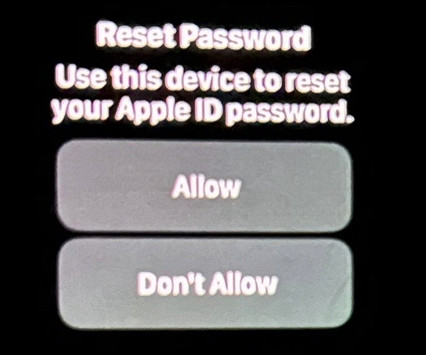
Several Apple customers recently reported being targeted in elaborate phishing attacks that involve what appears to be a bug in Apple’s password reset feature. “It was like this system notification from Apple to approve [a reset of the account password], but I couldn’t do anything else with my phone. .”































Let's personalize your content