US CISA Aims to Expand Automated Malware Analysis Support
Data Breach Today
APRIL 10, 2024
US Cyber Defense Agency Scales Next-Generation Malware Analysis Platform The U.S.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
APRIL 10, 2024
US Cyber Defense Agency Scales Next-Generation Malware Analysis Platform The U.S.

The Last Watchdog
JUNE 23, 2023
June 22, 2023 — Dasera , the premier automated data security and governance platform for top-tier finance, healthcare, and technology enterprises, is thrilled to unveil “Ski Lift,” a complimentary platform exclusively designed for Snowflake users.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
MARCH 15, 2022
The ISMG Security Report features an analysis of the U.S. government's request for billions of dollars in tech aid to curb the global impact of the Kremlin's campaign in Ukraine. It also examines Biden's cryptocurrency executive order and why breached organizations often don't share full details.

Security Affairs
FEBRUARY 16, 2024
CISA revealed that threat actors breached an unnamed state government organization via an administrator account belonging to a former employee. The government experts conducted an incident response assessment of the state government organization after its documents were posted on the dark web.

Collibra
JANUARY 9, 2024
In today’s world, data drives many of the decisions made by federal and state government agencies. Recently many agencies have started to discuss how data mesh strategies, focused on a decentralized data landscape and distributed domain-oriented data products, can help make better use of data and speed up decision making.
Security Affairs
APRIL 24, 2024
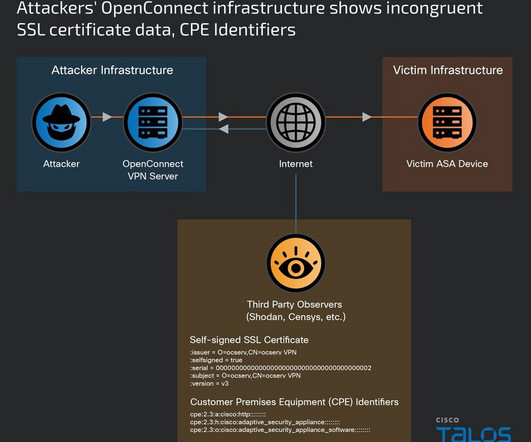
Nation-state actor UAT4356 has been exploiting two zero-days in ASA and FTD firewalls since November 2023 to breach government networks. Early in 2024, a customer contacted Cisco to report a suspicious related to its Cisco Adaptive Security Appliances (ASA). Cisco Talos researchers tracked this cyber-espionage campaign as ArcaneDoor.

erwin
SEPTEMBER 3, 2020
Why should you integrate data governance (DG) and enterprise architecture (EA)? Data governance provides time-sensitive, current-state architecture information with a high level of quality. Data governance provides time-sensitive, current-state architecture information with a high level of quality.

erwin
OCTOBER 31, 2019
Do you know where your data is? What data you have? Add to the mix the potential for a data breach followed by non-compliance, reputational damage and financial penalties and a real horror story could unfold. s Information Commissioner’s Office had levied against both Facebook and Equifax for their data breaches.

erwin
APRIL 2, 2021
Organizations are managing more data than ever. With more companies increasingly migrating their data to the cloud to ensure availability and scalability, the risks associated with data management and protection also are growing. Data Security Starts with Data Governance.

Security Affairs
MARCH 8, 2024
The ransomware attack on Xplain impacted tens of thousands Federal government files, said the National Cyber Security Centre (NCSC) of Switzerland. The National Cyber Security Centre (NCSC) published a data analysis report on the data breach resulting from the ransomware attack on the IT services provider Xplain.

Security Affairs
APRIL 8, 2024
Greylock McKinnon Associates, a service provider for the Department of Justice, suffered a data breach that exposed data of 341650 people. GMA disclosed a data breach that impacted medicare and other information belonging to 5465 people. The data breach occurred on May 30, 2023, and was discovered on February 7, 2024.

Security Affairs
AUGUST 26, 2021
Cybersecurity and Infrastructure Security Agency (CISA) released five malware analysis reports (MARs) related to samples found on compromised Pulse Secure devices. CISA published five malware analysis reports (MARs) related to samples found on compromised Pulse Secure devices. v1: Pulse Connect Secure.

Data Breach Today
NOVEMBER 8, 2019
The latest edition of the ISMG Security Report offers an analysis of how Twitter allegedly was used to spy on critics of the Saudi Arabian government. Also featured: A preview of the new NIST Privacy Framework and an update on business email compromise attacks.
Security Affairs
AUGUST 9, 2022
Cyber Security Specialist Zoziel Pinto Freire shows an example of malicious file analysis presented during his lecture on BSides-Vitória 2022. My objective with this series of articles is to show examples of malicious file analysis that I presented during my lecture on BSides-Vitória 2022. Static Analysis x Dynamic Analysis.

erwin
OCTOBER 8, 2020
So if you’re going to move from your data from on-premise legacy data stores and warehouse systems to the cloud, you should do it right the first time. And as you make this transition, you need to understand what data you have, know where it is located, and govern it along the way. Then you must bulk load the legacy data.

eSecurity Planet
AUGUST 9, 2022
Regulatory compliance and data privacy issues have long been an IT security nightmare. And since the EU’s General Data Protection Regulation (GDPR) took effect May 25, 2018, IT compliance issues have been at the forefront of corporate concerns. GDPR-style data privacy laws came to the U.S.
Collibra
OCTOBER 30, 2020
Data quality and data governance are both indispensable for organizations that want to become Data Intelligent enterprises. Data quality and data governance are certainly related, but they are two separate disciplines. The difference between data quality and data governance.
Data Breach Today
JANUARY 31, 2020
The latest edition of the ISMG Security Report discusses the ramifications of the U.K's decision to allow limited use of Huawei's equipment in 5G networks. Plus: Updates on Wawa's stolen card offered for sale and nascent security threats from social networks and drones.
Security Affairs
NOVEMBER 16, 2023
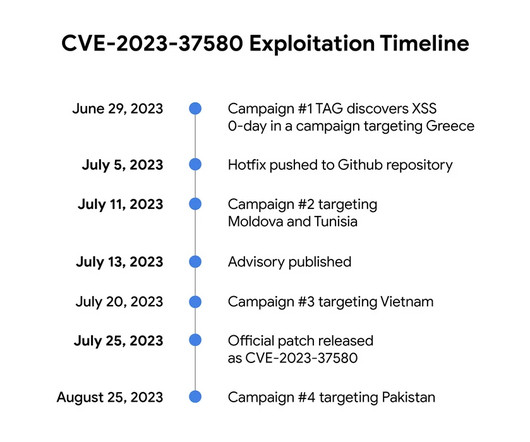
Google TAG revealed that threat actors exploited a Zimbra Collaboration Suite zero-day ( CVE-2023-37580 ) to steal emails from governments. The first campaign aimed at a government organization in Greece, threat actors sent emails containing exploit urls to their targets. ” continues the report. .”

erwin
SEPTEMBER 19, 2019
Data governance isn’t a one-off project with a defined endpoint. Data governance, today, comes back to the ability to understand critical enterprise data within a business context, track its physical existence and lineage, and maximize its value while ensuring quality and security.

erwin
MARCH 25, 2021
erwin recently hosted the second in its six-part webinar series on the practice of data governance and how to proactively deal with its complexities. Led by Frank Pörschmann of iDIGMA GmbH, an IT industry veteran and data governance strategist, the second webinar focused on “ The Value of Data Governance & How to Quantify It.”.

Security Affairs
DECEMBER 27, 2021
Albania’s prime minister Edi Rama apologized for the massive leak of personal records from a government database of state. Albania’s prime minister this week apologized for the massive leak of personal records from a government database of state. Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini.
Krebs on Security
MAY 12, 2022
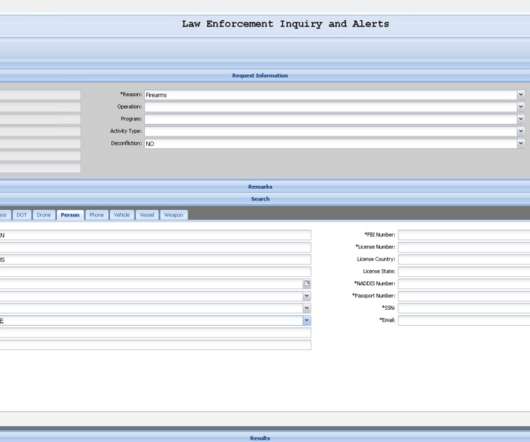
KrebsOnSecurity has learned the alleged compromise is tied to a cybercrime and online harassment community that routinely impersonates police and government officials to harvest personal information on their targets. “Law Enforcement Inquiry and Alerts (LEIA) allows for a federated search of 16 Federal law enforcement databases.”

Security Affairs
FEBRUARY 26, 2024
Recently the leak of a collection of files apparently stolen from the Chinese government hacking contractor, I-Soon, exposed Chinese hacking capabilities. An analyst based in Taiwan, known as Azaka, discovered the data leak and shared their findings on social media. ” reads an analysis published by SentinelOne.

erwin
NOVEMBER 6, 2019
erwin released its State of Data Governance Report in February 2018, just a few months before the General Data Protection Regulation (GDPR) took effect. Download Free GDPR Guide | Step By Step Guide to Data Governance for GDPR?. How to automate data mapping. The Role of Data Automation.

eSecurity Planet
APRIL 12, 2024
Data loss prevention (DLP) best practices are principles that help prevent intentional or unintentional data erasure. By following these guidelines, organizations can reduce the detrimental impact of data loss and quickly resume operations after an incident. Proofpoint’s 2024 data loss landscape report reveals 84.7%

IT Governance
SEPTEMBER 7, 2023
This week, we discuss security issues at the Electoral Commission, Meta’s appeal against daily GDPR fines, and a breach affecting 10 million users of the French unemployment agency Pôle emploi. Transcript: Hello and welcome to the IT Governance podcast for Friday, 8 September 2023. The fines are due to continue until 3 November.

Data Breach Today
FEBRUARY 11, 2020
Analysis: Equifax Failed on Security, But Only Governments Can Hold Each Other to Account Who's surprised Chinese military hackers allegedly hacked Equifax?

Schneier on Security
NOVEMBER 21, 2023
Google’s Threat Analysis Group announced a zero-day against the Zimbra Collaboration email server that has been used against governments around the world. TAG has observed four different groups exploiting the same bug to steal email data, user credentials, and authentication tokens. It has been patched.
Data Breach Today
OCTOBER 22, 2021
The latest edition of the ISMG Security Report features an analysis of whether businesses are stepping up their ransomware defenses in response to several warnings released by the U.S. governments highlighting the threat posed to infrastructure. Also featured are the Thingiverse data breach and airline fraud trends.

IBM Big Data Hub
FEBRUARY 5, 2024
For federal and state governments and agencies, identity is the crux of a robust security implementation. Numerous individuals disclose confidential, personal data to commercial and public entities daily, necessitating that government institutions uphold stringent security measures to protect their assets.
Security Affairs
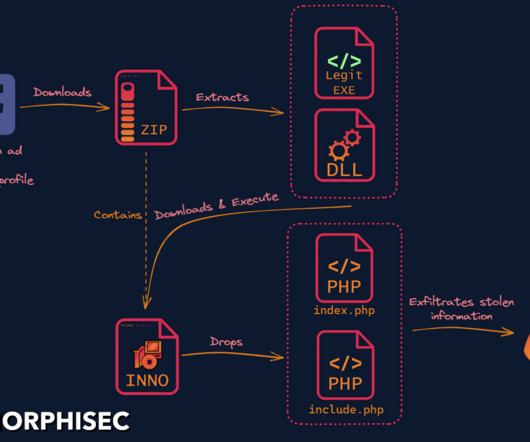
MARCH 7, 2023
Researchers discovered a new info stealer dubbed SYS01 stealer targeting critical government infrastructure and manufacturing firms. ” reads the analysis published by Morphisec. The attack is designed to steal sensitive information, including login data, cookies, and Facebook ad and business account information.”
Security Affairs
MARCH 24, 2024
Every week the best security articles from Security Affairs are free for you in your email box. Government’s Antitrust Case Against Apple Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, Ramadan )

IT Governance
OCTOBER 24, 2023
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. Publicly disclosed data breaches and cyber attacks City of Philadelphia discloses data breach after five months Date of breach: 24 May 2023 ( notice issued 20 October 2023).

Hunton Privacy
FEBRUARY 15, 2024
Recent developments in the Shanghai Pilot Free Trade Zone to facilitate cross-border data transfers are expected to provide greater flexibility in exporting data from China, which has been stymied by the Cyberspace Administration of China (“CAC”)’s strict cross-border data transfer regulations proposed in December 2023.

Collibra
APRIL 7, 2022
Data governance is important because it brings meaning to an organization’s data. It adds trust and understanding to an organization’s data through stewardship and a robust business glossary, thus accelerating digital transformation across the enterprise. . Why is data governance important?

Collibra
JANUARY 1, 2021
Creating a data governance framework is crucial to becoming a data-driven enterprise because data governance brings meaning to an organization’s data. It adds trust and understanding to data, accelerating digital transformation across the enterprise. What is a data governance framework?

erwin
JULY 12, 2019
In light of recent, high-profile data breaches, it’s past-time we re-examined strategic data governance and its role in managing regulatory requirements. for alleged violations of the European Union’s General Data Protection Regulation (GDPR). Govern PII “at rest”. Govern PII “in motion”. Complexity.

AIIM
SEPTEMBER 12, 2018
Data Privacy and Open Data: Secondary Uses under GDPR. Mitigate Data Privacy and Security Risks with Machine Learning. The Privacy and Security Dichotomy. GDPR and Cross Border Data Flows between the EU and the US: Current State of the Law. GDPR Compliance Starts with Data Discovery.

IT Governance
NOVEMBER 6, 2023
At the end of each month, these incidents – and any others that we find – will be used to inform our monthly analysis of data breaches and cyber attacks. When MOVEit was hacked by the Russian Cl0p ransomware gang in May, email addresses and links to government employee surveys were compromised.

Security Affairs
JANUARY 26, 2019
The cyber security expert Marco Ramilli continues its analysis of the data leak known as Collection #1, he shared some interesting views on data The cyber security expert Marco Ramilli continues its analysis of the data leak known as Collection #1, he shared some interesting views on data.

Collibra
MAY 5, 2020
Every business journal has displayed hyperbolic headlines or similar that proclaims, “The Future Is Digital,” “Technology Has Taken Over Our Lives,” or “Data Is the New Oil.” In some ways, this is every data citizen’s dream. Because of this, we are generating data at unprecedented rates. They need data governance. .
Security Affairs
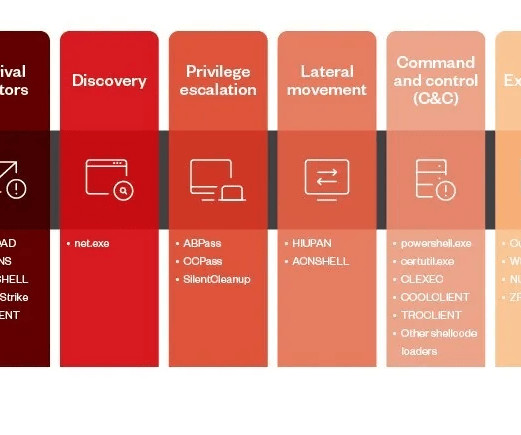
MARCH 27, 2023
China-linked Earth Preta cyberespionage group has been observed adopting new techniques to bypass security solutions. Trend Micro researchers reported that the China-linked Earth Preta group (aka Mustang Panda ) is actively changing its tools, tactics, and procedures (TTPs) to bypass security solutions.

Data Breach Today
JULY 5, 2019
The latest edition of the ISMG Security Report analyzes the debate over whether the government should require technology firms to use weak encryption for messaging applications. Plus, D-Link's proposed settlement with the FTC and a CISO's update on medical device security.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content