Network Security Architecture: Best Practices & Tools
eSecurity Planet
APRIL 26, 2024
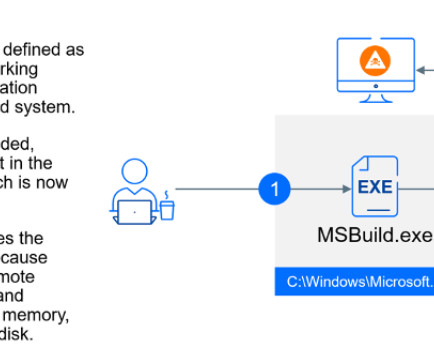
Endpoint: Enables access for human users and computer services and commonly includes PCs, laptops, Internet of Things (IoT), and operational technology (OT). Security Elements Security elements protect each element within the network, network access, and the data transmissions. or segregated as cloud or network attached storage (NAS).








































Let's personalize your content